Introduction To Computer System Security Pdf Systems Engineering

Introduction To Systems Engineering Pdf Systems Engineering System Week 11: security part i computer system engineering, lecture 20: introduction to security resource type: lecture notes pdf. Educating yourself about computer security can: enhance your own protection; contribute to security in your workplace; enhance the quality and safety of interpersonal and business transactions; improve overall security in cyberspace.

01 Introduction To Computer Security Pdf Information Security Suppose you design a system, derive some security claims, and discover every time that the system remains secure under all tests. is the system then secure? no, it is simply not proved insecure. The document is an introduction to a computer security course at mettu university, outlining its objectives, prerequisites, and key concepts related to information security, including security threats, vulnerabilities, and cryptography. Assignments– 45% (225 points) assignments [about 8 or 9] will be given that will involve using concepts learned in class related to system security, cryptography, malware, attacks, and mitigation(s). Next, we’ll look at some common attacks against computer systems, bypassing traditional os hardware security measures in the coming lectures, you will see some newer techniques to combat these threats.

Chap 1 Introduction To Computer Security Pdf Computer Security Assignments– 45% (225 points) assignments [about 8 or 9] will be given that will involve using concepts learned in class related to system security, cryptography, malware, attacks, and mitigation(s). Next, we’ll look at some common attacks against computer systems, bypassing traditional os hardware security measures in the coming lectures, you will see some newer techniques to combat these threats. This handbook provides assistance in securing computer based resources (including hardware, software, and information) by explaining important concepts, cost considerations, and interrelationships of security controls. The introduction of asymmetric cryptography revolutionized digital communication and laid the groundwork for modern security protocols, including digital certificates, vpns, and blockchain systems. Number of rounds – the number of rounds is regularly considered in design criteria, it just reflects the number of rounds to be suitable for an algorithm to make it more complex, in des we have 16 rounds ensuring it to be more secure while in aes we have 10 rounds which makes it more secure. A policy that states that students should not copy other students’ files, which is enforced by using file system access control mechanisms, is valid under the assumption that students don’t share passwords and that they set file access privileges correctly.
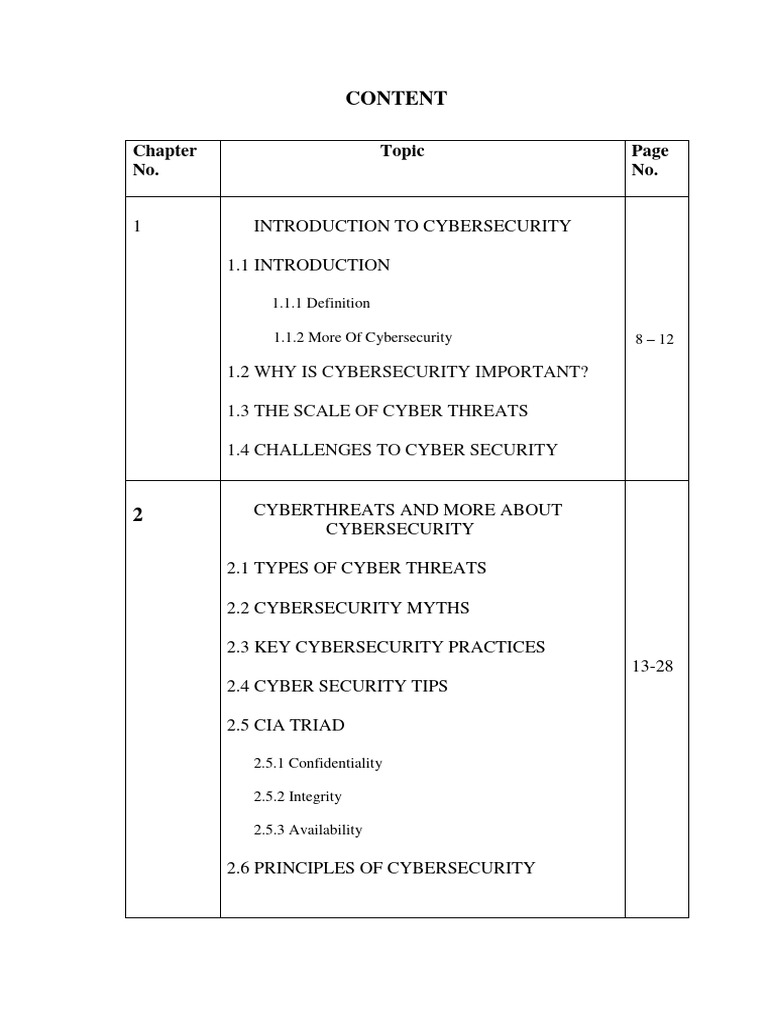
Introduction To Cybersecurity Pdf Security Computer Security This handbook provides assistance in securing computer based resources (including hardware, software, and information) by explaining important concepts, cost considerations, and interrelationships of security controls. The introduction of asymmetric cryptography revolutionized digital communication and laid the groundwork for modern security protocols, including digital certificates, vpns, and blockchain systems. Number of rounds – the number of rounds is regularly considered in design criteria, it just reflects the number of rounds to be suitable for an algorithm to make it more complex, in des we have 16 rounds ensuring it to be more secure while in aes we have 10 rounds which makes it more secure. A policy that states that students should not copy other students’ files, which is enforced by using file system access control mechanisms, is valid under the assumption that students don’t share passwords and that they set file access privileges correctly.

Introduction To Computer Security Pdf Malware Computer Virus Number of rounds – the number of rounds is regularly considered in design criteria, it just reflects the number of rounds to be suitable for an algorithm to make it more complex, in des we have 16 rounds ensuring it to be more secure while in aes we have 10 rounds which makes it more secure. A policy that states that students should not copy other students’ files, which is enforced by using file system access control mechanisms, is valid under the assumption that students don’t share passwords and that they set file access privileges correctly.

Fundamentals Of Computer Security Pdf Computer Network Computer
Comments are closed.