Internet Security Protocols 6 Different Internet Security Protocols
Internet Security Protocols Pdf This is a guide to internet security protocols. here we discuss the introduction and various internet security protocols, respectively. There are many protocols that exist that help in the security of data over the internet such as secure socket layer (ssl), transport layer security (tls). now, let us look at the various types of internet security protocols :.

Internet Security Protocols 6 Different Internet Security Protocols Learn about the network security protocols that are used to augment or replace insecure network protocols, lacking encryption, authentication, and more. Learn what security protocols are and why they matter in cyber security, network security, and information security with types, benefits, and best practices. Explore various types of network security protocols from basic tcp ip to advanced kerberos and tacacs to strengthen your organization's cybersecurity. Learn about the most common network security protocols including ipsec, ssl tls, and https.
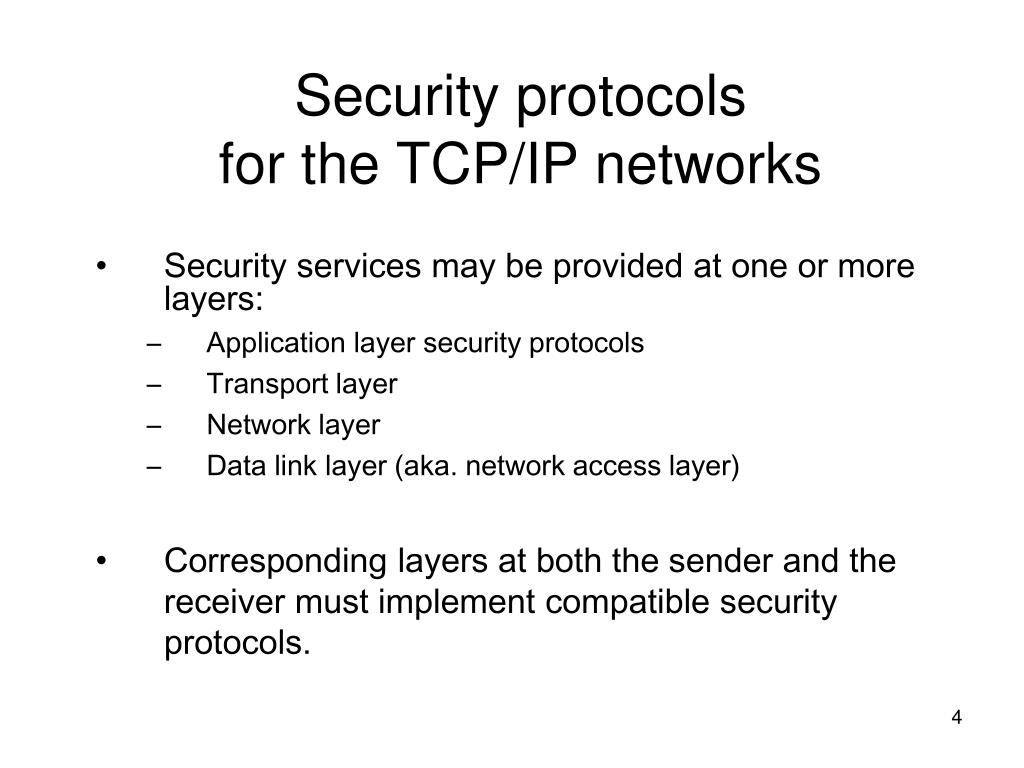
Internet Security Protocols Chapters 5 Outline Security Protocols Explore various types of network security protocols from basic tcp ip to advanced kerberos and tacacs to strengthen your organization's cybersecurity. Learn about the most common network security protocols including ipsec, ssl tls, and https. (ietf). it provides security at network level and helps to create authenticated and confidential packets for ip layer. Both ipsec (internet protocol security) and vpns (virtual private networks) rely on a group of security protocols that work together to encrypt communication between devices, keeping data safe when you connect to public networks, such as unsecured wi fis. Learn how network security protocols like tls, ipsec, and ssh protect data with encryption, authentication & integrity. Below are the leading network security protocols you should be familiar with. knowing that these protocols perform authentication, encryption, and message integrity is a fundamental first step in understanding network security protocols.
A Beginner S Guide To Network Security Protocols (ietf). it provides security at network level and helps to create authenticated and confidential packets for ip layer. Both ipsec (internet protocol security) and vpns (virtual private networks) rely on a group of security protocols that work together to encrypt communication between devices, keeping data safe when you connect to public networks, such as unsecured wi fis. Learn how network security protocols like tls, ipsec, and ssh protect data with encryption, authentication & integrity. Below are the leading network security protocols you should be familiar with. knowing that these protocols perform authentication, encryption, and message integrity is a fundamental first step in understanding network security protocols.

Trevonix Learn how network security protocols like tls, ipsec, and ssh protect data with encryption, authentication & integrity. Below are the leading network security protocols you should be familiar with. knowing that these protocols perform authentication, encryption, and message integrity is a fundamental first step in understanding network security protocols.
Ppt Internet Security Protocols Powerpoint Presentation Free
Comments are closed.