Kali Linux Tools Arachni Web Application Security Scanner
Arachni Web Application Security Scanner Framework Iemlabs Blog Learn how to install arachni on kali linux with this step by step guide for web vulnerability scanning and security testing. developers and security professionals often need reliable tools to scan web applications for vulnerabilities. Arachni is designed to automatically detect security issues in web applications. all it expects is the url of the target website and after a while it will present you with its findings.

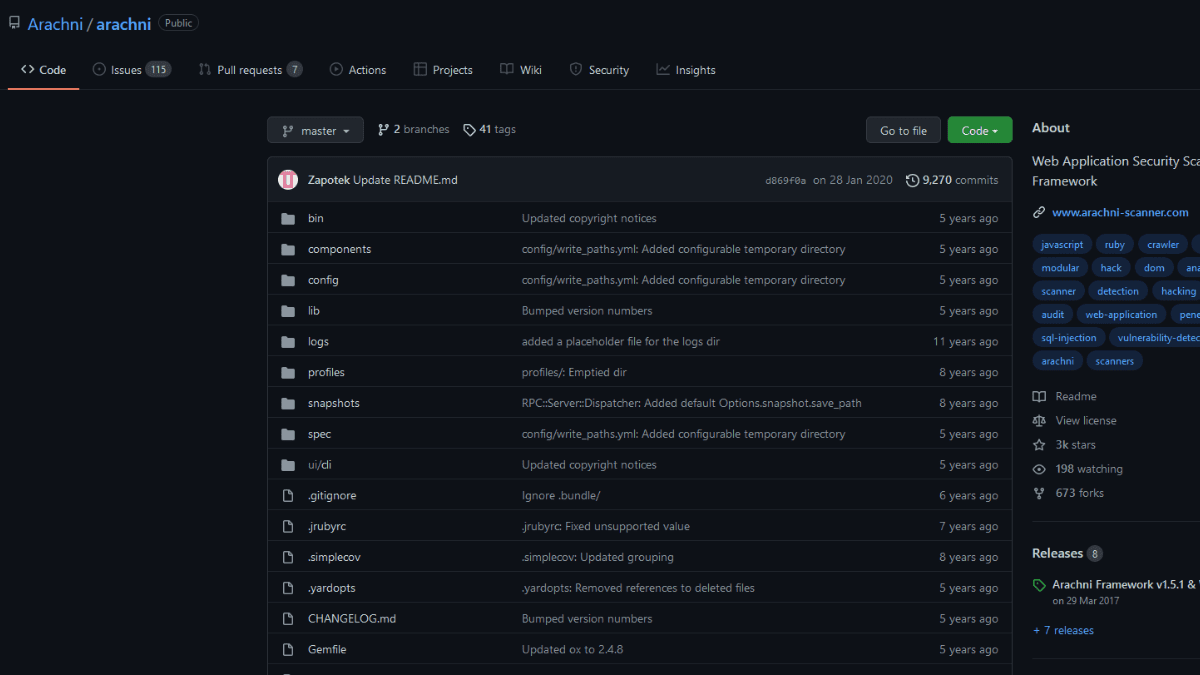
Arachni Web Application Security Scanner Programe Hacking Arachni is a powerful open source web application security scanner that i’ve come to admire for its versatility and thoroughness. when i first started using arachni, i was fascinated by how it automates the scanning process while still allowing for a good deal of customization. Here are five well known web scanner for kali linux, along with their brief descriptions, installation, and usage examples: kali linux is a popular distribution for penetration testing and ethical hacking, and it comes with a wide range of tools for web application scanning. Arachni adalah framework pemindai keamanan aplikasi web yang open source dan berbasis ruby. ia dikembangkan oleh tasos “zapotek” laskos dengan tujuan menyediakan alat otomasi pengujian keamanan. Home of kali linux, an advanced penetration testing linux distribution used for penetration testing, ethical hacking and network security assessments.

Arachni Web Application Security Scanner Programe Hacking Arachni adalah framework pemindai keamanan aplikasi web yang open source dan berbasis ruby. ia dikembangkan oleh tasos “zapotek” laskos dengan tujuan menyediakan alat otomasi pengujian keamanan. Home of kali linux, an advanced penetration testing linux distribution used for penetration testing, ethical hacking and network security assessments. Arachni is an open source, feature full, modular, high performance ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications. The tool searches all the links, forms, cookies, headers, json files, and xml data to find vulnerabilities in the target web application. the potential vulnerabilities are highlighted as they are found during the scanning process. We hope this article provided you with enough insights on the penetration tools you can leverage to ensure the security and integrity of your web applications. Though there are many tools in kali linux for vulnerability analysis here is the list of most used tools. 1. nikto is an open source software written in perl language that is used to scan a web server for vulnerability that can be exploited and can compromise the server.

Arachni Web Application Security Scanner By Mejbaur Bahar Arachni is an open source, feature full, modular, high performance ruby framework aimed towards helping penetration testers and administrators evaluate the security of web applications. The tool searches all the links, forms, cookies, headers, json files, and xml data to find vulnerabilities in the target web application. the potential vulnerabilities are highlighted as they are found during the scanning process. We hope this article provided you with enough insights on the penetration tools you can leverage to ensure the security and integrity of your web applications. Though there are many tools in kali linux for vulnerability analysis here is the list of most used tools. 1. nikto is an open source software written in perl language that is used to scan a web server for vulnerability that can be exploited and can compromise the server.

Web Application Security Scanner In Kali Linux Spaghetti Artofit We hope this article provided you with enough insights on the penetration tools you can leverage to ensure the security and integrity of your web applications. Though there are many tools in kali linux for vulnerability analysis here is the list of most used tools. 1. nikto is an open source software written in perl language that is used to scan a web server for vulnerability that can be exploited and can compromise the server.
Comments are closed.