Jeb3 Demo Native Code Auto Signing
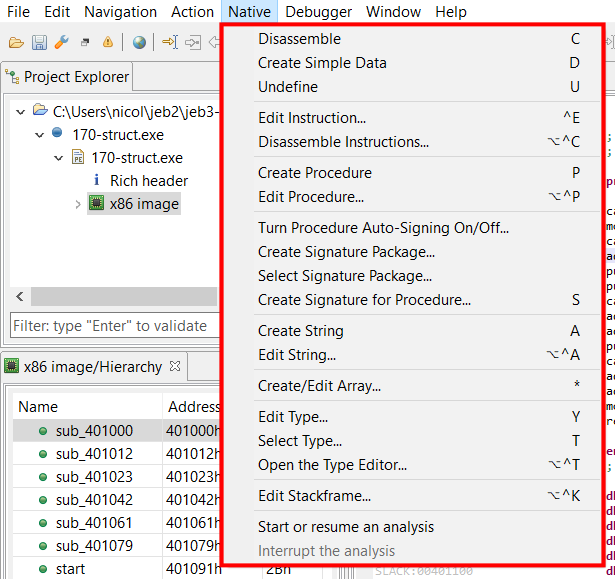
Native Code Analysis Jeb Decompiler Jeb 3.0 now allows users to create signatures on native code and features an "auto signing mode" for easy reuse of work between analysis! more. In this video we introduce a novel jeb 3.0 feature: auto signing mode for native code. in a nutshell, when this mode is activated all modifications made by users to native code in jeb (renaming a routine, adding a comment, etc) are “signed”.

Debugging Jeb Pro Is Not Showing Xrefs For Native Code Arm In this video we introduce a novel jeb 3.0 feature: auto signing mode for native code. in a nutshell, when this mode is activated all modifications made by users to native code in jeb (renaming a routine, adding a comment, etc) are “signed”. In this video we introduce a novel jeb 3.0 feature: auto signing mode for native code. in a nutshell, when this mode is activated all modifications made by users to native code in jeb (renaming a routine, adding a comment, etc) are “signed”. If you are a registered user, you can request to be put on the early adopters list and use jeb3 right now. you may also decide to wait and automatically receive your build when it becomes publicly available for all. the release date is scheduled for the early fall. Jeb 3.3 ships with our internal tool siglibgen to generate signatures for native routines. until now, users could sign individual routines only from jeb user interface (menu native> create signature for procedure), or with the auto signing mode.
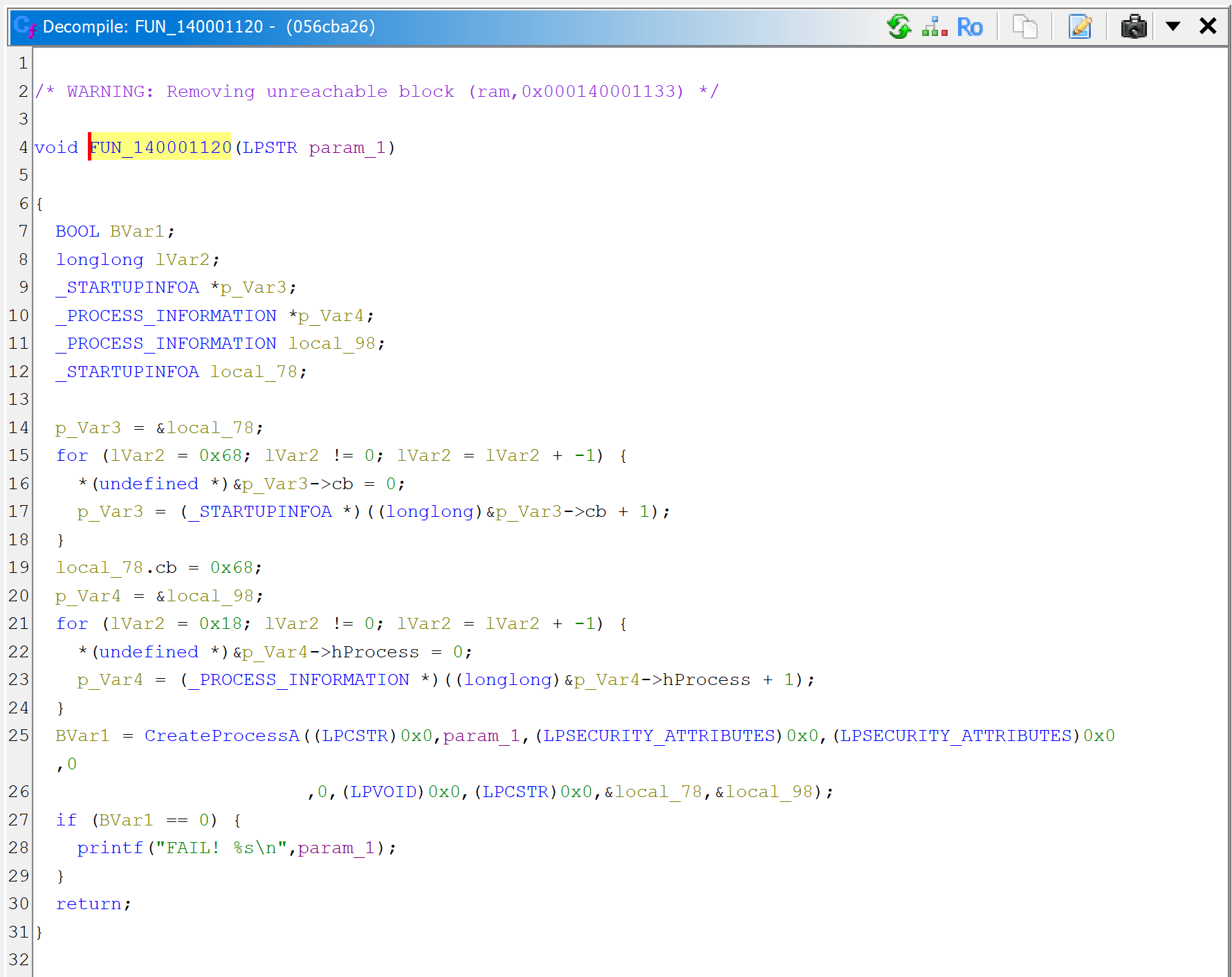
How To Use Jeb Auto Decrypt Strings In Protected Binary Code Jeb In If you are a registered user, you can request to be put on the early adopters list and use jeb3 right now. you may also decide to wait and automatically receive your build when it becomes publicly available for all. the release date is scheduled for the early fall. Jeb 3.3 ships with our internal tool siglibgen to generate signatures for native routines. until now, users could sign individual routines only from jeb user interface (menu native> create signature for procedure), or with the auto signing mode. 本课时我们就来介绍一下逆向相关的操作,通过逆向操作获得 apk 反编译后的代码,然后追踪这个 token 的生成逻辑是怎样的,最后我们再用代码把这个逻辑实现出来。 app 逆向其实多数情况下就是反编译得到 app 的源码,然后从源码里面找寻特定的逻辑,本课时就来演示一下 app 的反编译和入口点查找操作。 在这里我们使用的逆向工具叫作 jeb。 jeb 是一款专业的安卓应用程序的反编译工具,适用于逆向和审计工程,功能非常强大,可以帮助逆向人员节省很多逆向分析时间。 利用这个工具我们能方便地获取到 apk 的源码信息,逆向一个 apk 不在话下。. Jeb3 demo (include mips && arm64 && elf && pe && wasm decompiler) without limit jeb3 readme.md at master · chensem jeb3. 静态分析技术是指破解者利用反汇编工具将二进制的可执行文件翻译成汇编代码,通过对代码的分析来破解软件;而动态调试则是指破解者利用调试器跟踪软件的运行,寻求破解的途径。 动态调试有两种方法:jeb调试和androidstudio smalidea插件动态调试。 jeb是一款功能强大的为安全专业人士设计的android、应用程序反编译工具。 用于逆向工程或审计apk文件,可以提高效率减少许多工程师的分析时间。 首先下载jeb工具,下载完成后解压安装包, 解压后运行安装目录下的jeb wincon.bat文件。 本节课以“zhuceji.apk”文件作为案例,再下载“zhuceji.apk”文件,打开雷电模拟器安装该apk,点击运行。. Continue with google continue with github continue with apple continue with saml sso.
Comments are closed.