Java Deserialization Exploit Src Main Java Ysoserial Payloads
Java Deserialization Exploitation With Customized Ysoserial Payloads Ysoserial is a collection of utilities and property oriented programming "gadget chains" discovered in common java libraries that can, under the right conditions, exploit java applications performing unsafe deserialization of objects. This page provides practical examples of how to use ysoserial for generating java deserialization payloads in different exploitation scenarios. it covers the three main types of payloads: direct command execution, memory shell injection, and custom class loading.
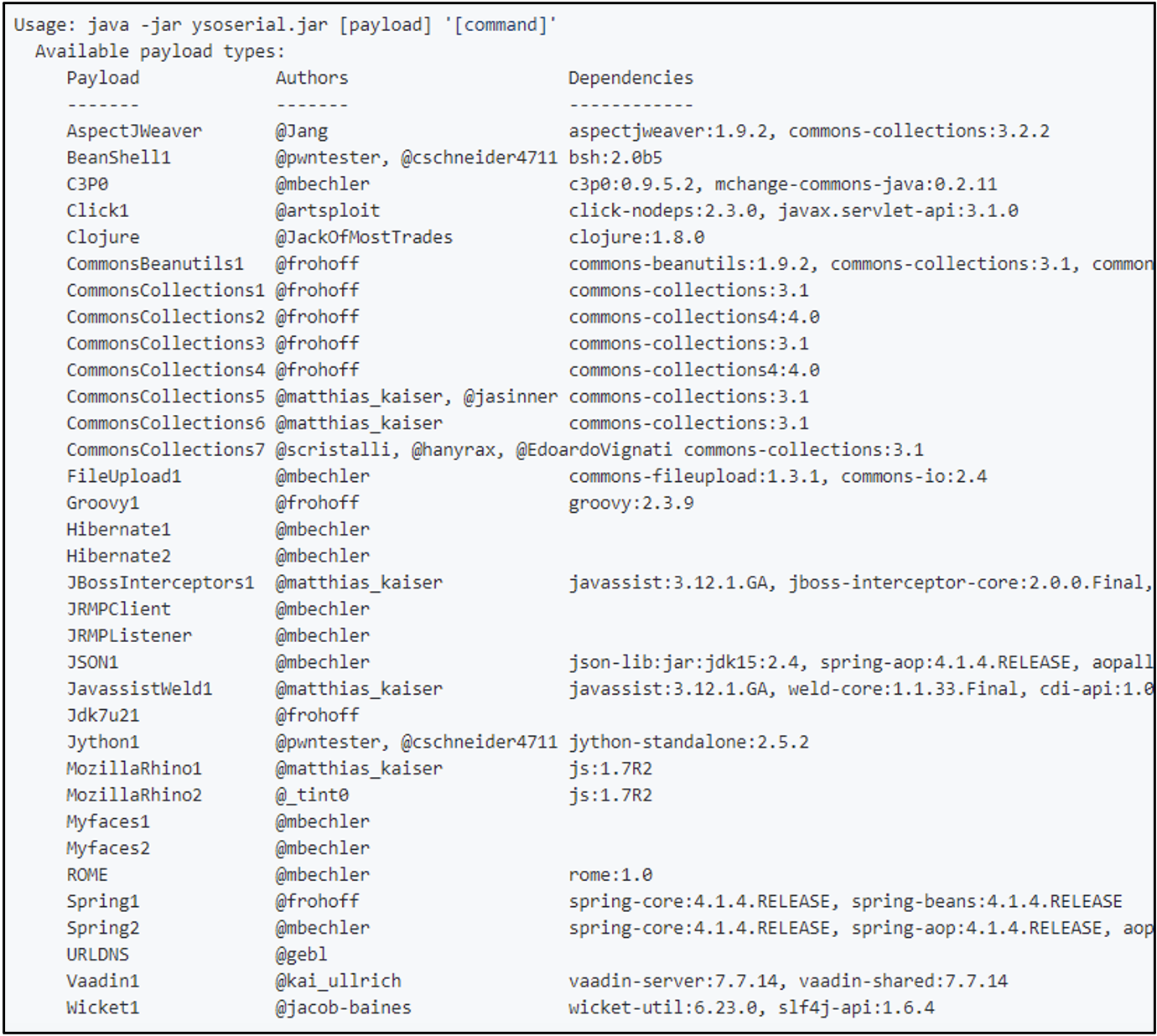
Now You Serial Now You Don T Systematically Hunting For Like any other java deserialization vulnerability, meaningful exploitation requires a gadget chain based on classes loaded on the server. the documentation for our customized fork of ysoserial includes a way to quickly generate payloads for all of its general purpose command execution gadget chains. Since 2015 when java deserialization was a major threat, lots of patches and improvements has been introduced. how to approach testing for java serialization to achieve best results?. A proof of concept tool for generating payloads that exploit unsafe java object deserialization. We analyze known deserialization exploits targeting applications developed in the java programming language. as previous research implies, fully comprehending this type of vulnerability is no easy task due to the complexity of exploitation, mostly relying on so called gadget chains.
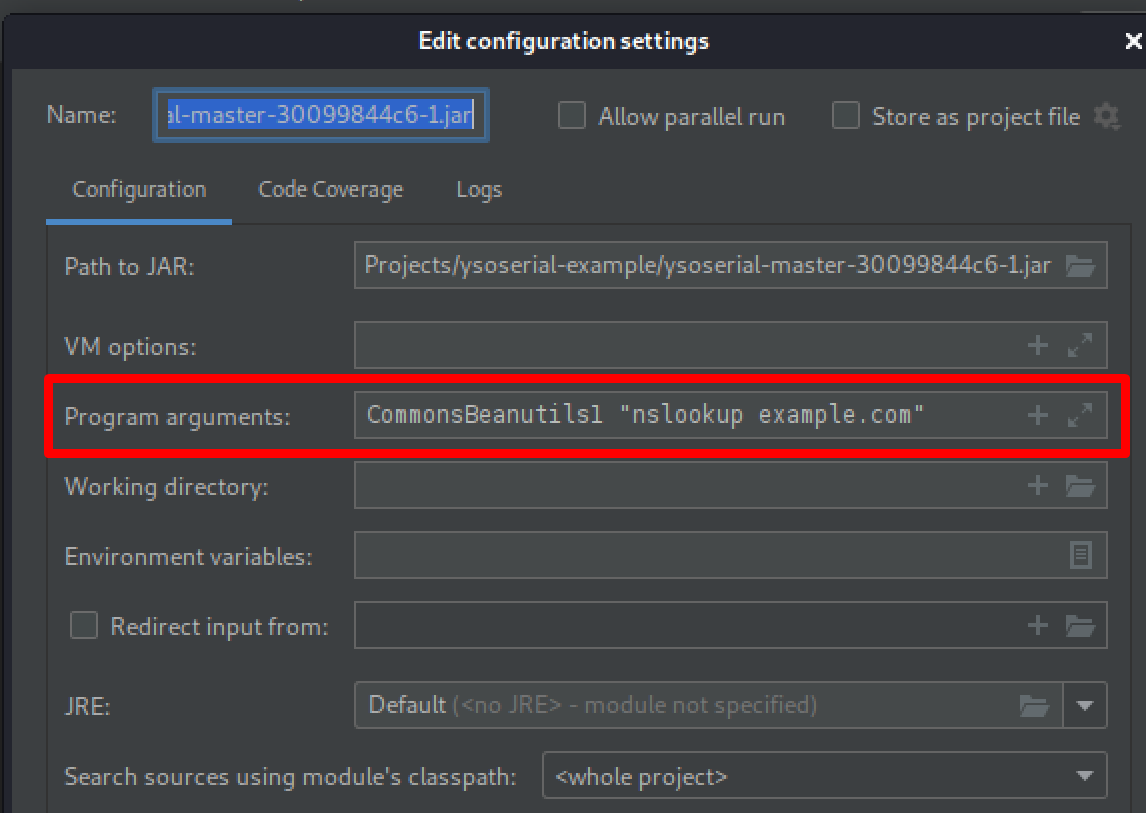
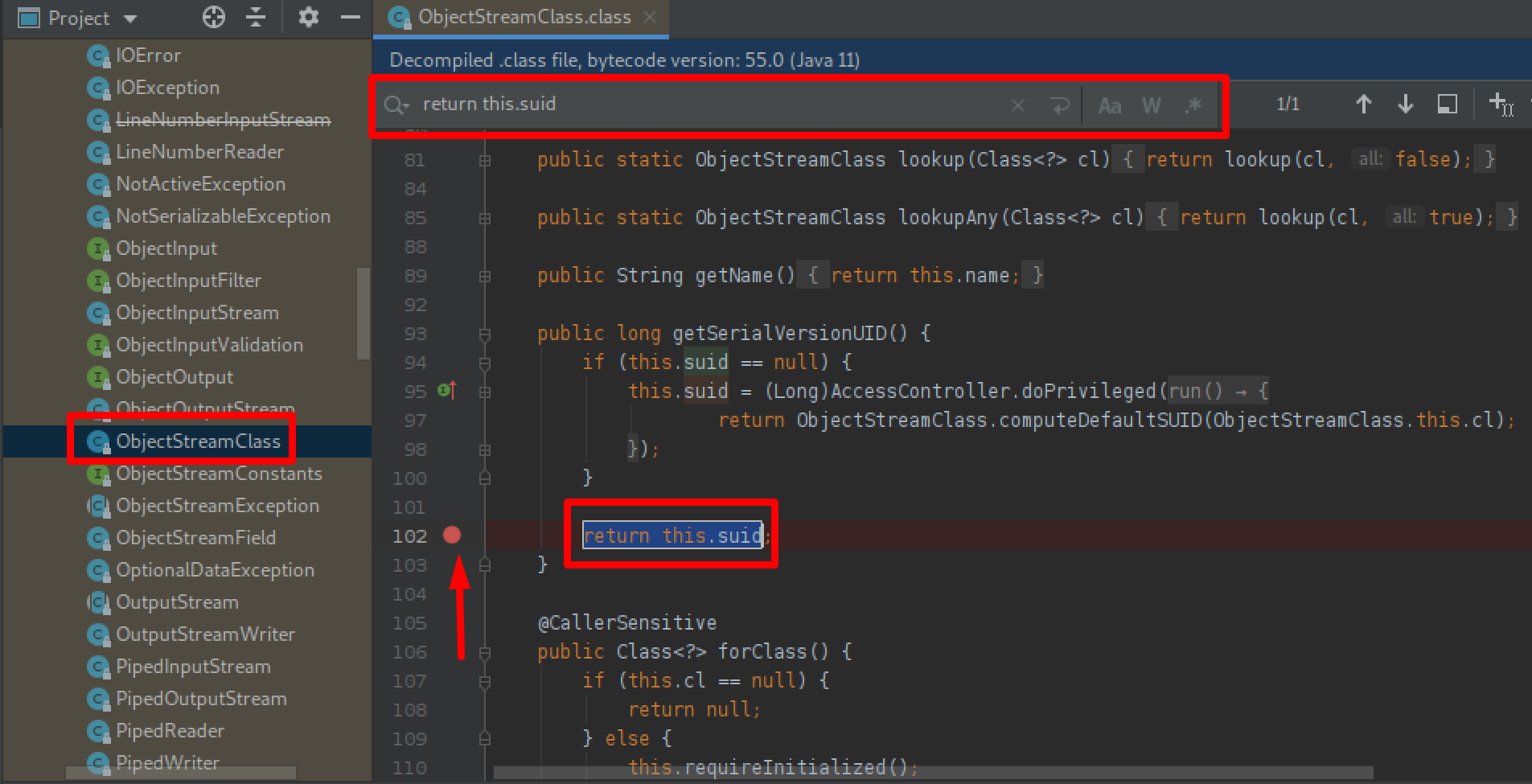
Java Deserialization Exploitation With Customized Ysoserial Payloads A proof of concept tool for generating payloads that exploit unsafe java object deserialization. We analyze known deserialization exploits targeting applications developed in the java programming language. as previous research implies, fully comprehending this type of vulnerability is no easy task due to the complexity of exploitation, mostly relying on so called gadget chains. Last year we encountered the so called java object deserialization vulnerability (not a java's problem as it looks), which is deserializing an object which might lead to remote code execution (rce) or denial of service (dos) attacks. In this blog post we will walk through the process, tools, and techniques of modifying ysoserial to customize payloads and fix errors which might be encountered during exploitation. Java serialization is the process of converting a java object’s state into a byte stream, which can be stored or transmitted and later reconstructed (deserialized) back into the original object. To exploit a deserialization vulnerability, you identify readobject methods from classes in the application class path that are exploitable. classes in the path include all classes defined in.
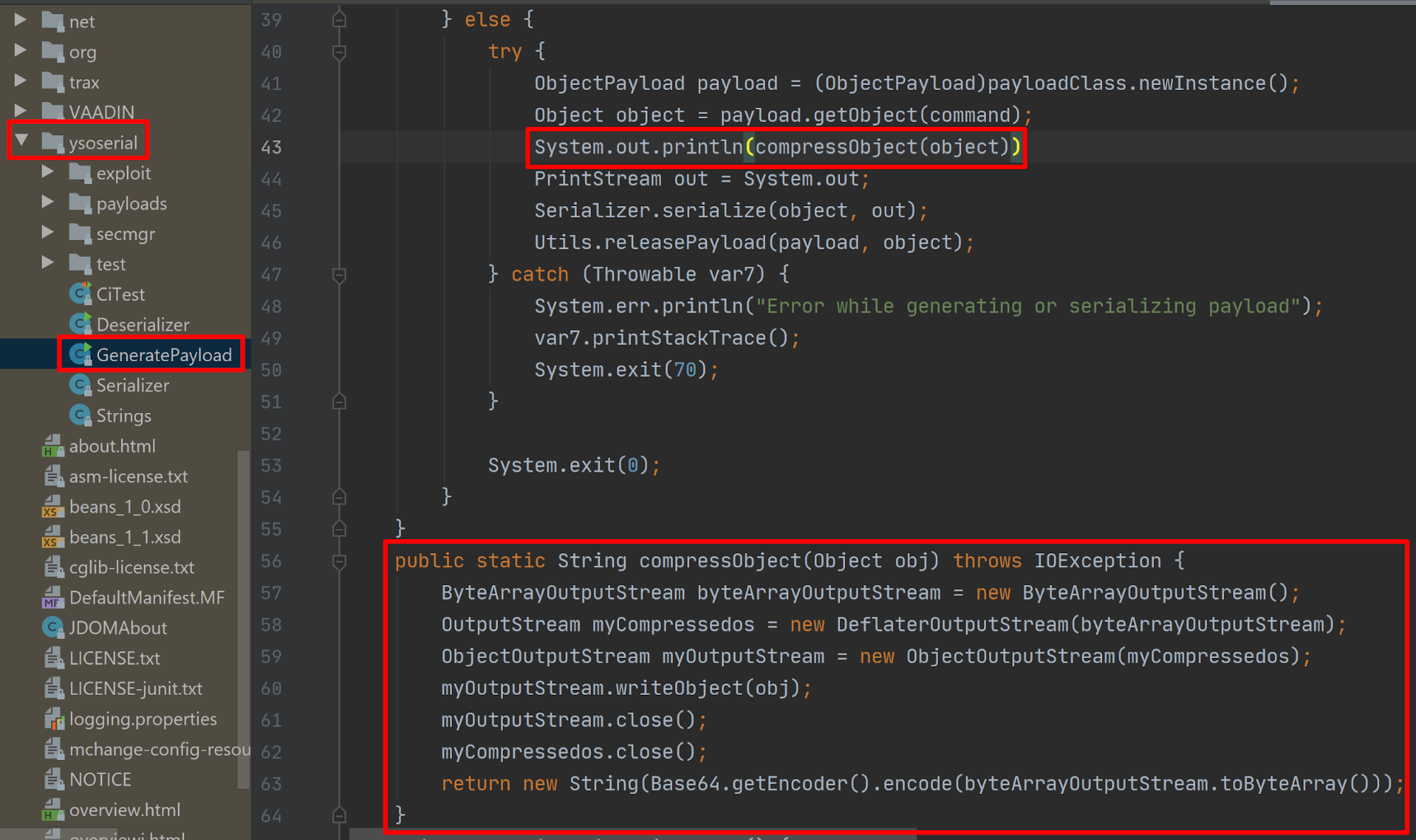
Java Deserialization Exploitation With Customized Ysoserial Payloads Last year we encountered the so called java object deserialization vulnerability (not a java's problem as it looks), which is deserializing an object which might lead to remote code execution (rce) or denial of service (dos) attacks. In this blog post we will walk through the process, tools, and techniques of modifying ysoserial to customize payloads and fix errors which might be encountered during exploitation. Java serialization is the process of converting a java object’s state into a byte stream, which can be stored or transmitted and later reconstructed (deserialized) back into the original object. To exploit a deserialization vulnerability, you identify readobject methods from classes in the application class path that are exploitable. classes in the path include all classes defined in.
Comments are closed.