Is Your Orm Vulnerable To Sql Injection
Fixing Sql Injection Orm Is Not Enough Snyk This article shows how sql injection vulnerabilities can still occur in apps using modern orm frameworks. learn how to spot insecure patterns and write safer code. It is possible, however, for a web application using orm generated objects to be vulnerable to sql injection attacks if methods can accept unsanitized input parameters. orm layers can be prone to vulnerabilities, as they extend the surface of attack.
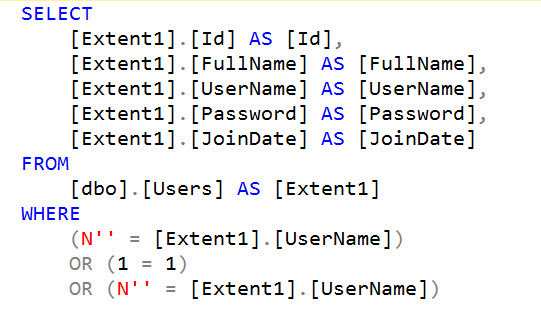
2 5 Ways Your Orm Is Vulnerable To Sql Injection Despite using orms like django, rails activerecord, and hibernate, sql injection remains a critical threat in 2025. analyze recent cves, real world breaches, and how to secure your orm usage. This article explores how prisma orm provides built in protection against sql injection and best practices for maintaining that security in alignment with owasp recommendations. A critical vulnerability has been identified in mikroorm, a widely used typescript object relational mapper (orm) for node.js. with over 2 million downloads every month, the impact of this flaw could be felt across a vast ecosystem of modern web applications. the vulnerability, tracked as cve 2026 34220, carries a cvssv4 score of 9.3, signaling an urgent need for developers to patch their. It is also possible for a web application using orm generated objects to be vulnerable to sql injection attacks or orm injections if methods can accept unsanitized input parameters.
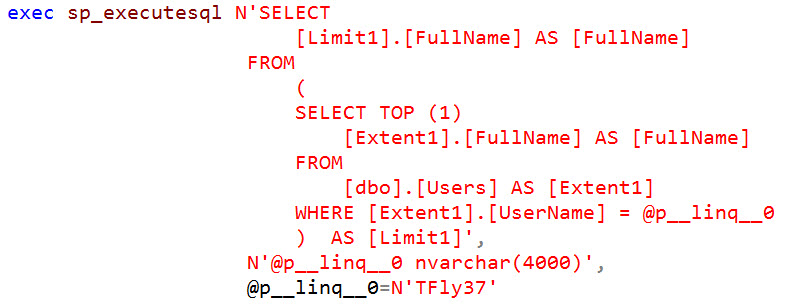
2 5 Ways Your Orm Is Vulnerable To Sql Injection A critical vulnerability has been identified in mikroorm, a widely used typescript object relational mapper (orm) for node.js. with over 2 million downloads every month, the impact of this flaw could be felt across a vast ecosystem of modern web applications. the vulnerability, tracked as cve 2026 34220, carries a cvssv4 score of 9.3, signaling an urgent need for developers to patch their. It is also possible for a web application using orm generated objects to be vulnerable to sql injection attacks or orm injections if methods can accept unsanitized input parameters. It is possible, however, for a web application using orm generated objects to be vulnerable to sql injection attacks if methods can accept unsanitized input parameters. orm layers can be prone to vulnerabilities, as they extend the surface of attack. With advancements in cyber security, many developers have adopted object relational mapping (orm) to mitigate sql injection attacks. while orm is intended to simplify database interactions and improve security, the threat of injection attacks is still not over. It is possible, however, for a web application using orm generated objects to be vulnerable to sql injection attacks if methods can accept unsanitized input parameters. orm layers can be prone to vulnerabilities, as they extend the surface of attack. One of the most dangerous and widespread vulnerability types is sql injection, which gives attackers access to your backend database. using prepared statements and object relational mapping (orm) is a good way to defend against sql injection, but it’s not enough.
Comments are closed.