Is Answer Key Pdf Public Key Cryptography Key Cryptography

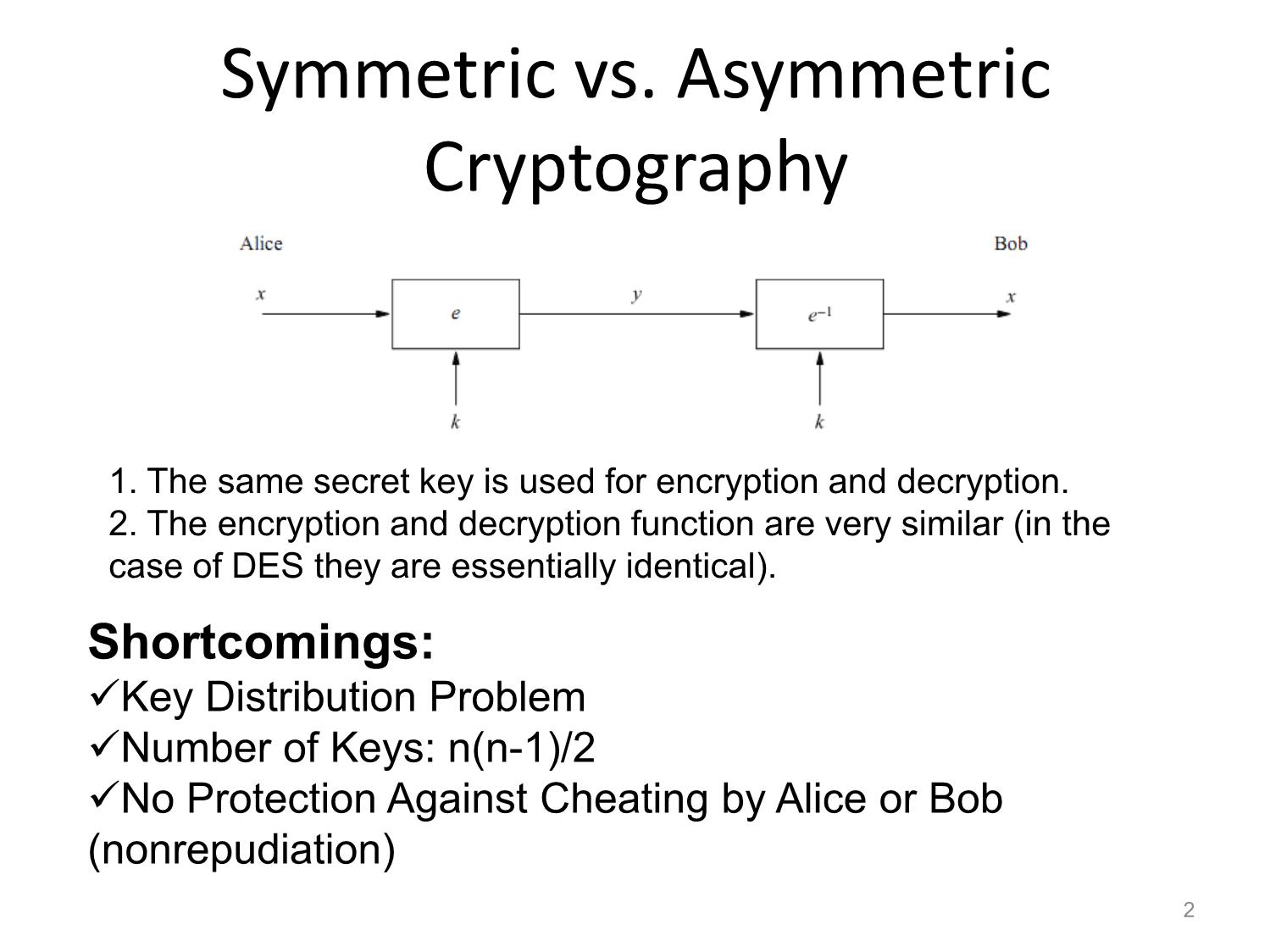
Public Key Cryptography Pdf Public Key Cryptography Encryption It includes short answer questions and practical problems, such as rsa encryption and hash functions, with detailed solutions provided. the exam assesses understanding of key concepts and practical applications in cryptography. Why public key cryptography? developed to address two key issues: key distribution– how to have secure communications in general without having to trust a kdc with your key digital signatures– how to verify a message comes intact from the claimed sender.

Lecture 2 Public Key Cryptography Pdf Cryptography Public Key Asymmetric cryptography refers to using both a public key and a private key. the public key is known to everyone and is used to encrypt messages and verify digital signatures. the private key is known only to the user and is used to decrypt the ciphertext or generate digital signatures. Public key algorithms rely on one key for encryption and a different but related key for decryption. these algorithms have the following important characteristics:. Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair. – introduction to public key cryptography october 6, 2024 these slides were originally prepared by timo kasper and christof paar. later, they were modified by tomas fabsic for purposes of teaching i zkry at fei stu.
Public Key Cryptography Elgamal encryption transforms diffie hellman key agreement into a public key encryption scheme by using the public secret information of the recipient as a long term key pair and the public secret information of the sender as a one time key pair. – introduction to public key cryptography october 6, 2024 these slides were originally prepared by timo kasper and christof paar. later, they were modified by tomas fabsic for purposes of teaching i zkry at fei stu. These extensions provide a method for integrating public key cryptography into the initial authentication exchange, by using asymmetric key signature and or encryption algorithms in pre authentication data fields. Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key. Anyone can encrypt a message using a recipient’s public key only the recipient can decrypt a message using their private key no shared secret! private key (secret) is stored only at one side. Public and private keys: this is a pair of keys that have been selected so that if one is used for encryption, the other is used for decryption. the exact transformations performed by the algorithm depend on the public or private key that is provided as input.
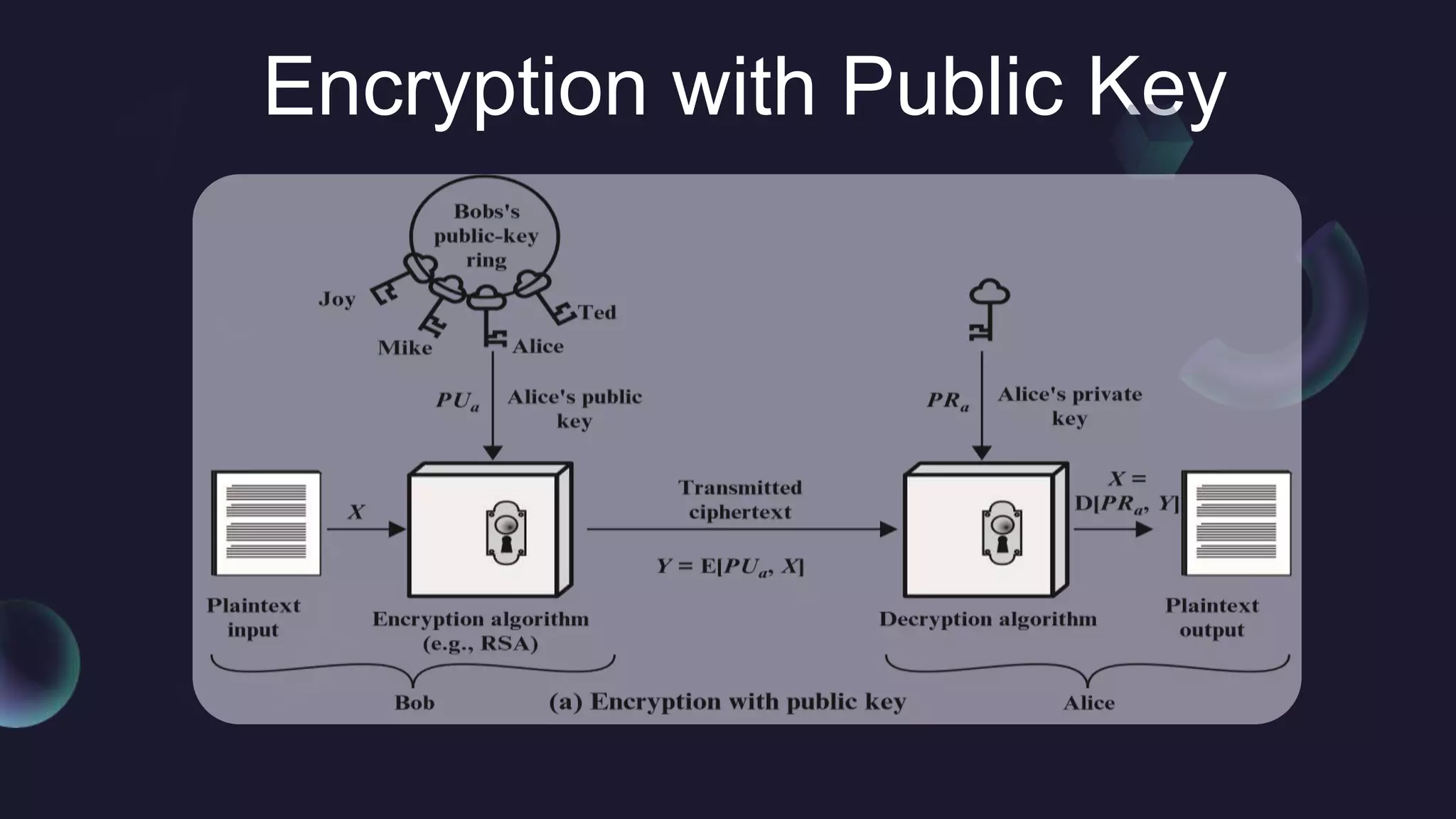
Public Key Cryptography Pptx These extensions provide a method for integrating public key cryptography into the initial authentication exchange, by using asymmetric key signature and or encryption algorithms in pre authentication data fields. Reduce protection of information to protection of authenticity of public keys • no need to keep public keys secret, but must be sure that alice’s public key is really her true public key. Anyone can encrypt a message using a recipient’s public key only the recipient can decrypt a message using their private key no shared secret! private key (secret) is stored only at one side. Public and private keys: this is a pair of keys that have been selected so that if one is used for encryption, the other is used for decryption. the exact transformations performed by the algorithm depend on the public or private key that is provided as input.

Pdf Public Key Cryptography Anyone can encrypt a message using a recipient’s public key only the recipient can decrypt a message using their private key no shared secret! private key (secret) is stored only at one side. Public and private keys: this is a pair of keys that have been selected so that if one is used for encryption, the other is used for decryption. the exact transformations performed by the algorithm depend on the public or private key that is provided as input.

Public Key Cryptography Pdf Public Key Cryptography Cryptography
Comments are closed.