Iot Devices And Cybersecurity Threats Techvidvan

Iot Devices And Cybersecurity Threats Techvidvan Iot devices are revolutionizing our daily lives and how companies operate. but with modern tech innovations come cybersecurity risks. Here are the eight common iot vulnerabilities and seven external threats that pose the most significant risks. 1. an expanding attack surface. one of the biggest threats to an organization's ability to secure its iot environment is its sheer scale.

Introduction To Iot Techvidvan Iot Tutorial Big Data To analyze common threats targeting iot environments, including malware, denial of service (dos) ddos attacks, data breaches, and advanced persistent threats, and assess their potential impact on iot systems. Survey [74] provides an exhaustive examination of iot security in the ai era, encompassing cyber and physical security threats. it categorizes iot security challenges into device level, network level, data level, and privacy related issues, exploring ai based techniques such as ml, dl, and natural language processing to enhance iot security. This research article explores the distinct security challenges posed by iot devices and proposes effective strategies to mitigate these risks. The implications for broader iot security have been highlighted, as the challenges faced in underwater sensor networks mirror those encountered in many resource limited iot devices deployed in hostile environments.

Securing Iot Devices Against Cyber Threats This research article explores the distinct security challenges posed by iot devices and proposes effective strategies to mitigate these risks. The implications for broader iot security have been highlighted, as the challenges faced in underwater sensor networks mirror those encountered in many resource limited iot devices deployed in hostile environments. To combat this escalating threat landscape, security experts look toward innovative and trending technologies that offer promising solutions. this blog discusses the iot threat landscape and the impact that vulnerabilities can have on systems, data, and privacy. Explore the top 10 iot security risks, effective mitigation strategies, and best practices to secure iot devices against cyber threats. The easiest way to pick a threat to an iot device is its vulnerability. companies that provide iot based solutions begin by addressing this issue first before focusing on the underlying software. This paper aims to explore the various security threats associated with iot, analyze the inherent challenges in securing iot environments, and propose effective countermeasures to mitigate these risks.
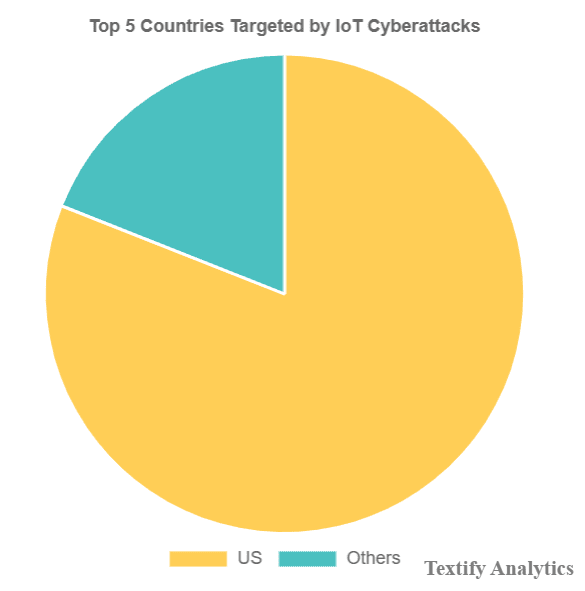
How To Protect Iot Devices From Cybersecurity Threats Textify Analytics To combat this escalating threat landscape, security experts look toward innovative and trending technologies that offer promising solutions. this blog discusses the iot threat landscape and the impact that vulnerabilities can have on systems, data, and privacy. Explore the top 10 iot security risks, effective mitigation strategies, and best practices to secure iot devices against cyber threats. The easiest way to pick a threat to an iot device is its vulnerability. companies that provide iot based solutions begin by addressing this issue first before focusing on the underlying software. This paper aims to explore the various security threats associated with iot, analyze the inherent challenges in securing iot environments, and propose effective countermeasures to mitigate these risks.
Comments are closed.