Iot Secure Development Guide Pen Test Partners
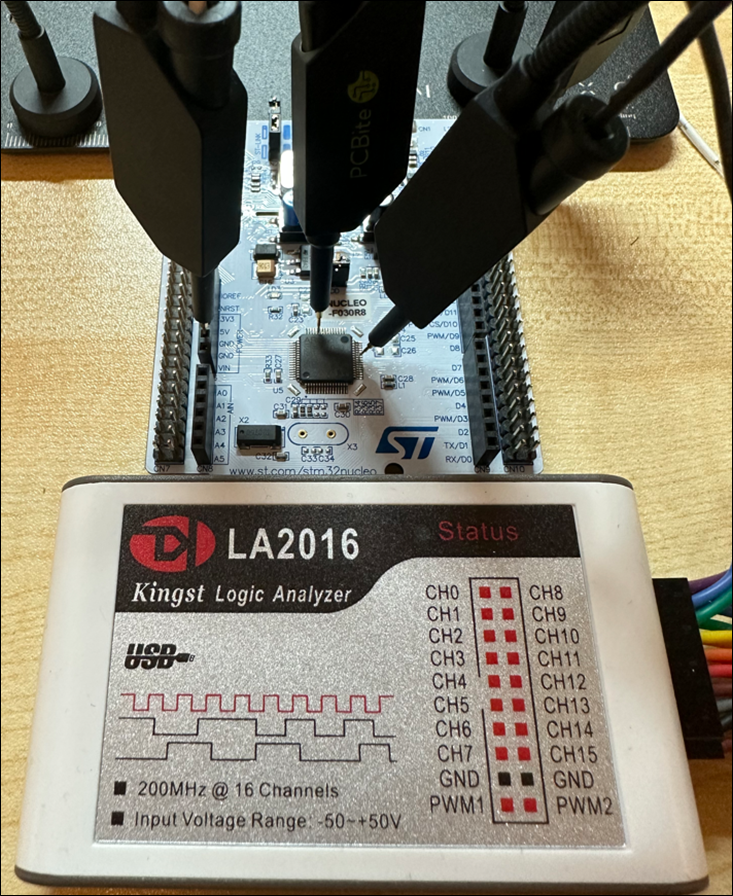
Iot Secure Development Guide Pen Test Partners This guide deals with threat modelling and early stages of development so that security issues and controls are identified before committing to manufacturing. current attack methods, and the pitfalls we find in embedded designs, have been highlighted so that a finished product is as secure as it can be. The owasp iot security testing guide (istg) provides a comprehensive methodology for penetration tests in the iot field, offering flexibility to adapt innovations, and developments in the iot market while still ensuring comparability of test results.
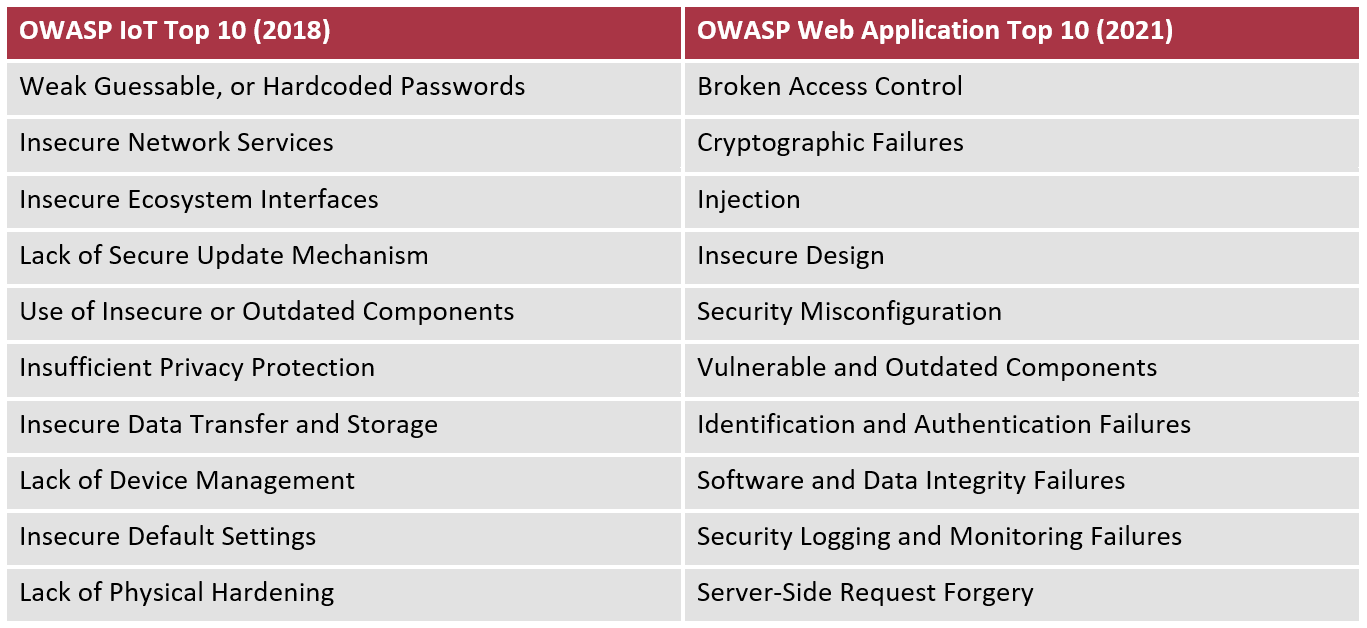
Iot Secure Development Guide Pen Test Partners The guide provides an understanding of communication between manufacturers and operators of iot devices as well as penetration testing teams that’s facilitated by establishing a common terminology. Learn how iot penetration testing secures connected devices and helps meet compliance with the eu cra, hipaa, and u.s. cyber trust mark. Security penetration testing, or pen testing, can be a useful but often misunderstood security test method, particularly by companies who are new to security, so what is a pen test, is it suitable for iot embedded products, and when should it be used?. This list identifies the most essential iot security threats and vulnerabilities that should be addressed during iot pen testing. the following test scenarios are included in the owasp top 10 for iot pentest.

Iot Secure Development Guide Pen Test Partners Security penetration testing, or pen testing, can be a useful but often misunderstood security test method, particularly by companies who are new to security, so what is a pen test, is it suitable for iot embedded products, and when should it be used?. This list identifies the most essential iot security threats and vulnerabilities that should be addressed during iot pen testing. the following test scenarios are included in the owasp top 10 for iot pentest. Packages can be modified and expanded to suit individual testing needs; indeed, they may include expedited report delivery, executive reporting, vulnerability re testing, and even options to incentivize greater vulnerability discovery. Sec556 equips security professionals with comprehensive skills to identify, assess, and exploit iot device security mechanisms across diverse technological ecosystems. this course is perfect to learn essential contents of iot pen testing. In this tech talk, aaron guzman and luca pascal rotsch will present their owasp iot security testing guide (istg) project. version 1.0.0 of this guide was published on march 1, providing a comprehensive methodology for penetration testing in the iot field. Iot pentesting methodology refers to a structured approach for evaluating the security of iot systems by simulating real world attacks. the goal is to identify vulnerabilities across devices, gateways, networks, and cloud systems to strengthen their security.
Comments are closed.