Kernel Exploits Tryhackme Linux Privilege Escalation
Tryhackme Linux Privilege Escalation Learn the fundamentals of linux privilege escalation. from enumeration to exploitation, get hands on with over 8 different privilege escalation techniques. Linux privilege escalation, simply put, is gaining higher levels of access on a linux system than you're supposed to have. we start off with launching the box on tryhackme and sshing in using ssh karen@ . we can use the password "password1" to log in.
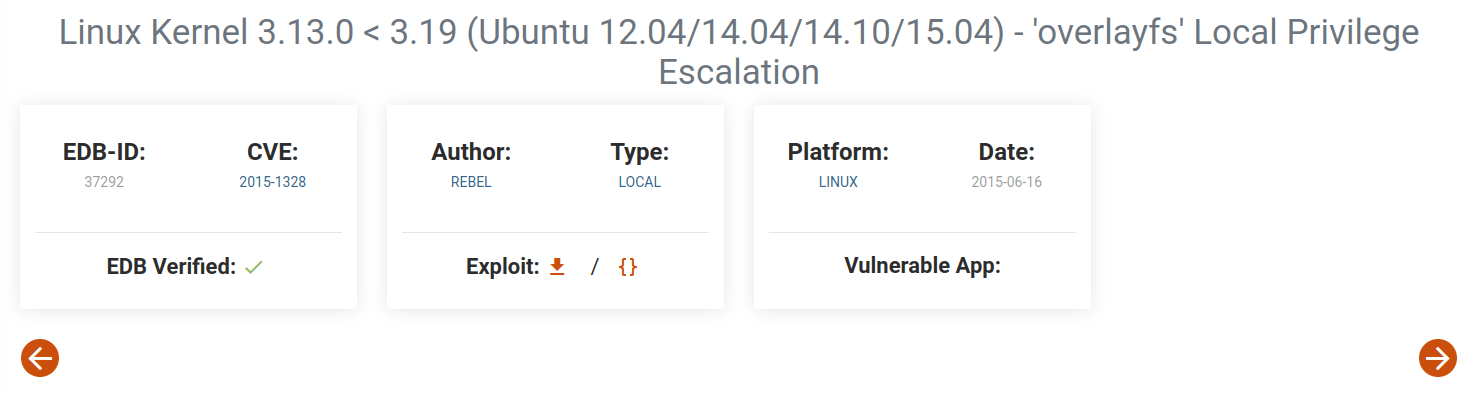
Tryhackme Linux Privilege Escalation In this walkthrough, we’ll explore the kernel exploits section of the linux privilege escalation room on tryhackme. i’ll walk you through the steps i took to escalate privileges on the target machine, and as a blue teamer at heart, i’ll follow up with defensive strategies mapped to the mitre att&ck framework. So one way to do it is to find a known kernel exploit. for find kernel exploit, first we need to get our current kernel version, so we are going to use uname r command (explanation is in. Then we can look for an exploit for this kernel through exploit database for example. now we can either download the file from here or locate it on our machine through the file name. The kernel on linux systems manages the communication between components such as the memory on the system and applications. this critical function requires the kernel to have specific privileges; thus, a successful exploit will potentially lead to root privileges.
Tryhackme Linux Privilege Escalation Then we can look for an exploit for this kernel through exploit database for example. now we can either download the file from here or locate it on our machine through the file name. The kernel on linux systems manages the communication between components such as the memory on the system and applications. this critical function requires the kernel to have specific privileges; thus, a successful exploit will potentially lead to root privileges. Explore the linux privilege escalation room on tryhackme—a must know skill for pentesters and cybersecurity pros. this in depth walkthrough covers it all!. This tryhackme room covers privilege escalation techniques on linux systems. in this activity, we focus on exploiting a kernel vulnerability to gain root access. Sudo versions before 1.9.17p1 (1.9.14 1.9.17 < 1.9.17p1) allows unprivileged local users to escalate their privileges to root via sudo chroot option when etc nsswitch.conf file is used from a user controlled directory. here is a poc to exploit that vulnerability. In this post we will be exploring various kernel exploits that can be used for linux privilege escalation from standard user to root. we will start by using various commands to find the kernel version on the victim host.
Comments are closed.