Jzjsjisjs79832844394 73a7e9e9 25f0 45c3 85f4 Aaa0cd80530b
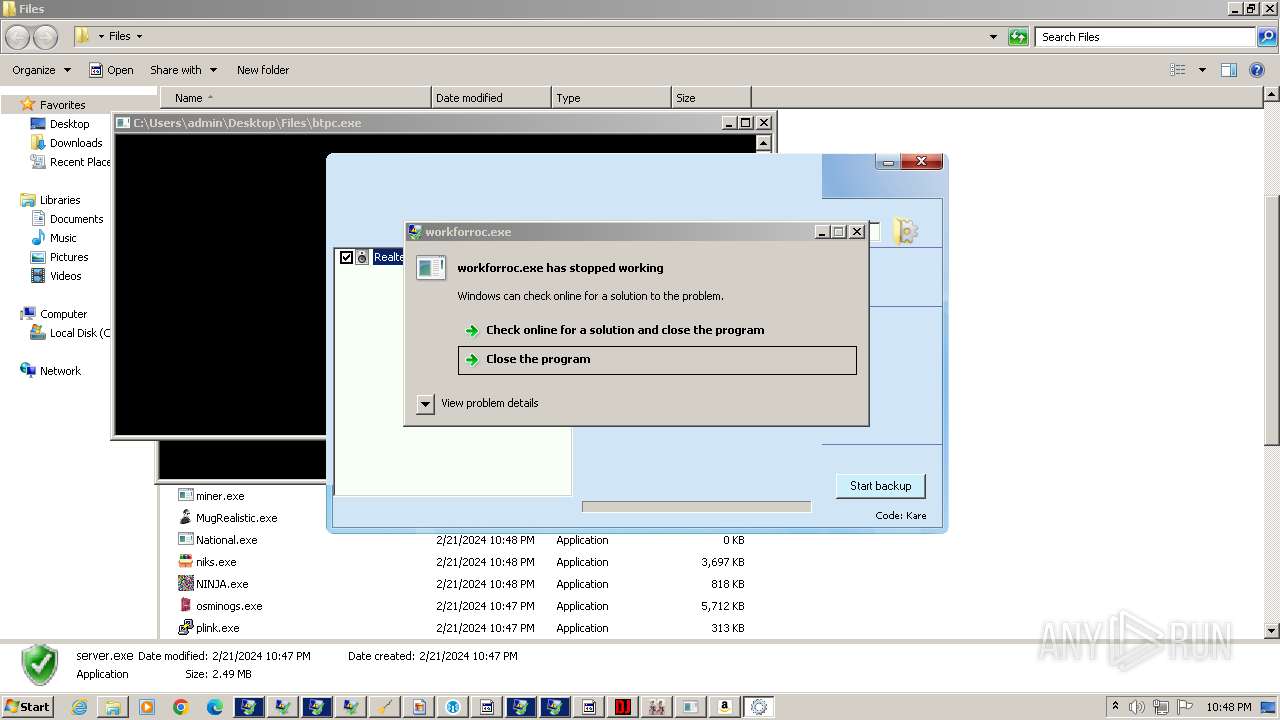
Analysis 4363463463464363463463463 Exe Md5 Enjoy the videos and music you love, upload original content, and share it all with friends, family, and the world on . Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for.
97d6f2a4eaae0cda4c1b0b43163de6f9 Youtube Microsoft bing is a fast, secure, ai powered search engine offering advanced tools for quick and secure information discovery. Since our launch in 1997, google search has continued to evolve to help you find the information you're looking for. explore new ways to search. download the google app to experience lens, ar, search labs, voice search, and more. Google images. the most comprehensive image search on the web. Search with microsoft bing and use the power of ai to find information, explore webpages, images, videos, maps, and more. a smart search engine for the forever curious.

94cc228e6b54004da8cb75ed4f6efd51 Youtube Google images. the most comprehensive image search on the web. Search with microsoft bing and use the power of ai to find information, explore webpages, images, videos, maps, and more. a smart search engine for the forever curious. Join our upcoming webinar on november 6th at 17:00 pm cest and 11:00 am edt where we'll show you how to transform raw intelligence into a dynamic, actionable defense strategy. we’ll start with a real world scenario from google threat intelligence. Meet url decode and encode, a simple online tool that does exactly what it says: decodes from url encoding as well as encodes into it quickly and easily. url encode your data without hassles or decode it into a human readable format. Ekinerja ekinerja. It's common knowledge that the decryption of a "hash" is impossible. this service uses "reverse lookup" via the database to match a hash to its value. our database is around ~3000m records in size and keeps growing. calculate hash! with no changes in a codebase! decode!.

7cddd29f3aee57b87ac2eeb6b5b80867 Youtube Join our upcoming webinar on november 6th at 17:00 pm cest and 11:00 am edt where we'll show you how to transform raw intelligence into a dynamic, actionable defense strategy. we’ll start with a real world scenario from google threat intelligence. Meet url decode and encode, a simple online tool that does exactly what it says: decodes from url encoding as well as encodes into it quickly and easily. url encode your data without hassles or decode it into a human readable format. Ekinerja ekinerja. It's common knowledge that the decryption of a "hash" is impossible. this service uses "reverse lookup" via the database to match a hash to its value. our database is around ~3000m records in size and keeps growing. calculate hash! with no changes in a codebase! decode!.
C4f2cb7f81064a149192644fa573bdd300 06 59 Youtube Ekinerja ekinerja. It's common knowledge that the decryption of a "hash" is impossible. this service uses "reverse lookup" via the database to match a hash to its value. our database is around ~3000m records in size and keeps growing. calculate hash! with no changes in a codebase! decode!.
Comments are closed.