Iot Cyber Security Vulnerabilities And Threats

Understanding What Are Iot Vulnerabilities And How To Address Them Here are the eight common iot vulnerabilities and seven external threats that pose the most significant risks. 1. an expanding attack surface. one of the biggest threats to an organization's ability to secure its iot environment is its sheer scale. Internet of things (iot) device vulnerabilities can lead to data theft and sophisticated cyberattacks. discover the top iot vulnerabilities and how to best protect your network and devices.

Understanding What Are Iot Vulnerabilities And How To Address Them The sources assist in gathering articles pertaining to the impacts of cybersecurity on iot, the functionality of iot devices at the network and application layers, iot vulnerabilities, threats, and possible remedies. Explore the top 10 iot security risks, effective mitigation strategies, and best practices to secure iot devices against cyber threats. To analyze common threats targeting iot environments, including malware, denial of service (dos) ddos attacks, data breaches, and advanced persistent threats, and assess their potential impact on iot systems. This survey aims to provide a comprehensive analysis of vulnerabilities, threats, and defense mechanisms, specifically focusing on the integration of network and application layers within real time monitoring and decision making systems.
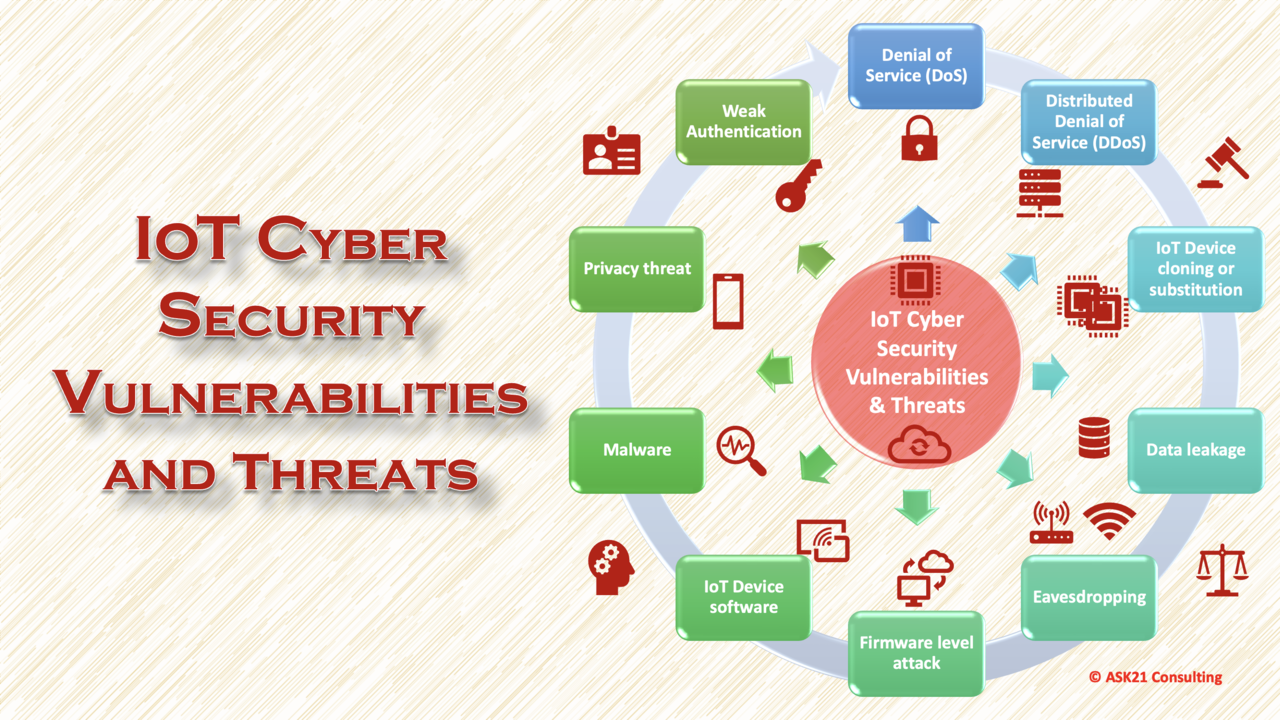
Iot Cyber Security Vulnerabilities And Threats To analyze common threats targeting iot environments, including malware, denial of service (dos) ddos attacks, data breaches, and advanced persistent threats, and assess their potential impact on iot systems. This survey aims to provide a comprehensive analysis of vulnerabilities, threats, and defense mechanisms, specifically focusing on the integration of network and application layers within real time monitoring and decision making systems. Vulnerabilities in iot devices may allow cyber criminals to hijack them and launch attacks against critical systems. cyber criminals often target and exploit recognized weak points in iot devices, converting them into compromised networks known as iot botnets. This survey paper delves into the diverse array of security threats faced by iot devices and networks, ranging from data breaches and unauthorized access to physical tampering and denial of service attacks. These vulnerabilities make iot devices susceptible to unauthorized access, compromise by attackers, and data breaches. they can range from inadequate user authentication mechanisms to insecure networking protocols and lack of security updates. This paper presents a comprehensive review of cybersecurity threats affecting iot networks and surveys contemporary solutions designed to mitigate these vulnerabilities.
Comments are closed.