Introducing Diddht A New Did Method
Introducing Did Dht A New Did Method Youtube Join us for an exciting show & tell session where gabe cohen will introduce the groundbreaking did (decentralized identifier) method that he and daniel buchn. Did dht the did:dht method. home to the did dht method specification, and a reference implementation of a gateway server in go.
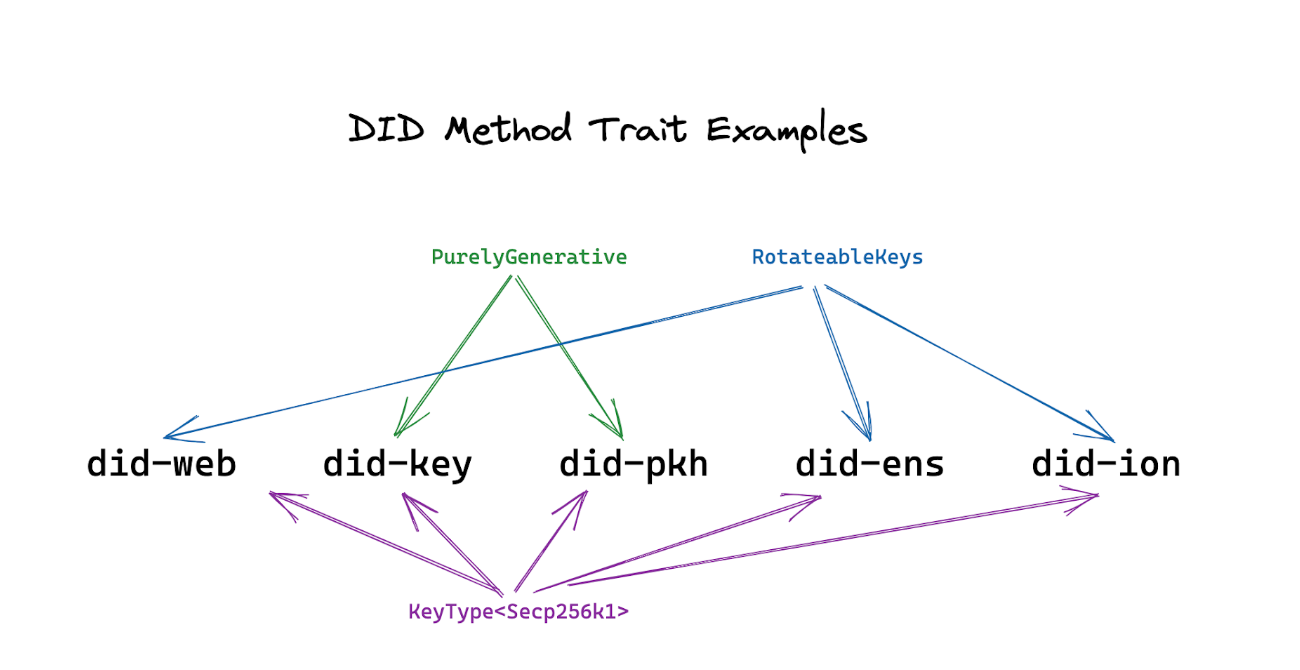
Upgradeable Decentralized Identity Did Method Traits Yes, i know what you’re thinking…another did method, really? but we >> believe it’s worth it for a truly decentralized and (relatively) simple >> method which does not rely on a blockchain. This table summarizes the did method specifications currently in development. the links will be updated as subsequent implementer’s drafts are produced. Some of you may already be familiar with did dht and why we’ve chosen to make it our default did method, but if not, or if you’re curious to find out more, read on to learn more about how the method was created, and how we’ve ended up here today. The did dht method specification is based on the dht used by bittorrent for reasons summarised in the abstract below. i’m posting here as a place for discussing how a did based on safe network might have advantages over this proposal, for example given sn’s goal of securing data permanently.

Ppt Designing And Planning Technology Enhanced Instruction Powerpoint Some of you may already be familiar with did dht and why we’ve chosen to make it our default did method, but if not, or if you’re curious to find out more, read on to learn more about how the method was created, and how we’ve ended up here today. The did dht method specification is based on the dht used by bittorrent for reasons summarised in the abstract below. i’m posting here as a place for discussing how a did based on safe network might have advantages over this proposal, for example given sn’s goal of securing data permanently. After analyzing several common did methods (web, ethr, key, sidetree, peer, keri, ens, cheqd) we realize that to fulfill the principles above, one needs to use either…. If options are not specified for create(), a did dht method implementation will generate a new ed25519 identity key and the did document will not include any additional verification method or service entries. This etho did method specification describes a new did method, that is, etho did and defines how ethereum blockchain stores etho dids and their corresponding did documents, and how to do crud operations on etho did documents. This document provides guidance to did method developers, related to serialization, cryptographic primitive selection, governance, and interoperability.
Ppt Designing And Planning Technology Enhanced Instruction Powerpoint After analyzing several common did methods (web, ethr, key, sidetree, peer, keri, ens, cheqd) we realize that to fulfill the principles above, one needs to use either…. If options are not specified for create(), a did dht method implementation will generate a new ed25519 identity key and the did document will not include any additional verification method or service entries. This etho did method specification describes a new did method, that is, etho did and defines how ethereum blockchain stores etho dids and their corresponding did documents, and how to do crud operations on etho did documents. This document provides guidance to did method developers, related to serialization, cryptographic primitive selection, governance, and interoperability.
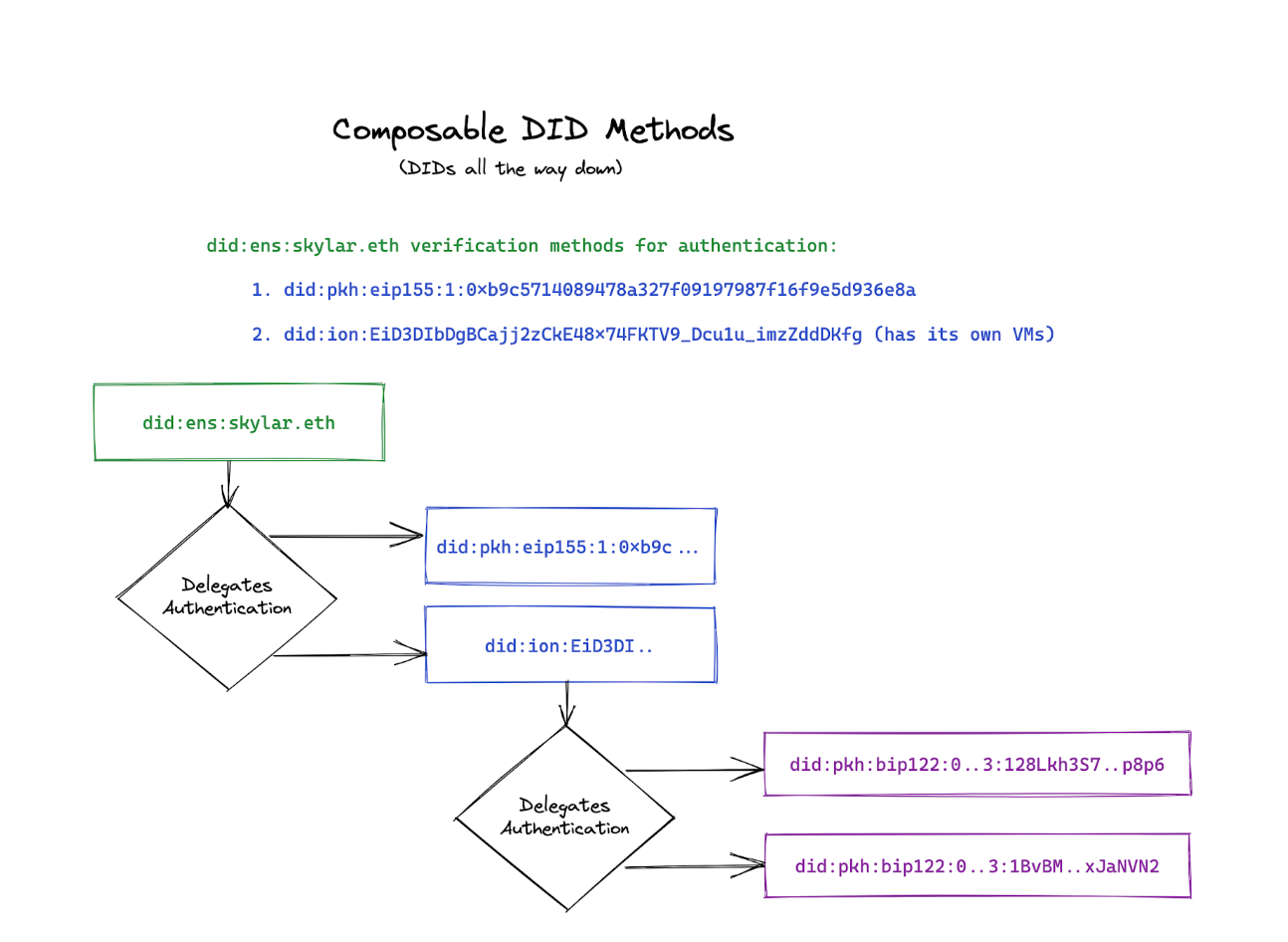
Upgradeable Decentralized Identity Did Method Traits This etho did method specification describes a new did method, that is, etho did and defines how ethereum blockchain stores etho dids and their corresponding did documents, and how to do crud operations on etho did documents. This document provides guidance to did method developers, related to serialization, cryptographic primitive selection, governance, and interoperability.
Comments are closed.