It Information Security Syllabus Pdf Encryption Cryptography

Information Security And Cryptography Updated Syllabus Pdf The document outlines the syllabus for an information security course, including topics like cryptography, network security, security protocols, and authentication techniques. In this course students will learn as aspects of network security and cryptography.

Module 04 Cryptography And Encryption Pdf Cryptography Public Key Cyber security fundamentals: network and security concepts information assurance fundamentals, basic cryptography, symmetric and asymmetric encryption, public key encryption, the domain name system (dns), firewalls, virtualization, radio frequency identification. Cryptography concepts and techniques: introduction, plain text and cipher text, substitution techniques, transposition techniques, encryption and decryption, symmetric and asymmetric key cryptography, stenography, key range and key size, possible types of attacks. To explore the working principles and utilities of various cryptographic algorithms including secret key cryptography, hashes and message digests, and public key algorithms. Working principles and utilities of various cryptographic algorithms including secret key cryptography, hashes and message digests, and public key algorithms.
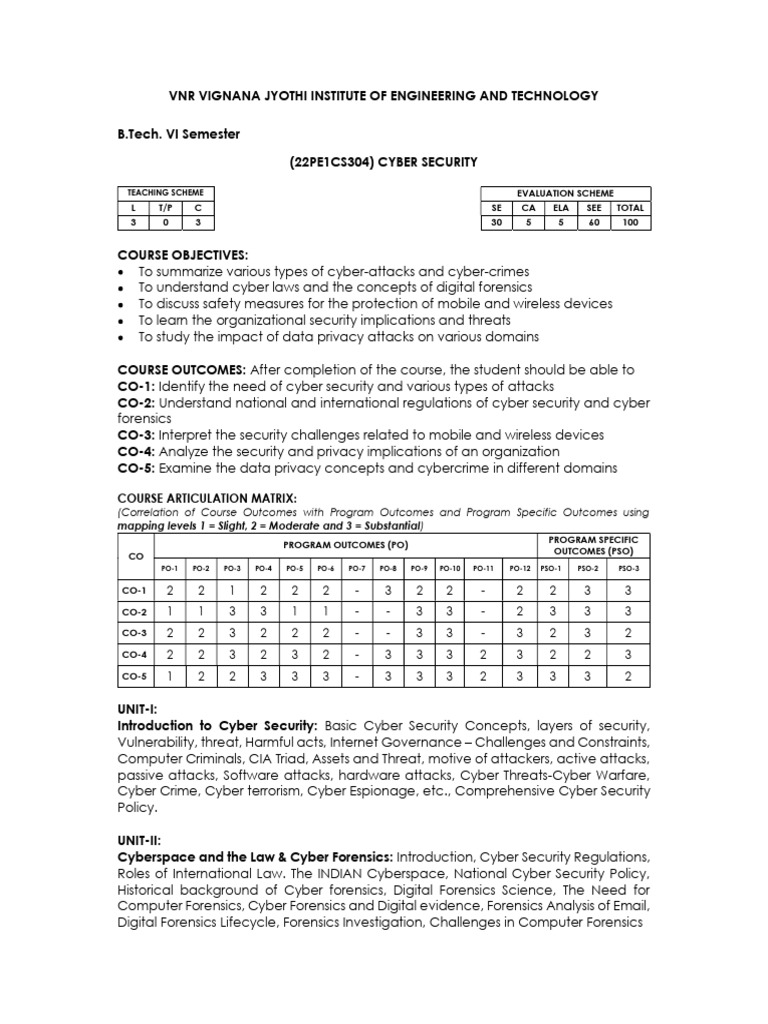
Cyber Security Syllabus Pdf Security Computer Security To explore the working principles and utilities of various cryptographic algorithms including secret key cryptography, hashes and message digests, and public key algorithms. Working principles and utilities of various cryptographic algorithms including secret key cryptography, hashes and message digests, and public key algorithms. Behrouz a. forouzan, “cryptography and network security”, tata mcgraw hill edition. Overview: internet security protocols are designed to protect data transmitted over the internet by providing various levels of security, including confidentiality, integrity, authentication, and non repudiation. After completing this course, the student will be able to: c413.1: understand various attacks on the network and understanding the need for security [analysis] c413.2: apply various classical encryption techniques on messages and analyze various security services and mechanisms. Cryptography: concepts and techniques: introduction, plain text and cipher text, substitution techniques, transposition techniques, encryption and decryption, symmetric and asymmetric cryptography, steganography, key range and key size, possible types of attacks.

Syllabus Pdf Information Security Security Behrouz a. forouzan, “cryptography and network security”, tata mcgraw hill edition. Overview: internet security protocols are designed to protect data transmitted over the internet by providing various levels of security, including confidentiality, integrity, authentication, and non repudiation. After completing this course, the student will be able to: c413.1: understand various attacks on the network and understanding the need for security [analysis] c413.2: apply various classical encryption techniques on messages and analyze various security services and mechanisms. Cryptography: concepts and techniques: introduction, plain text and cipher text, substitution techniques, transposition techniques, encryption and decryption, symmetric and asymmetric cryptography, steganography, key range and key size, possible types of attacks.

Fall 2021 Syllabus Pdf Cryptography Information Security After completing this course, the student will be able to: c413.1: understand various attacks on the network and understanding the need for security [analysis] c413.2: apply various classical encryption techniques on messages and analyze various security services and mechanisms. Cryptography: concepts and techniques: introduction, plain text and cipher text, substitution techniques, transposition techniques, encryption and decryption, symmetric and asymmetric cryptography, steganography, key range and key size, possible types of attacks.
Comments are closed.