Java Top 10 Security Vulnerabilities Guardrails

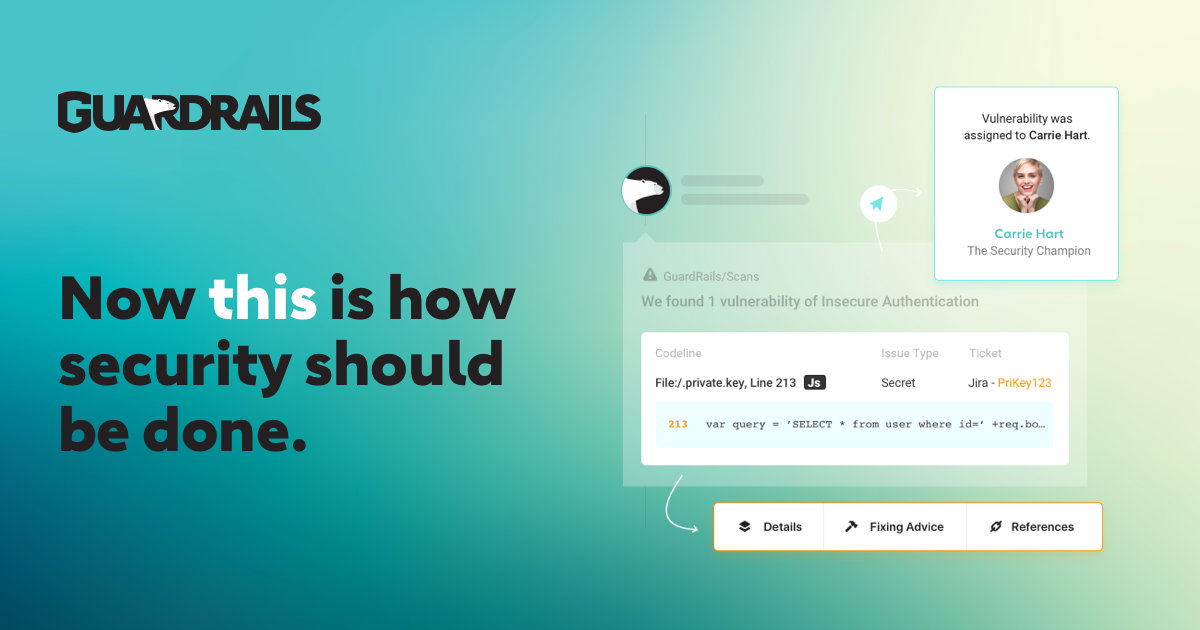
Java Top 10 Security Vulnerabilities Guardrails While java is considered relatively safe because it is a server side language, there are still multiple ways to attack and access secure code you’d like to remain private. here are the top ten java security vulnerabilities to keep in mind as you code away. Guardrails' sast solution offers a comprehensive approach by scanning your code for security vulnerabilities, ensuring quality assurance, and helping you maintain a secure and compliant.

Java Top 10 Security Vulnerabilities Guardrails Get to know the most commonly searched high risk java cves in our vulnerability database. Owasp top 10: the foundation of secure development owasp (open web application security project) provides a list of the most critical web app vulnerabilities. every java developer should be familiar with this list. Improve the security of your java code with our easy to use security platform and find and fix vulnerabilities in seconds. This category covers the following vulnerabilities: 📄️ insecure use of cryptography fixing insecure hashes 📄️ insecure use of dangerous function this vulnerability category covers the following issues: 📄️ insecure use of regular expressions fixing regular expression denial of service (redos) 📄️ insecure use of sql queries.

Java Top 10 Security Vulnerabilities Guardrails Improve the security of your java code with our easy to use security platform and find and fix vulnerabilities in seconds. This category covers the following vulnerabilities: 📄️ insecure use of cryptography fixing insecure hashes 📄️ insecure use of dangerous function this vulnerability category covers the following issues: 📄️ insecure use of regular expressions fixing regular expression denial of service (redos) 📄️ insecure use of sql queries. Let’s explore 11 common security vulnerabilities in java applications, highlighting how they arise, their potential impact, and, most importantly, how they can be mitigated. Learn about the top 10 java security vulnerabilities, how they work, and how finite state's software composition analysis can protect your application. Learn how to fix critical vulnerabilities in these 10 commonly used java related tools and technologies. Identifying and tackling the risks of gen ai systems and applications owasp genai security project a global community driven and expert led initiative to create freely available open source guidance and resources for understanding and mitigating security and safety concerns for generative ai applications and adoption. members k countries ai cybersecurity publications what’s new […].
Java Top 10 Security Vulnerabilities Guardrails Let’s explore 11 common security vulnerabilities in java applications, highlighting how they arise, their potential impact, and, most importantly, how they can be mitigated. Learn about the top 10 java security vulnerabilities, how they work, and how finite state's software composition analysis can protect your application. Learn how to fix critical vulnerabilities in these 10 commonly used java related tools and technologies. Identifying and tackling the risks of gen ai systems and applications owasp genai security project a global community driven and expert led initiative to create freely available open source guidance and resources for understanding and mitigating security and safety concerns for generative ai applications and adoption. members k countries ai cybersecurity publications what’s new […].
Java Top 10 Security Vulnerabilities Guardrails Learn how to fix critical vulnerabilities in these 10 commonly used java related tools and technologies. Identifying and tackling the risks of gen ai systems and applications owasp genai security project a global community driven and expert led initiative to create freely available open source guidance and resources for understanding and mitigating security and safety concerns for generative ai applications and adoption. members k countries ai cybersecurity publications what’s new […].
Comments are closed.