Introduction Hash Functions In Cryptography

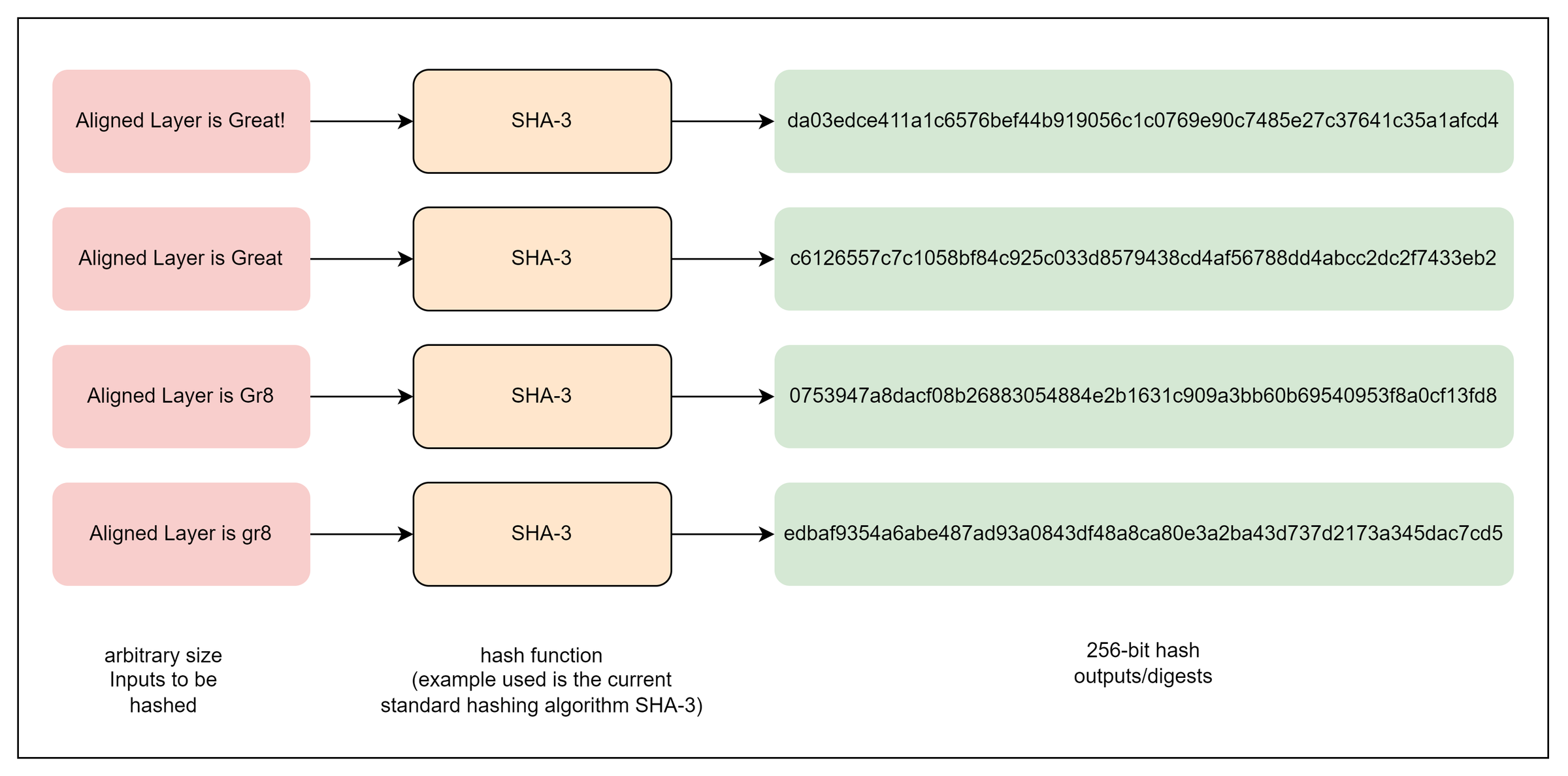
Cryptographic Hash Functions Pdf Cryptography Security Engineering In this introductory blog, we’ve explored the fundamental properties of cryptographic hash functions and their crucial role in securing digital systems. from understanding the surprising probability principles of the birthday paradox to the differences between regular and cryptographic hash functions. Cryptographic hash functions are intended to be fast, deterministic, and one way, meaning that even a minor change in input yields a very different hash. these functions are important for securing information digitally by allowing data verification and authentication.

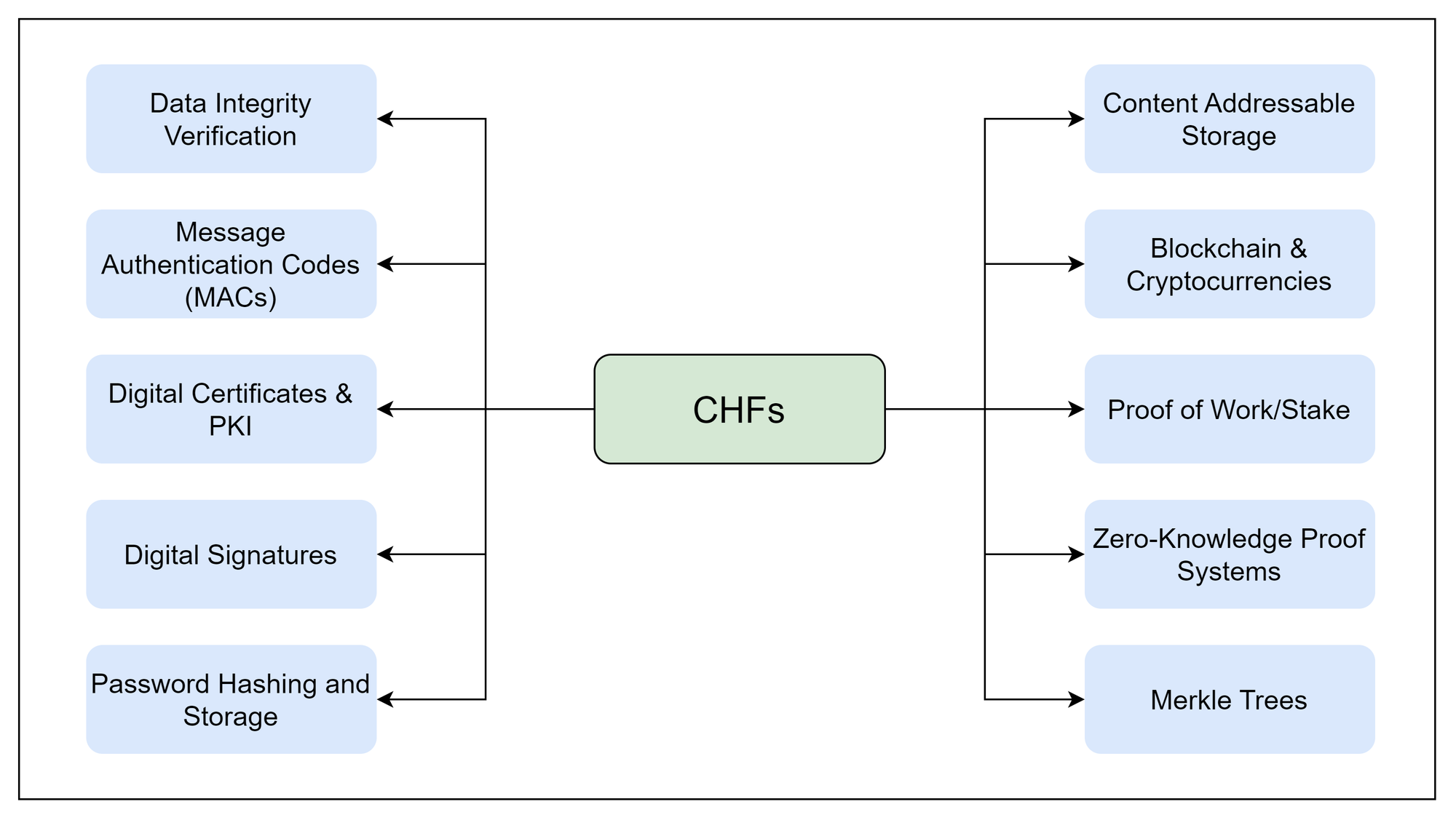
M 3 Cryptographic Hash Functions Pdf Public Key Cryptography Key points of hash functions hash functions are mathematical operations that "map" or change a given collection of data into a fixed length bit string that is referred to as the "hash value." hash functions have a variety of complexity and difficulty levels and are used in cryptography. Explore the in depth guide on hashing and hash functions. common examples, working, benefits and algorithms. Hash functions are a fundamental component in the field of cryptography, playing a crucial role in ensuring the security and integrity of data. in this article, we will explore the definition, properties, and applications of hash functions in cryptography. Cryptographic hash functions are used in message authentication codes (macs) for data integrity, digital signatures, password protection, key derivation, among other applications.

Unit 4 Cryptographic Hash Functions And Digital Signature Pdf Hash functions are a fundamental component in the field of cryptography, playing a crucial role in ensuring the security and integrity of data. in this article, we will explore the definition, properties, and applications of hash functions in cryptography. Cryptographic hash functions are used in message authentication codes (macs) for data integrity, digital signatures, password protection, key derivation, among other applications. This article will discuss the basic ideas and security considerations underpinning cryptographic hash functions and outline potential vulnerabilities from the advent of quantum computing. A cryptographic hash function is a type of mathematical formula that transforms a piece of information (for example, a text, file, or password) into a short “fingerprint” of fixed length. The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message. Parallelhash: a variable length hash function that can hash very long messages in parallel nist recommended four types of sha 3 derived functions which are mentioned as follows:.
Introduction Hash Functions In Cryptography This article will discuss the basic ideas and security considerations underpinning cryptographic hash functions and outline potential vulnerabilities from the advent of quantum computing. A cryptographic hash function is a type of mathematical formula that transforms a piece of information (for example, a text, file, or password) into a short “fingerprint” of fixed length. The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message. Parallelhash: a variable length hash function that can hash very long messages in parallel nist recommended four types of sha 3 derived functions which are mentioned as follows:.
Introduction Hash Functions In Cryptography The essence of the use of a hash function for message integrity is as follows. the sender computes a hash value as a function of the bits in the message and transmits both the hash value and the message. Parallelhash: a variable length hash function that can hash very long messages in parallel nist recommended four types of sha 3 derived functions which are mentioned as follows:.
Comments are closed.