It Manager S Guide How To Implement Zero Trust Security

Mastering A Zero Trust Security Strategy Pdf Security Computer Zero trust is easy to understand, but hard to implement, as it requires architectural changes, not just technical controls. let’s understand step by how to implement zero trust in practice. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments.

How To Implement A Zero Trust Security Model Our guide on how to implement zero trust security breaks down core principles, key components, and best practices for building a modern security framework. As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure. Secure your network with a step by step guide to zero trust implementation. learn the key principles and practical steps to achieve a zero trust security model. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users.

How To Implement Zero Trust Security Learn 7 Key Strategies Secure your network with a step by step guide to zero trust implementation. learn the key principles and practical steps to achieve a zero trust security model. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Seven practical steps to implement zero trust network security in your small business powered by the original gartner report. hands on tips to adopt and win the zero trust culture. This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture.
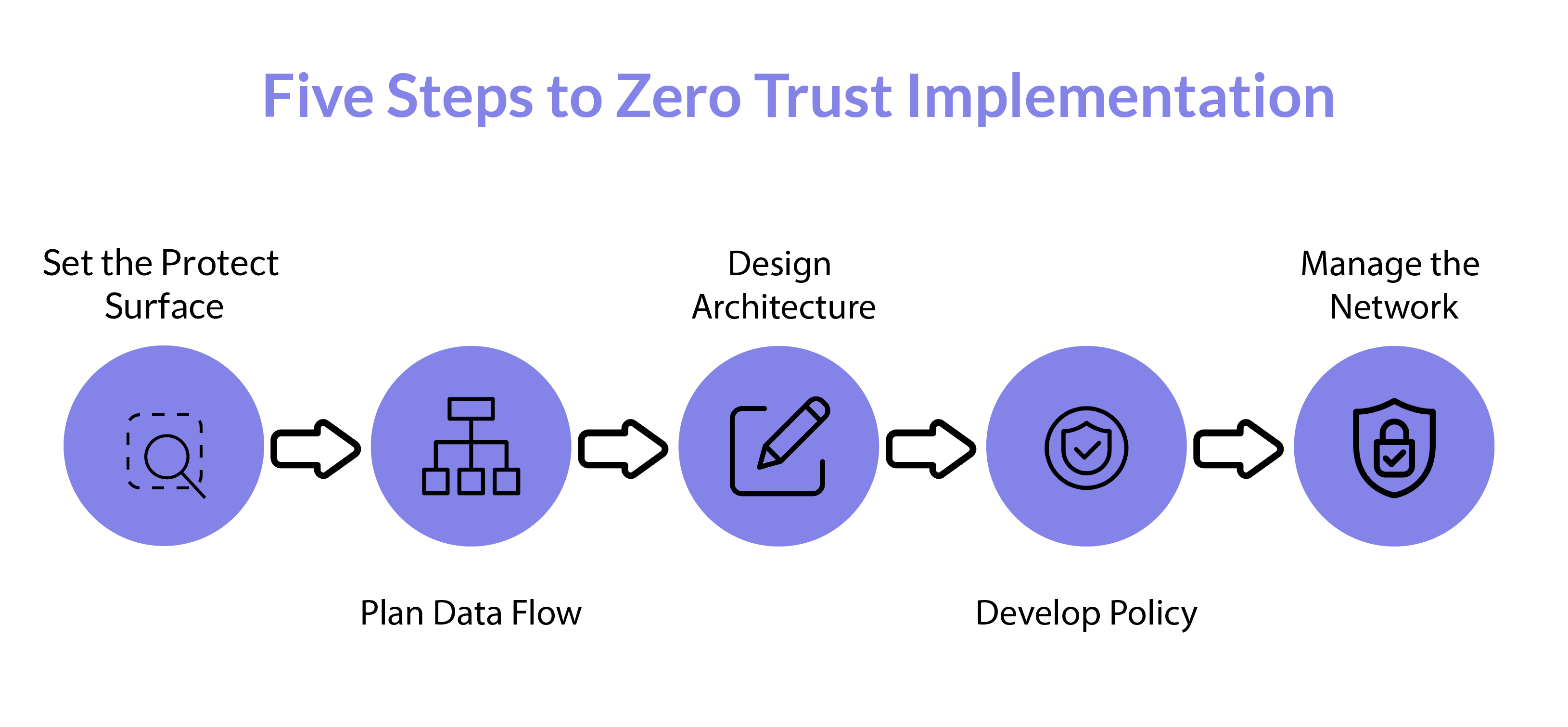
How To Implement Zero Trust Security Geniusee Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Seven practical steps to implement zero trust network security in your small business powered by the original gartner report. hands on tips to adopt and win the zero trust culture. This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture.

A Comprehensive Guide To Implementing Zero Trust Security I T In Vt This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. With a clear understanding of the five pillars of zero trust and your organizational security goals in mind, you can start acting on your zero trust implementation plan. these 10 steps offer a roadmap for using zero trust principles effectively as the basis for your organization’s security posture.

Steps To Implement Zero Trust Security Guarding Network Threats
Comments are closed.