Jwt Structure Cognito
Github Labd Django Cognito Jwt An Authentication Backend For Django Because amazon cognito implements oidc sufficiently close to the public specification, any reputable jwt library in your developer environment of choice can handle your verification requirements. A practical guide to decoding, validating, and verifying aws cognito jwt tokens in your application, including signature verification, claim checks, and common pitfalls.
Github Xeedware Cognito Jwt Typescript Friendly Aws Cognito Dive deep on how amazon cognito issued tokens authorize access to apis and aws resources. a custom web application explores the structure of json web tokens (jwts), including header, payload, and signature verification. After a user logs in, an amazon cognito user pool returns a jwt, which is a base64 encoded json string that contains information about the user (called claims). Complete guide to aws cognito authentication. learn user pools vs identity pools, oauth 2.0 workflows, jwt token validation, and securing apis. Jwt consists of 3 parts: a header, a payload and a signature. the header and the payload contain information about the token and its contents, while the signature is used to verify the integrity.
Github Maximivanov Cognito Jwt Verifier Verify Id And Access Jwt Complete guide to aws cognito authentication. learn user pools vs identity pools, oauth 2.0 workflows, jwt token validation, and securing apis. Jwt consists of 3 parts: a header, a payload and a signature. the header and the payload contain information about the token and its contents, while the signature is used to verify the integrity. We applied these concepts to one of aws's services, cognito, which offers several other strategies beyond the one discussed such as mfa or sso. these practices should help prevent malicious attacks and minimize the risk of fraud, as well as being an efficient way to ensure granular access control for your users. Before we go forward with a complete example let's quickly make sure that we understand the theory behind verifying the signature of a jwt. as we know the jwt contains three sections. You can securely validate jwt tokens issued by aws cognito using the jwx library. this ensures the token’s signature and claims are valid before granting access to your protected resources. When a user signs into your app, amazon cognito verifies the login information. if the login is successful, amazon cognito creates a session and returns an id token, an access token, and a refresh token for the authenticated user.

Cognito Jwt Verifier Travis Wimer We applied these concepts to one of aws's services, cognito, which offers several other strategies beyond the one discussed such as mfa or sso. these practices should help prevent malicious attacks and minimize the risk of fraud, as well as being an efficient way to ensure granular access control for your users. Before we go forward with a complete example let's quickly make sure that we understand the theory behind verifying the signature of a jwt. as we know the jwt contains three sections. You can securely validate jwt tokens issued by aws cognito using the jwx library. this ensures the token’s signature and claims are valid before granting access to your protected resources. When a user signs into your app, amazon cognito verifies the login information. if the login is successful, amazon cognito creates a session and returns an id token, an access token, and a refresh token for the authenticated user.
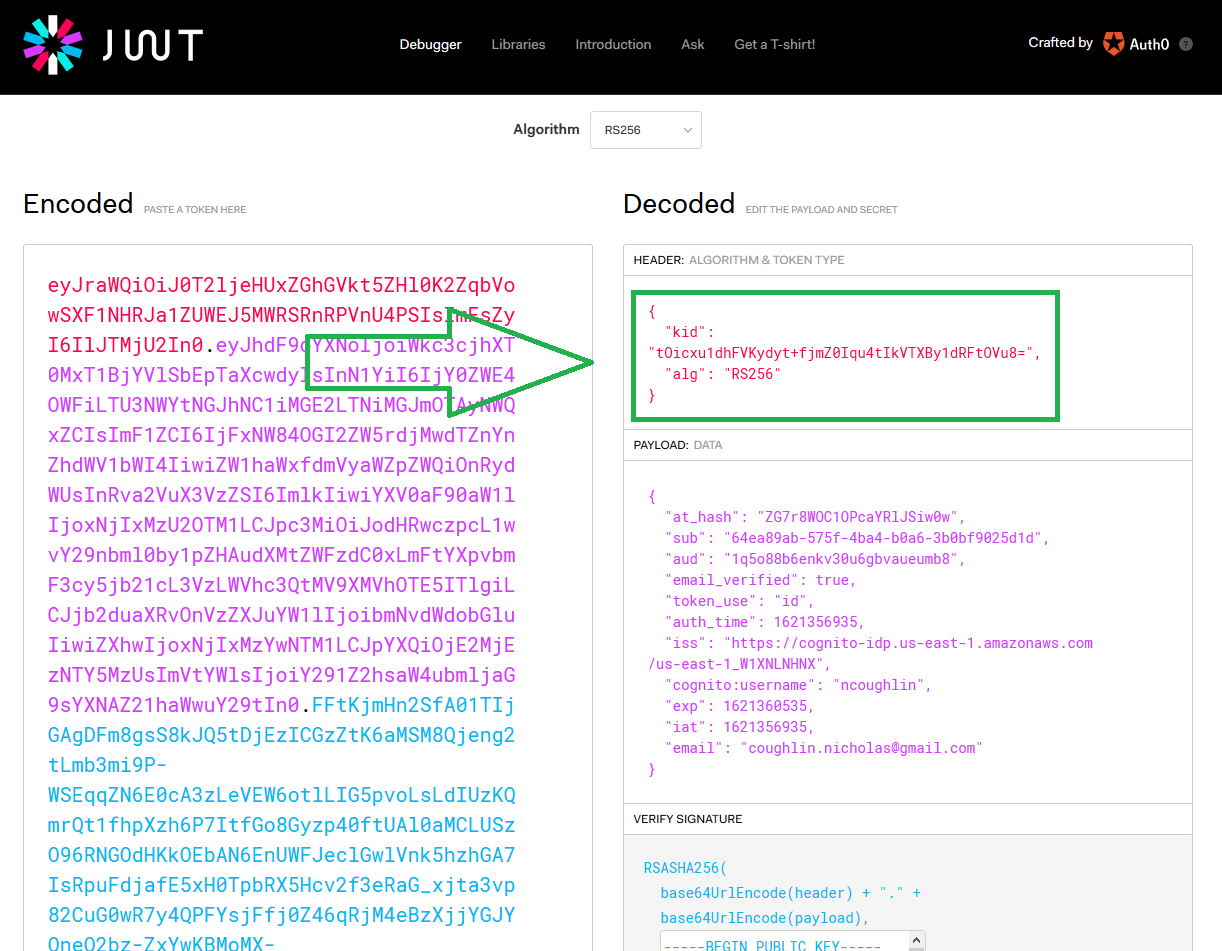
Verify And Decode Cognito Jwt Tokens Nicholas Coughlin You can securely validate jwt tokens issued by aws cognito using the jwx library. this ensures the token’s signature and claims are valid before granting access to your protected resources. When a user signs into your app, amazon cognito verifies the login information. if the login is successful, amazon cognito creates a session and returns an id token, an access token, and a refresh token for the authenticated user.
Comments are closed.