Installing Rootkit Hunter
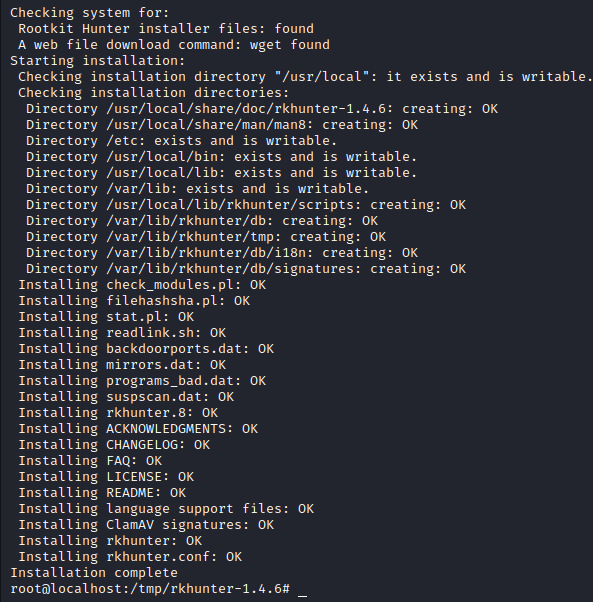
Installation Rootkit Hunter Rkhunter On Centos Knowledgebase Here’s a step by step guide on installing and using rootkit hunter in ubuntu 24.04 lts linux to scan local exploits, backdoors, and rootkits. To run rootkit hunter please install or upgrade to rootkit hunter version 1.4.6, and read the readme file.

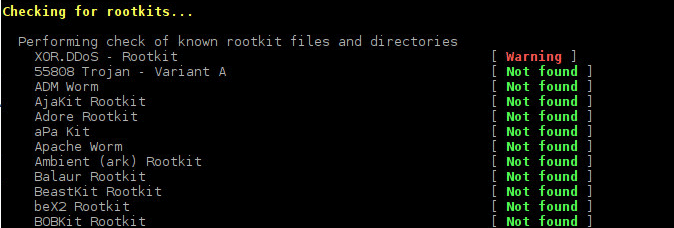
Rootkit Hunter Rkhunter Gratis Download Heise Complete guide to installing and configuring rkhunter for rootkit detection on ubuntu. in the ever evolving landscape of cybersecurity threats, rootkits remain one of the most dangerous and stealthy forms of malware. Rootkit hunter, commonly known as rkhunter, is a powerful tool designed to detect and remove rootkits, malware, and suspicious system behavior. in this guide, we’ll walk you through the process of installing and using rkhunter on debian linux to fortify your server’s security. Rkhunter, short for rootkit hunter, is an open source security tool that scans linux and unix systems for rootkits, backdoors, and other possible security threats. it is an essential addition to any security conscious user’s toolkit. In this article, we will show you how to install and configure rkhunter on ubuntu debian. before installing rkhunter, it is important to update the system to the latest version. to update the system, run the following commands: to install rkhunter, run the following command: this will install rkhunter and its dependencies on your system.
Linux Mint Community Rkhunter, short for rootkit hunter, is an open source security tool that scans linux and unix systems for rootkits, backdoors, and other possible security threats. it is an essential addition to any security conscious user’s toolkit. In this article, we will show you how to install and configure rkhunter on ubuntu debian. before installing rkhunter, it is important to update the system to the latest version. to update the system, run the following commands: to install rkhunter, run the following command: this will install rkhunter and its dependencies on your system. In this article, we’ll explain how to install rootkit hunter in linux (rkhunter). rootkit hunter is an open source unix linux based security monitoring and analyzing tool. In this article, we will explore how to install and configure rkhunter (rootkit hunter) on a linux system. rkhunter is an essential tool for the security of any server, as it allows the detection of rootkits, backdoors, and local exploits on unix systems. An open source security, monitoring and analyzing tool for posix compliant systems. rootkit hunter rkhunter. In general this can be achieved by installing rootkit hunter right after a clean operating system installation. rootkit hunter is not a reactive tool: it only enumerates encountered threats. it is up to you to read the log file and investigate suspicious activity.
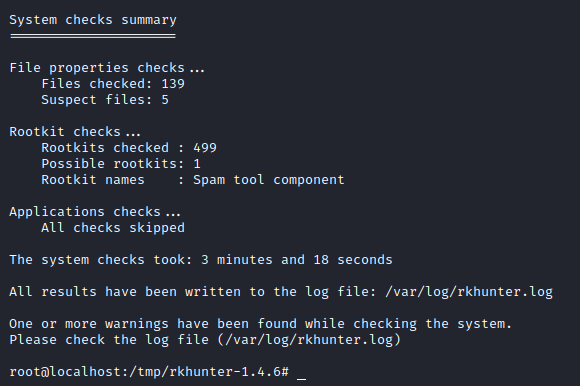
Scanning For Malware By Using Rootkit Hunter In Linux E2e Cloud In this article, we’ll explain how to install rootkit hunter in linux (rkhunter). rootkit hunter is an open source unix linux based security monitoring and analyzing tool. In this article, we will explore how to install and configure rkhunter (rootkit hunter) on a linux system. rkhunter is an essential tool for the security of any server, as it allows the detection of rootkits, backdoors, and local exploits on unix systems. An open source security, monitoring and analyzing tool for posix compliant systems. rootkit hunter rkhunter. In general this can be achieved by installing rootkit hunter right after a clean operating system installation. rootkit hunter is not a reactive tool: it only enumerates encountered threats. it is up to you to read the log file and investigate suspicious activity.
Scanning For Malware By Using Rootkit Hunter In Linux E2e Cloud An open source security, monitoring and analyzing tool for posix compliant systems. rootkit hunter rkhunter. In general this can be achieved by installing rootkit hunter right after a clean operating system installation. rootkit hunter is not a reactive tool: it only enumerates encountered threats. it is up to you to read the log file and investigate suspicious activity.
Comments are closed.