Introduction To Cryptography Omscs Notes
Cryptography Notes Pdf Cryptography Encryption Secret key cryptography uses a single key for encryption and decryption, which means that the sender and the receiver must possess the same key. public key cryptography uses two keys a public and a private key that are linked together mathematically. Welcome to lecture notes that are clear, organized, and forever free. i built omscs notes to share my notes with other students in the gatech omscs program. my notes are searchable, navigable, and, most importantly, free. i hope they help you on your journey here. join the party. sign up today.
Cryptography Notes Pdf Cryptography Key Cryptography We'll learn what security is in the context of symmetric key cryptography and our first symmetric key encryption scheme. this scheme will turn out to be the most efficient and secure encryption scheme in the world, but we'll also learn what its limitations are. We’ll learn what security is in the context of symmetric key cryptography and our first symmetric key encryption scheme. this scheme will turn out to be the most efficient and secure encryption scheme in the world, but we’ll also learn what its limitations are. Cryptographic algorithms, cryptanalysis, symmetric cryptography, public key cryptography, des, aes, rsa, hash and mac functions, digital signatures, pseudo random generators, cryptographic protocols, ssl tls, set. the tas were very helpful and prompt to answer questions. A graduate level introduction to modern cryptography, which focuses on the classical goals of cryptography, such as data privacy, authenticity and integrity. you will learn various cryptographic schemes and how they are used in practice. for example, you will learn what aes, cbc, rsa, dsa, tls stand for and how they "work".
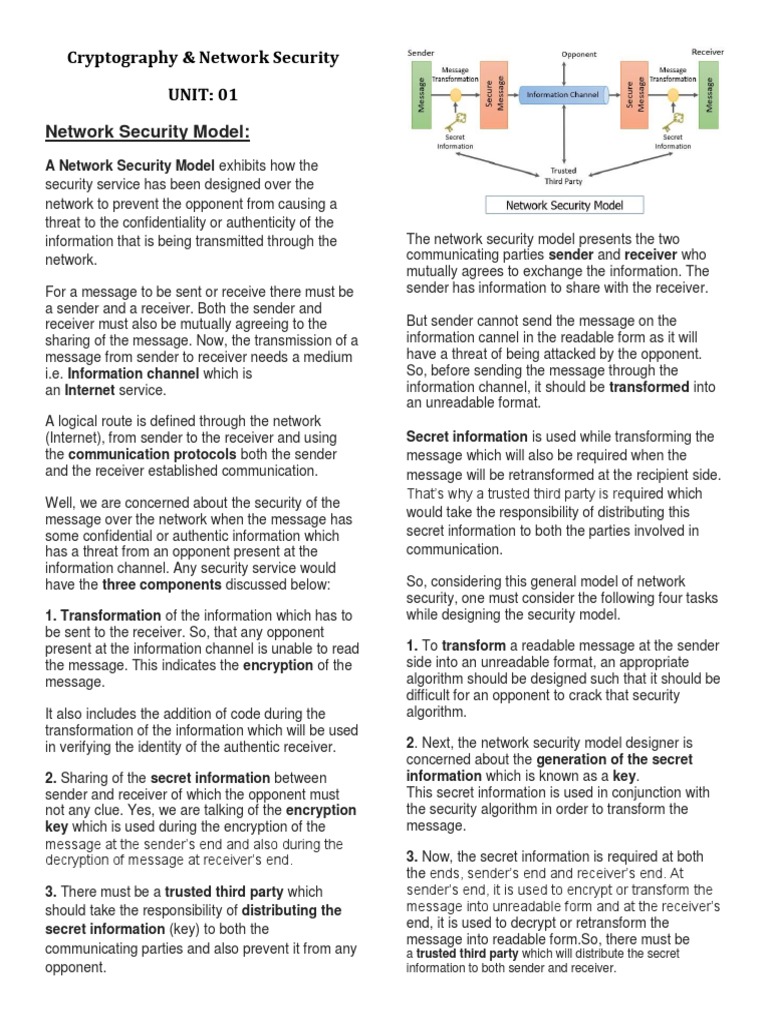
Cryptography Notes Pdf Cryptography Security Cryptographic algorithms, cryptanalysis, symmetric cryptography, public key cryptography, des, aes, rsa, hash and mac functions, digital signatures, pseudo random generators, cryptographic protocols, ssl tls, set. the tas were very helpful and prompt to answer questions. A graduate level introduction to modern cryptography, which focuses on the classical goals of cryptography, such as data privacy, authenticity and integrity. you will learn various cryptographic schemes and how they are used in practice. for example, you will learn what aes, cbc, rsa, dsa, tls stand for and how they "work". In computer based cryptography, it is the art of ciphering an easily understood message or “plain text” into one that cannot be easily deciphered (mel and baker 2001). the basic components for a cryptographic system are a ciphering engine, a key exchange mechanism, and a random number generator. Cryptography is the study of techniques in securing communication in the presence of adversaries who have access to the communication. encryption schemes are one of the primitives in cryptography; they designed for confi dentiality, and must be secure and correct. Some good sources for this material are the lecture notes by papadimitriou and vazirani (see home page of umesh vaziarani), lehman, leighton and meyer from mit course 6.042 “mathematics for computer science” (chapters 1 2 and 14 to 19 are particularly relevant), and the berkeley course cs 70. Cryptography studies techniques aimed at securing communication in the presence of adversaries. while encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that.

Cryptography Notes 5 23 Pdf Cryptanalysis Cryptography In computer based cryptography, it is the art of ciphering an easily understood message or “plain text” into one that cannot be easily deciphered (mel and baker 2001). the basic components for a cryptographic system are a ciphering engine, a key exchange mechanism, and a random number generator. Cryptography is the study of techniques in securing communication in the presence of adversaries who have access to the communication. encryption schemes are one of the primitives in cryptography; they designed for confi dentiality, and must be secure and correct. Some good sources for this material are the lecture notes by papadimitriou and vazirani (see home page of umesh vaziarani), lehman, leighton and meyer from mit course 6.042 “mathematics for computer science” (chapters 1 2 and 14 to 19 are particularly relevant), and the berkeley course cs 70. Cryptography studies techniques aimed at securing communication in the presence of adversaries. while encryption is probably the most prominent example of a crypto graphic problem, modern cryptography is much more than that.
Comments are closed.