Introducing Runtime Based Vulnerability Management

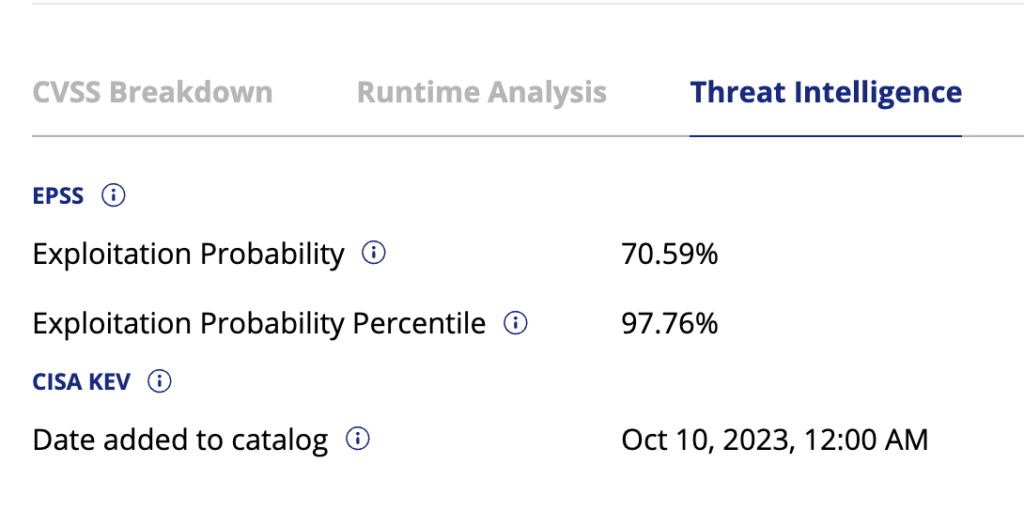
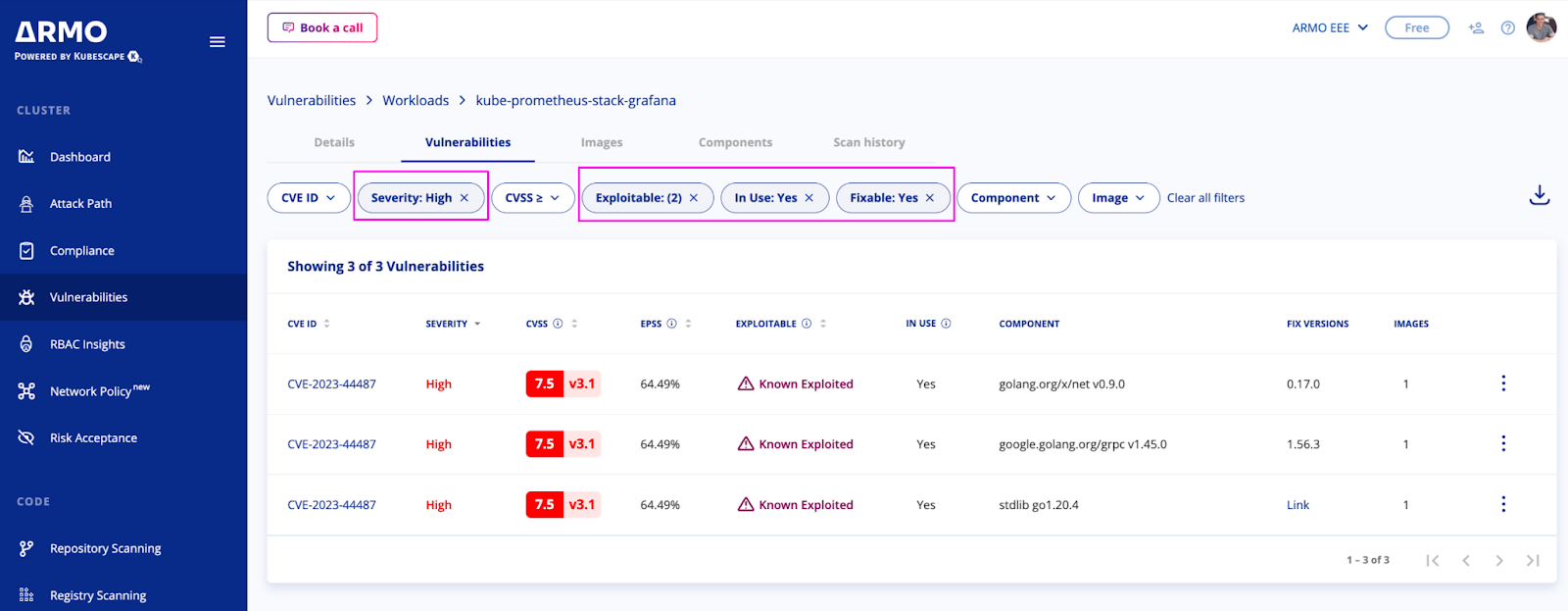
Risk Based Vulnerability Management Pdf Armo platform enables precise vulnerability prioritization by considering workload context, exploitability, severity, runtime analysis, and fixability. this comprehensive approach ensures that you address the most critical vulnerabilities first, minimizing potential risks to your infrastructure. That’s why more security teams are starting vulnerability management at runtime. runtime vulnerability management (rvm) has emerged as a more effective way to understand what is truly risky within your environment based on how software actually behaves when it runs.
Introducing Runtime Based Vulnerability Management Struggling to manage vulnerabilities in your kubernetes environment? you’re not alone. traditional vulnerability management tools often leave security teams feeling overwhelmed and unsure of where to focus their efforts. What is runtime vulnerability management (rvm)? rvm is a security approach that detects real world software risks by observing how applications behave while running, regardless of whether they have known vulnerabilities (cves). Discover how jfrog runtime ensures end to end software supply chain security with fast discovery and intelligent analysis of potential threats in runtime environments. Sweet goes beyond static scoring to assess vulnerabilities based on their behavior and relevance in your specific cloud environment. by combining llms with real time runtime context, sweet evaluates the true risk and business impact of each vulnerability—so you can focus on what matters most.
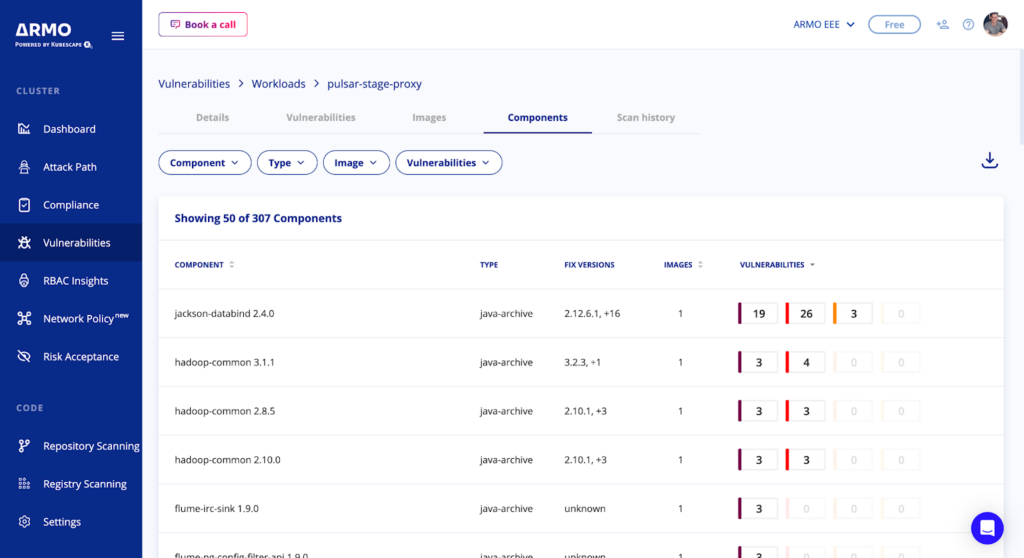
Introducing Runtime Based Vulnerability Management Discover how jfrog runtime ensures end to end software supply chain security with fast discovery and intelligent analysis of potential threats in runtime environments. Sweet goes beyond static scoring to assess vulnerabilities based on their behavior and relevance in your specific cloud environment. by combining llms with real time runtime context, sweet evaluates the true risk and business impact of each vulnerability—so you can focus on what matters most. Combining this data with specific runtime based vulnerable components lets you quickly spot exploitable vulnerabilities and take proactive steps to address them. Effective application security programs integrate ai with attack surface discovery, runtime validation, and risk based prioritization to manage real application risk. Runtime vulnerability management (rvm) represents the next evolution of vulnerability management. instead of starting with cve databases, rvm monitors how software actually behaves while running in your environment. Close knowledge gaps in your vulnerability management operations by mapping relationships between runtimes, binaries, packages, and cpes. discover how vulnz.io helps you understand and manage your security landscape. comprehensive tracking of all runtime environments and their dependencies.
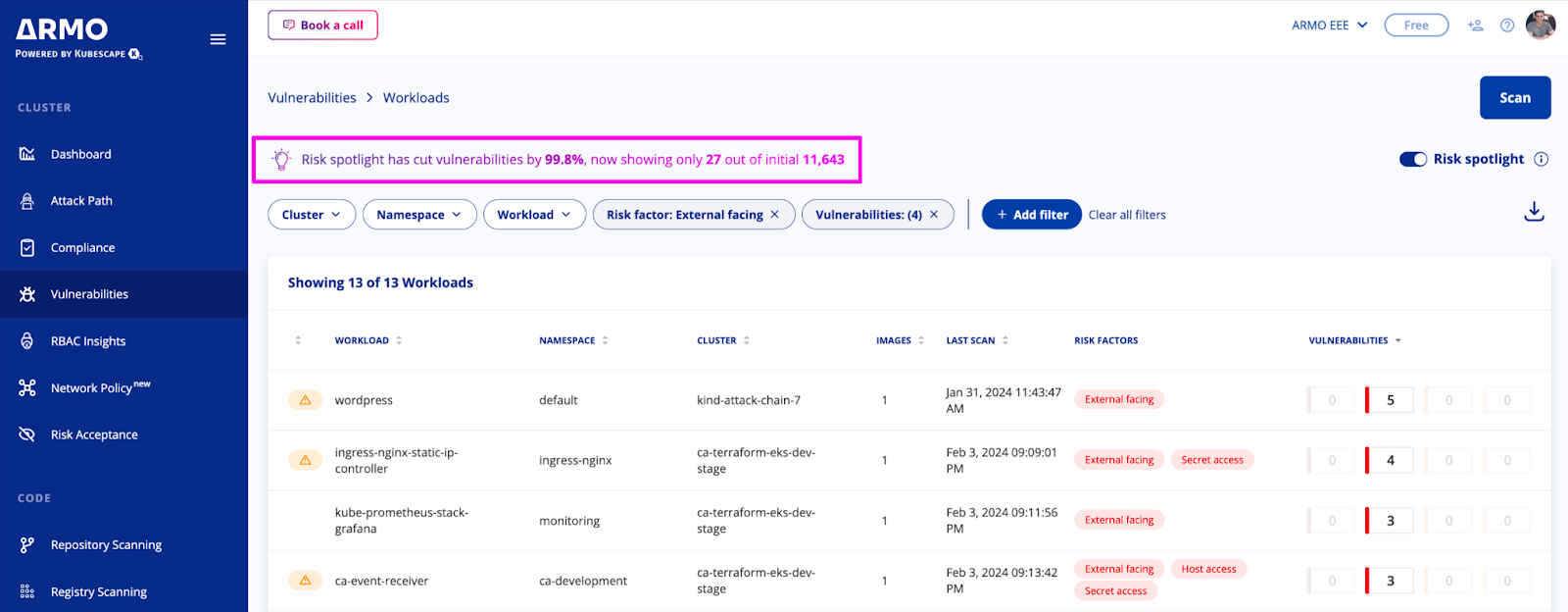
Introducing Runtime Based Vulnerability Management Combining this data with specific runtime based vulnerable components lets you quickly spot exploitable vulnerabilities and take proactive steps to address them. Effective application security programs integrate ai with attack surface discovery, runtime validation, and risk based prioritization to manage real application risk. Runtime vulnerability management (rvm) represents the next evolution of vulnerability management. instead of starting with cve databases, rvm monitors how software actually behaves while running in your environment. Close knowledge gaps in your vulnerability management operations by mapping relationships between runtimes, binaries, packages, and cpes. discover how vulnz.io helps you understand and manage your security landscape. comprehensive tracking of all runtime environments and their dependencies.
Introducing Runtime Based Vulnerability Management Runtime vulnerability management (rvm) represents the next evolution of vulnerability management. instead of starting with cve databases, rvm monitors how software actually behaves while running in your environment. Close knowledge gaps in your vulnerability management operations by mapping relationships between runtimes, binaries, packages, and cpes. discover how vulnz.io helps you understand and manage your security landscape. comprehensive tracking of all runtime environments and their dependencies.

Introducing Runtime Based Vulnerability Management
Comments are closed.