Intruders In The Library Exploring Dll Hijacking

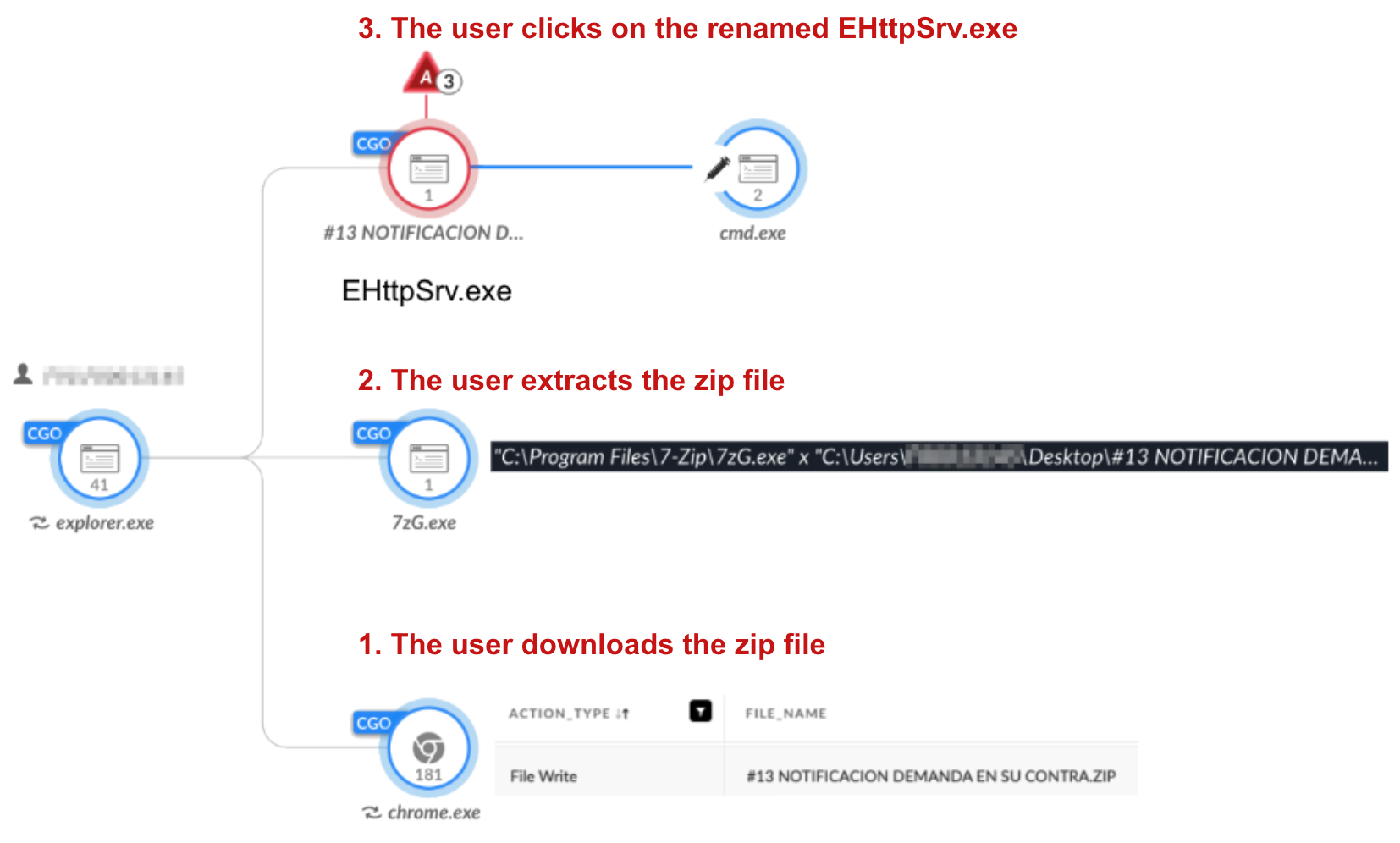
Intruders In The Library Exploring Dll Hijacking Dynamic link library (dll) hijacking remains a popular technique to run malware. we address its evolution using examples from the realm of cybercrime and more. Dynamic link library (dll) hijacking remains a popular technique to run malware. we address its evolution using examples from the realm of cybercrime and more. the post intruders in the library: exploring dll hijacking appeared first on unit 42.

Intruders In The Library Exploring Dll Hijacking #statelytaurus (aka #mustangpanda), chinese apts and cybercrime groups targeting victims in south america — they are all connected by their use of dll hijacking, a well established and. Dll hijacking happens when a windows app loads the wrong dll, often from a user writable folder, letting attackers run code inside a trusted process. this guide explains the main variations (search order, sideloading, phantom dll), plus detection and prevention checklists. In this blog post, we will explore dll exploitation through hijacking and proxying, allowing our malicious dll to be loaded alongside the legitimate one without causing any runtime errors in the executable. ) executive summary dynamic link library (dll) hijacking is one of the oldest techniques that both threat actors and offensive.

Intruders In The Library Exploring Dll Hijacking In this blog post, we will explore dll exploitation through hijacking and proxying, allowing our malicious dll to be loaded alongside the legitimate one without causing any runtime errors in the executable. ) executive summary dynamic link library (dll) hijacking is one of the oldest techniques that both threat actors and offensive. Adversaries may execute their own malicious payloads by hijacking the search order that windows uses to load dlls. this search order is a sequence of special and standard search locations that a program checks when loading a dll. Dll search order hijacking: exploiting the order in which windows searches for dlls, placing a malicious dll in a directory that gets searched before the legitimate one. In this guide, we will look at how windows loads code, how to find vulnerable applications using sysinternals process monitor, and how to exploit the flaw. dll stands for dynamic link library. dynamic linking means an application does not contain all the code it needs to run. The issue of dll hijacking arises when a harmful dll is strategically placed in one of these directories, ensuring it gets loaded before the authentic dll. a solution to prevent this is to ensure the application uses absolute paths when referring to the dlls it requires.
Intruders In The Library Exploring Dll Hijacking Adversaries may execute their own malicious payloads by hijacking the search order that windows uses to load dlls. this search order is a sequence of special and standard search locations that a program checks when loading a dll. Dll search order hijacking: exploiting the order in which windows searches for dlls, placing a malicious dll in a directory that gets searched before the legitimate one. In this guide, we will look at how windows loads code, how to find vulnerable applications using sysinternals process monitor, and how to exploit the flaw. dll stands for dynamic link library. dynamic linking means an application does not contain all the code it needs to run. The issue of dll hijacking arises when a harmful dll is strategically placed in one of these directories, ensuring it gets loaded before the authentic dll. a solution to prevent this is to ensure the application uses absolute paths when referring to the dlls it requires.
Intruders In The Library Exploring Dll Hijacking In this guide, we will look at how windows loads code, how to find vulnerable applications using sysinternals process monitor, and how to exploit the flaw. dll stands for dynamic link library. dynamic linking means an application does not contain all the code it needs to run. The issue of dll hijacking arises when a harmful dll is strategically placed in one of these directories, ensuring it gets loaded before the authentic dll. a solution to prevent this is to ensure the application uses absolute paths when referring to the dlls it requires.

Intruders In The Library Exploring Dll Hijacking
Comments are closed.