It Compliance Frameworks What Is The Nist Cybersecurity Framework How Does Soc 2 Map To It
Soc 2 Vs Nist How Do They Compare Compliancy Group A definitive guide to the soc 2 vs nist cybersecurity framework. learn the key differences in scope, controls, and audit strategy to achieve compliance. Here is expert guidance on how to use the nist csf to implement a cybersecurity framework that maps to the soc 2 criteria and supports your audit compliance.
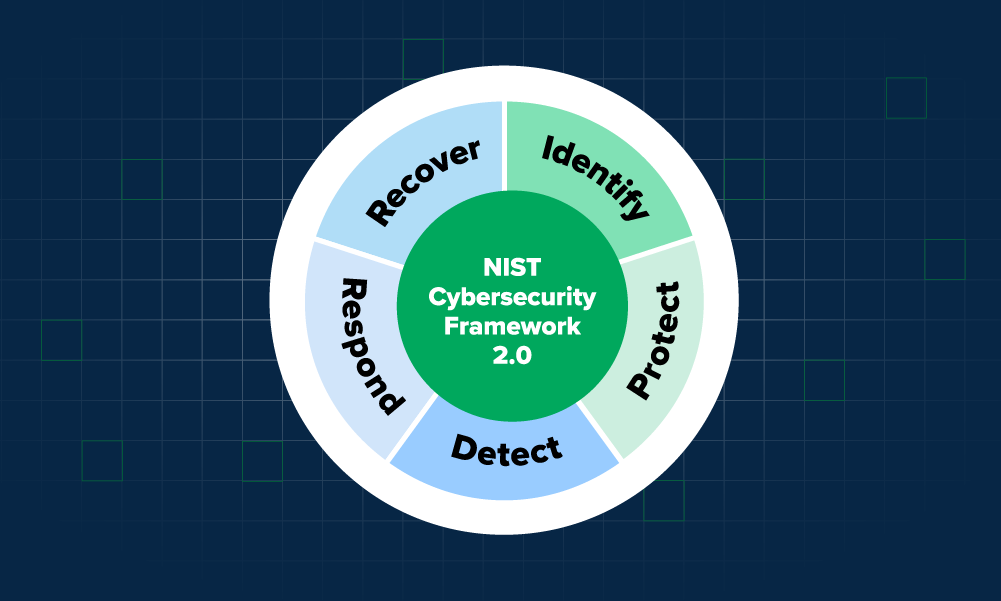
Navigating Nist Cybersecurity Frameworks Compliance Expel This draft explains how to find, filter, and apply informative references using nist tools. review and submit comments here. the final version of nist cybersecurity framework 2.0: cybersecurity, enterprise risk management, and workforce management quick start guide. Understand the roles of soc 2 and nist frameworks in helping organizations secure sensitive data and manage risk effectively. The nist cybersecurity framework (csf) and soc 2 are two popular frameworks used to assess the security and compliance of organizations. the csf is focused on risk management, while soc 2 is focused on trust and assurance. What is the nist cybersecurity framework the nist cybersecurity framework (csf) is a voluntary framework developed by the national institute of standards and technology that provides organizations with a structured approach to managing cybersecurity risk. originally published in 2014 and updated to csf 2.0 in 2024, the framework is used by organizations of all sizes across all industries.
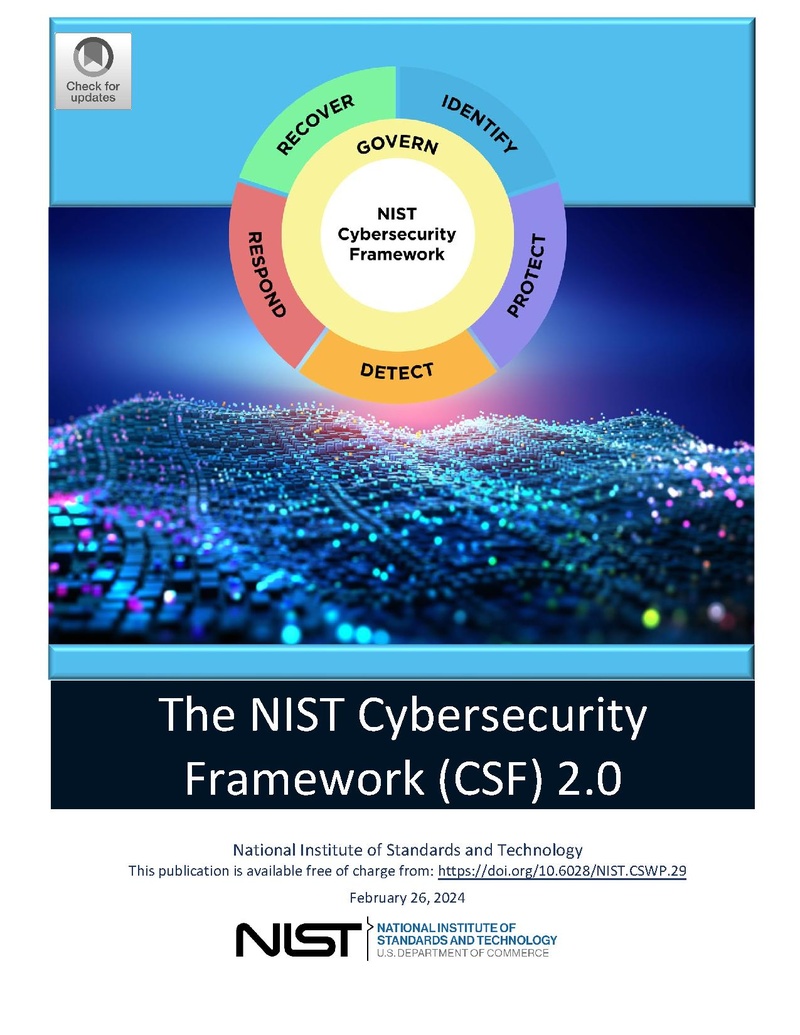
Nist Cybersecurity Framework 2 0 Opencommons The nist cybersecurity framework (csf) and soc 2 are two popular frameworks used to assess the security and compliance of organizations. the csf is focused on risk management, while soc 2 is focused on trust and assurance. What is the nist cybersecurity framework the nist cybersecurity framework (csf) is a voluntary framework developed by the national institute of standards and technology that provides organizations with a structured approach to managing cybersecurity risk. originally published in 2014 and updated to csf 2.0 in 2024, the framework is used by organizations of all sizes across all industries. Among the most prominent are soc 2, the nist cybersecurity framework (csf), iso 27001, and nist special publication 800 53 (sp 800 53). this article explores the differences between these frameworks to help you determine which might be most appropriate for your organization’s needs. Soc 2 can ensure that customer data is handled securely and meets compliance requirements, while nist’s guidelines can offer a broader framework for identifying and mitigating cybersecurity risks across the entire organization. Soc 2 mapping is the process of aligning the requirements and controls of the soc 2 framework with those of other relevant frameworks or security standards. this involves identifying commonalities and overlaps between soc 2 and other compliance standards such as iso 27001, gdpr, or nist. Discover how nist csf, iso 27001, and soc 2 differ in scope, structure, and application, and learn how to choose the right cybersecurity framework for your organization’s needs.
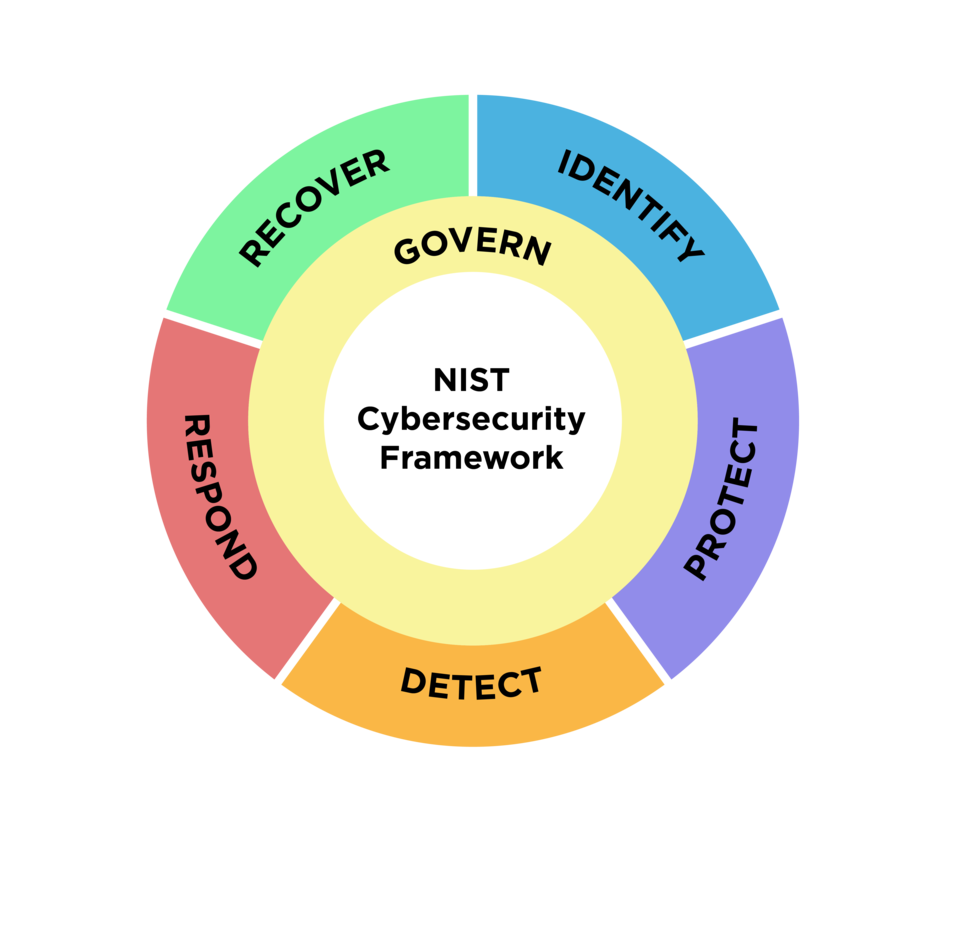
Nist Cybersecurity Framework 2 0 Among the most prominent are soc 2, the nist cybersecurity framework (csf), iso 27001, and nist special publication 800 53 (sp 800 53). this article explores the differences between these frameworks to help you determine which might be most appropriate for your organization’s needs. Soc 2 can ensure that customer data is handled securely and meets compliance requirements, while nist’s guidelines can offer a broader framework for identifying and mitigating cybersecurity risks across the entire organization. Soc 2 mapping is the process of aligning the requirements and controls of the soc 2 framework with those of other relevant frameworks or security standards. this involves identifying commonalities and overlaps between soc 2 and other compliance standards such as iso 27001, gdpr, or nist. Discover how nist csf, iso 27001, and soc 2 differ in scope, structure, and application, and learn how to choose the right cybersecurity framework for your organization’s needs.
Comments are closed.