Knowledge Based Authentication Kba Powerful Verification Based On

Everything You Need To Know About Knowledge Based Authentication This powerful authentication method uses personal information to verify a user’s identity and is increasingly used to protect sensitive data and accounts. but what is kba, and how does it work? and is it as safe as we believe?. Knowledge based authentication [kba] verifies identity by asking questions only the real user should be able to answer. there are two main types of kba: static (pre set questions) & dynamic (questions generated from databases).

Problems 5 Flaws In Knowledge Based Authentication Kba This article is a comprehensive guide on knowledge based authentication (kba). it discusses what it is, how it works and why it’s important. What is knowledge based authentication (kba)? kba verifies a user’s identity by requiring them to answer questions based on personal or account related knowledge. Dynamic kba is a high level of authentication that uses knowledge questions to verify each individual identity but does not require the person to have provided the questions and answers beforehand. Kba is a form of identity verification that relies on the user answering specific questions to confirm their identity. these questions are typically based on personal information that only the legitimate user should know, such as financial or historical data.

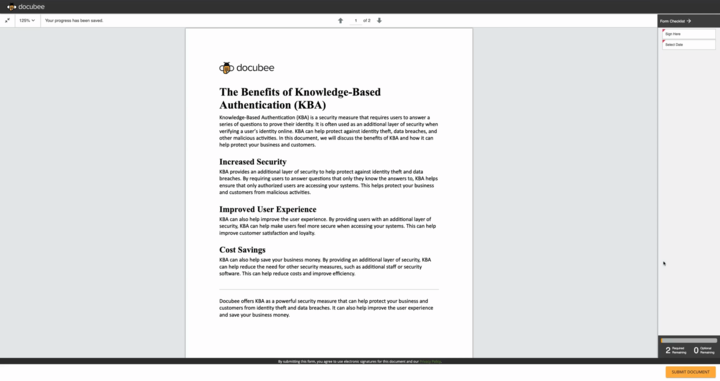
What Is Knowledge Based Authentication Kba Dynamic kba is a high level of authentication that uses knowledge questions to verify each individual identity but does not require the person to have provided the questions and answers beforehand. Kba is a form of identity verification that relies on the user answering specific questions to confirm their identity. these questions are typically based on personal information that only the legitimate user should know, such as financial or historical data. Knowledge based authentication (kba) has emerged as a pivotal tool in bolstering security measures by verifying the identity of users through personalized questions based on private information. Knowledge based authentication (kba) verifies identity through security questions. learn what kba is, how it works, why ai customers are breaking it, and what comes next. Knowledge based authentication (kba) is a security method that verifies your identity by asking questions only you should be able to answer. you encounter it when logging into government portals, applying for credit, accessing medical records, or resetting a password. Although knowledge based authentication (kba) has been utilized, it is now evident that it is insufficient. stronger authentication techniques are required since social engineering, data breaches, and ai driven attacks have exposed kba’s flaws.
Basil Kba Knowledge Based Authentication Knowledge based authentication (kba) has emerged as a pivotal tool in bolstering security measures by verifying the identity of users through personalized questions based on private information. Knowledge based authentication (kba) verifies identity through security questions. learn what kba is, how it works, why ai customers are breaking it, and what comes next. Knowledge based authentication (kba) is a security method that verifies your identity by asking questions only you should be able to answer. you encounter it when logging into government portals, applying for credit, accessing medical records, or resetting a password. Although knowledge based authentication (kba) has been utilized, it is now evident that it is insufficient. stronger authentication techniques are required since social engineering, data breaches, and ai driven attacks have exposed kba’s flaws.
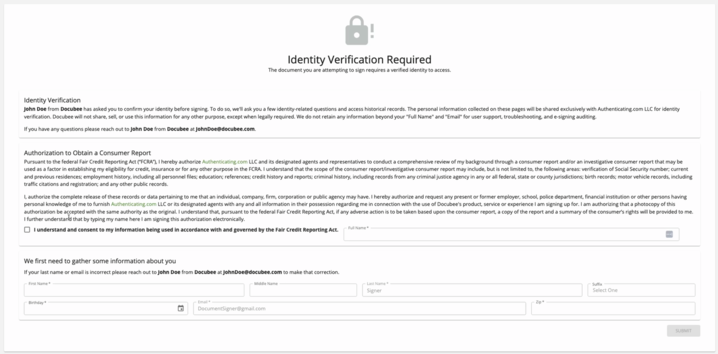
Knowledge Based Authentication Kba Configuration Docubee Knowledge based authentication (kba) is a security method that verifies your identity by asking questions only you should be able to answer. you encounter it when logging into government portals, applying for credit, accessing medical records, or resetting a password. Although knowledge based authentication (kba) has been utilized, it is now evident that it is insufficient. stronger authentication techniques are required since social engineering, data breaches, and ai driven attacks have exposed kba’s flaws.
Knowledge Based Authentication Kba Configuration Docubee
Comments are closed.