Java Blowfish Encryption And Decryption Example
3 Blowfish Encryption And Decryption Algorithm Download Scientific Blowfish is an encryption technique designed by bruce schneier in 1993 as an alternative to the des encryption technique. it is significantly faster than des and provides a good encryption rate with no effective cryptanalysis technique found to date. Learn how to implement encryption and decryption using blowfish ciphers with the java cryptography architecture (jca).

3 Blowfish Encryption And Decryption Algorithm Download Scientific In this article, we explored the implementation of the blowfish encryption algorithm in java, utilizing the java cryptography architecture (jca). a code snippet is provided that demonstrates how to encrypt and decrypt data using the blowfish algorithm. The code demonstrates how to use the java cryptography architecture to implement the blowfish algorithm for encryption and decryption. this example showcases the actual process described above in a concise and practical manner. Securing sensitive data in java applications often requires robust encryption. this guide demonstrates how to implement blowfish encryption and decryption using java, covering key lengths from 32 to 448 bits. This project demonstrates how to perform symmetric encryption and decryption using the blowfish algorithm in java. the implementation includes separate files for encryption and decryption, showcasing how to securely handle plaintext data using blowfish with a custom key.
Java Encryption And Decryption Of An Image Using Blowfish Algorithm Securing sensitive data in java applications often requires robust encryption. this guide demonstrates how to implement blowfish encryption and decryption using java, covering key lengths from 32 to 448 bits. This project demonstrates how to perform symmetric encryption and decryption using the blowfish algorithm in java. the implementation includes separate files for encryption and decryption, showcasing how to securely handle plaintext data using blowfish with a custom key. The document outlines a java program that encrypts the text 'hello world' using the blowfish algorithm. it details the steps for generating a secret key, initializing a cipher, and displaying the encrypted and decrypted messages. Learn about blowfish encryption (32 448 bits) in java. discover its features, implementation, and security benefits for robust data protection. If you need to work with blowfish today, you’re usually doing one of three things: (1) decrypting historical data, (2) maintaining cross language interoperability with an older system, or (3) dealing with password hashing ecosystems that were influenced by blowfish’s key schedule (notably bcrypt). The blowfish algorithm allows bigger keys, but they fail in java because of the usa export restriction in the jre — the usa allow encryption but not stronger than what the nsa can break.
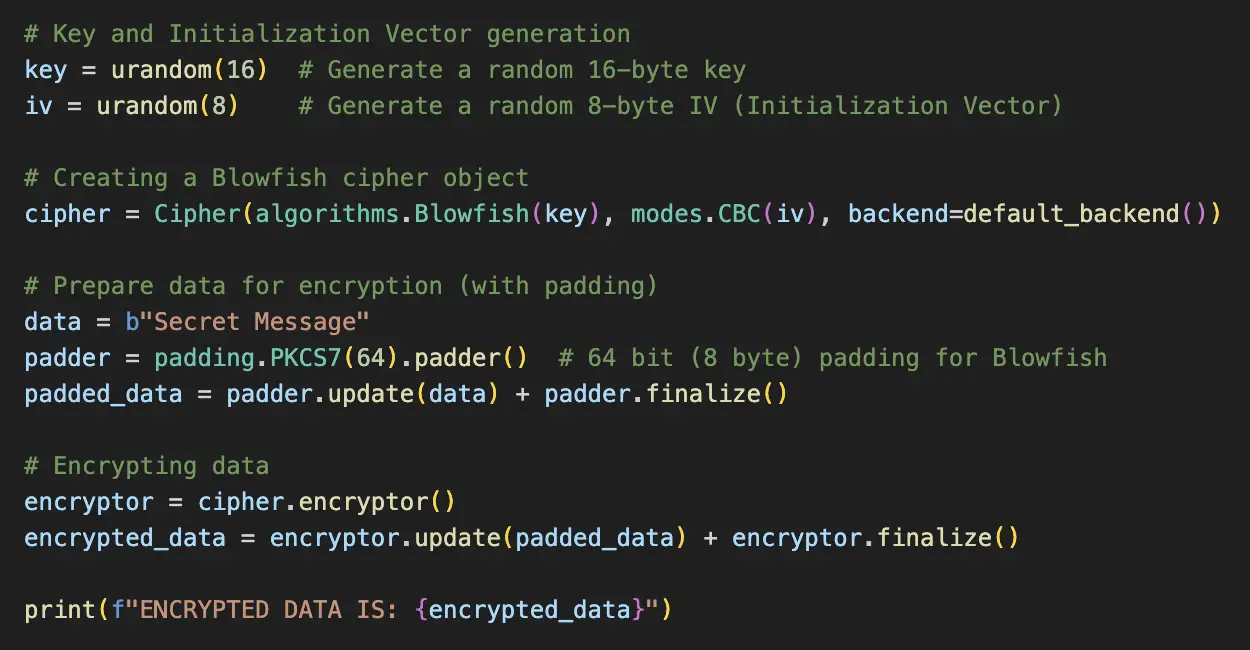
Python Blowfish Encryption Example Devrescue The document outlines a java program that encrypts the text 'hello world' using the blowfish algorithm. it details the steps for generating a secret key, initializing a cipher, and displaying the encrypted and decrypted messages. Learn about blowfish encryption (32 448 bits) in java. discover its features, implementation, and security benefits for robust data protection. If you need to work with blowfish today, you’re usually doing one of three things: (1) decrypting historical data, (2) maintaining cross language interoperability with an older system, or (3) dealing with password hashing ecosystems that were influenced by blowfish’s key schedule (notably bcrypt). The blowfish algorithm allows bigger keys, but they fail in java because of the usa export restriction in the jre — the usa allow encryption but not stronger than what the nsa can break.

Blowfish Encryption Algorithm Java Code Geeks If you need to work with blowfish today, you’re usually doing one of three things: (1) decrypting historical data, (2) maintaining cross language interoperability with an older system, or (3) dealing with password hashing ecosystems that were influenced by blowfish’s key schedule (notably bcrypt). The blowfish algorithm allows bigger keys, but they fail in java because of the usa export restriction in the jre — the usa allow encryption but not stronger than what the nsa can break.
Github Jdvor Encryption Blowfish Blowfish Symmetric Encryption With
Comments are closed.