Instant Messaging System Pdf Instant Messaging Malware

14 Best Instant Messaging Software Of 2025 The results of this analysis will provide insights for individuals and organizations looking to choose a secure instant messaging app for their communication needs. In this paper, we present forensic acquisition and analysis of four voips: whatsapp, skype, viber and tango for both ios and android platforms. they are the most popular im apps as their total users already exceeded 1 billion [23][24][26].

From Irc To Instant Messaging The Rise Of Malware Communication Via In this paper, we pro pose a novel im malware detection and suppression mecha nism, honeyim, which guarantees almost zero false positive on detecting and blocking im malware in an enterprise like network. the detection of honeyim is based on the concept of honeypot. We review selected im worms and summarize their main characteristics, moti vating a brief overview of the network formed by im contact lists, and a discussion of theoretical consequences of worms in such networks. Many im applications use end to end encryption to secure your information and messages. although this seems like a high level of security when sending and receiving information, you should not rely entirely on end to end encryption to protect your data. Secure instant messengers are messaging applications designed from the ground up with security in mind. whatsapp, telegram, and signal are the most widely used, with several billion combined users.
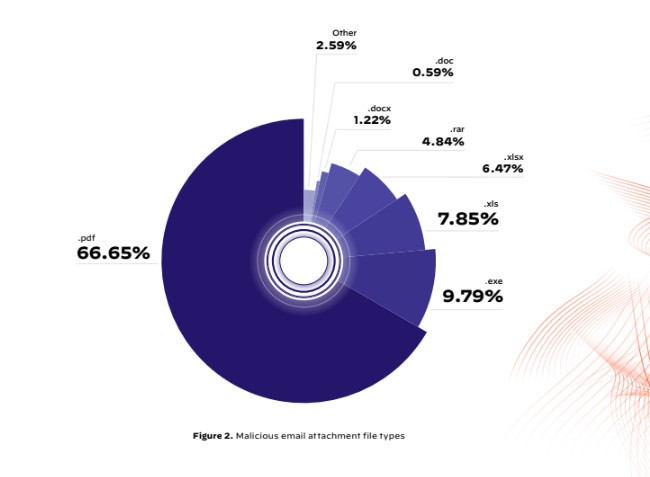
Pdfs As Malware Research Suggests How Some Benign Looking Files Could Many im applications use end to end encryption to secure your information and messages. although this seems like a high level of security when sending and receiving information, you should not rely entirely on end to end encryption to protect your data. Secure instant messengers are messaging applications designed from the ground up with security in mind. whatsapp, telegram, and signal are the most widely used, with several billion combined users. Instant messaging and security free download as pdf file (.pdf), text file (.txt) or read online for free. this strategic guide examines the risks of using instant messaging in businesses and how to mitigate them. In this paper we study a number of instant messenger ‘worms’ which spread by causing a putative victim to receive a message from one of their instant messaging ‘buddies’. this message includes a url which, if clicked, will download some malware onto the victim’s computer. We provide a survey on security features and threats to existing instant messaging (im) networks and discuss how currently available systems fail to provide adequate security in light of existing threats. In this article, we proposed a security approach for viber to safeguard user confidential data and sensitive information. the proposed approach involves two theoretical solutions: short message service (sms) authentication code and the physical hardware number to prevent illegal access to user data.
Bulk Messaging Malware In Facebook Messenger Kaspersky Official Blog Instant messaging and security free download as pdf file (.pdf), text file (.txt) or read online for free. this strategic guide examines the risks of using instant messaging in businesses and how to mitigate them. In this paper we study a number of instant messenger ‘worms’ which spread by causing a putative victim to receive a message from one of their instant messaging ‘buddies’. this message includes a url which, if clicked, will download some malware onto the victim’s computer. We provide a survey on security features and threats to existing instant messaging (im) networks and discuss how currently available systems fail to provide adequate security in light of existing threats. In this article, we proposed a security approach for viber to safeguard user confidential data and sensitive information. the proposed approach involves two theoretical solutions: short message service (sms) authentication code and the physical hardware number to prevent illegal access to user data.
National Cyber Security Authority Instant Messaging Services The We provide a survey on security features and threats to existing instant messaging (im) networks and discuss how currently available systems fail to provide adequate security in light of existing threats. In this article, we proposed a security approach for viber to safeguard user confidential data and sensitive information. the proposed approach involves two theoretical solutions: short message service (sms) authentication code and the physical hardware number to prevent illegal access to user data.
Comments are closed.