Ip Spoofing Through Nmap
Ip Spoofing In this situation, use s with the ip address of the interface you wish to send packets through. another possible use of this flag is to spoof the scan to make the targets think that someone else is scanning them. Learn how to use the ` s` option with nmap to spoof the source address, a powerful tool for testing firewall rules and evading detection.
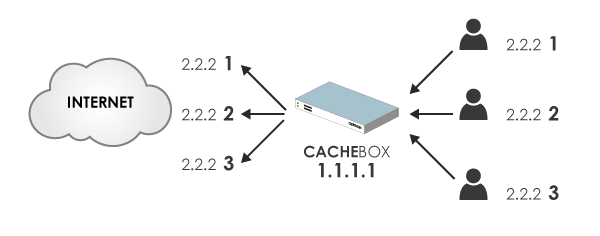
Ip And Mac Spoofing Techniques Using Nmap For Stealth Scanning Learn how to evade firewalls and ids with nmap! master nmap techniques like decoy scans, packet fragmentation, ip spoofing, and rate limiting for network security testing. improve your nmap skills today!. Offensive nmap guide for penetration testers and red teamers. includes practical examples, evasion techniques, and advanced usage for network reconnaissance and stealth scanning. This blog explores advanced, lesser known nmap capabilities that bypass firewalls, evade ids ips, and leave minimal forensic trace. it’s a tactical guide for professionals who need to map. In this nmap cheat sheet, you'll learn all the basics to advanced like basic scanning techniques, discovery options in nmap, firewall evasion techniques, version detection, output options, scripting engines and more.
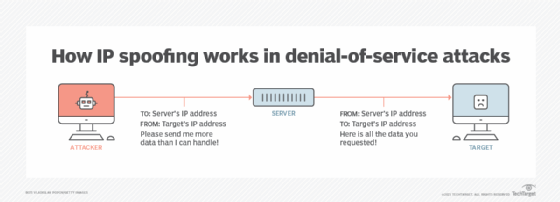
What Is Ip Spoofing How To Prevent It This blog explores advanced, lesser known nmap capabilities that bypass firewalls, evade ids ips, and leave minimal forensic trace. it’s a tactical guide for professionals who need to map. In this nmap cheat sheet, you'll learn all the basics to advanced like basic scanning techniques, discovery options in nmap, firewall evasion techniques, version detection, output options, scripting engines and more. Learn how to perform ip and mac spoofing with nmap to mask scan origins, evade detection, and understand ethical considerations in network scanning. Use this guide to quickly find the right commands for everything from basic discovery to advanced, low profile scanning. nmap is like a multi tool knife that can be used for a variety of situations you might find yourself in as an ethical hacker. In this blog i will be sharing the use of different switches which are used in nmap of bypassing firewall ids ips. with the use of this switches, data packets can be sent in the way that firewall ids ips does not detect the packet as different than normal packets. If you're actually trying to scan something, the only useful reason to use s is to set your source ip when nmap can't figure it out itself. alternatively, you can make it look like an nmap scan is coming from another system on the network, in order to confuse a defender and waste their time.
Ip Spoofing Pelo Nmap Security Master Learn how to perform ip and mac spoofing with nmap to mask scan origins, evade detection, and understand ethical considerations in network scanning. Use this guide to quickly find the right commands for everything from basic discovery to advanced, low profile scanning. nmap is like a multi tool knife that can be used for a variety of situations you might find yourself in as an ethical hacker. In this blog i will be sharing the use of different switches which are used in nmap of bypassing firewall ids ips. with the use of this switches, data packets can be sent in the way that firewall ids ips does not detect the packet as different than normal packets. If you're actually trying to scan something, the only useful reason to use s is to set your source ip when nmap can't figure it out itself. alternatively, you can make it look like an nmap scan is coming from another system on the network, in order to confuse a defender and waste their time.
Comments are closed.