Installing A Validated Pattern
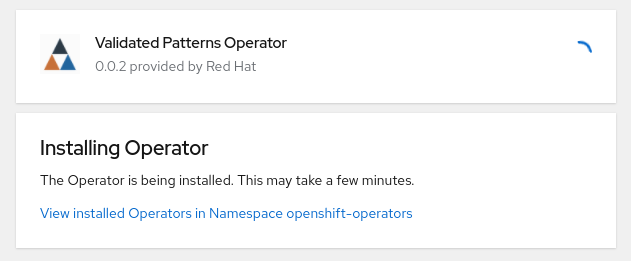
Using The Validated Pattern Operator Validated Patterns These are the steps run by make install and what each one does: the operator deploy task installs the validated patterns operator, which in turn creates a subscription for the openshift gitops operator and installs both the cluster and hub instances of it. This document details the system requirements, installation procedures, and prerequisite validation for the validated patterns ansible toolkit. it covers: openshift cluster specifications and valid.
Using The Validated Pattern Operator Validated Patterns In this resource, we’ll walk through how to prepare your environment to deploy a validated pattern, which will involve cluster sizing considerations and cluster creation. This pattern helps you get started with deploying confidential containers in openshift container platform. Validated patterns are field tested approaches for using, connecting, or integrating software products. they describe how to use features or data from one product with another. Validated patterns toolkit reference implementation and reusable toolkit for deploying validated patterns on openshift.

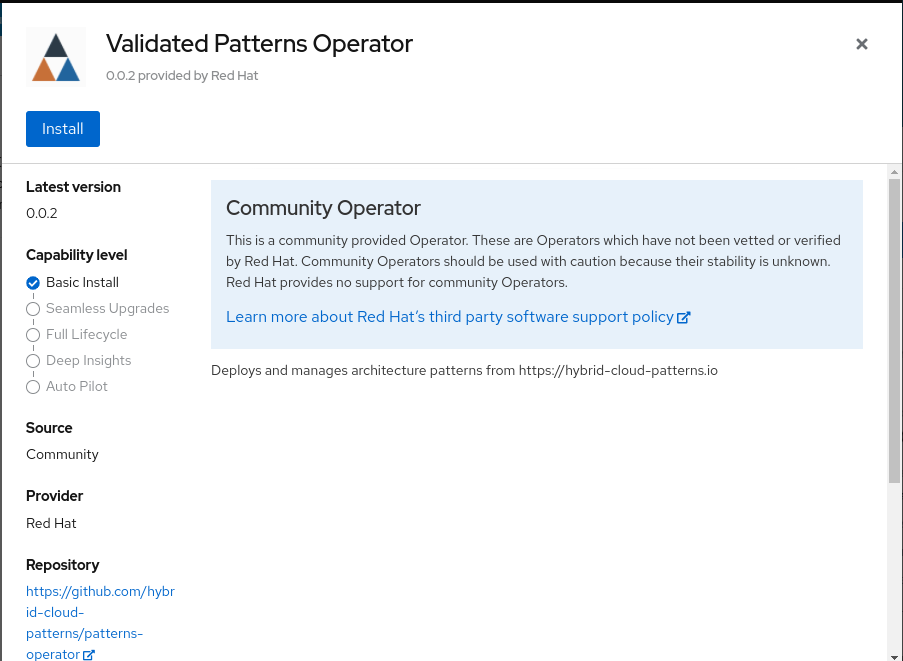
Patterns Validated Patterns Validated patterns are field tested approaches for using, connecting, or integrating software products. they describe how to use features or data from one product with another. Validated patterns toolkit reference implementation and reusable toolkit for deploying validated patterns on openshift. The validated pattern operator was developed in order to take advantage of the automation provided with the validated pattern framework. it allows users to deploy validated patterns using the red hat openshift console. The general workflow to deploy a pattern is to fork the repo into a private repository and make local changes there. the actual deployment can be started from the command line with a script in the local copy of the repo or from the hub cluster using the validated pattern operator. In this article, i detail the deployment of a credit card fraud detection stack using red hat validated patterns on ibm fusion—leveraging ibm fusion, redhat ai and a robust mlops pipelines for rapid results. In this blog, we will learn how container deployment patterns can be validated for zero trust. confidential computing leverages a trusted execution environment (tee) to protect data during processing, providing encryption not only for stored and transmitted data but also for data actively in use.
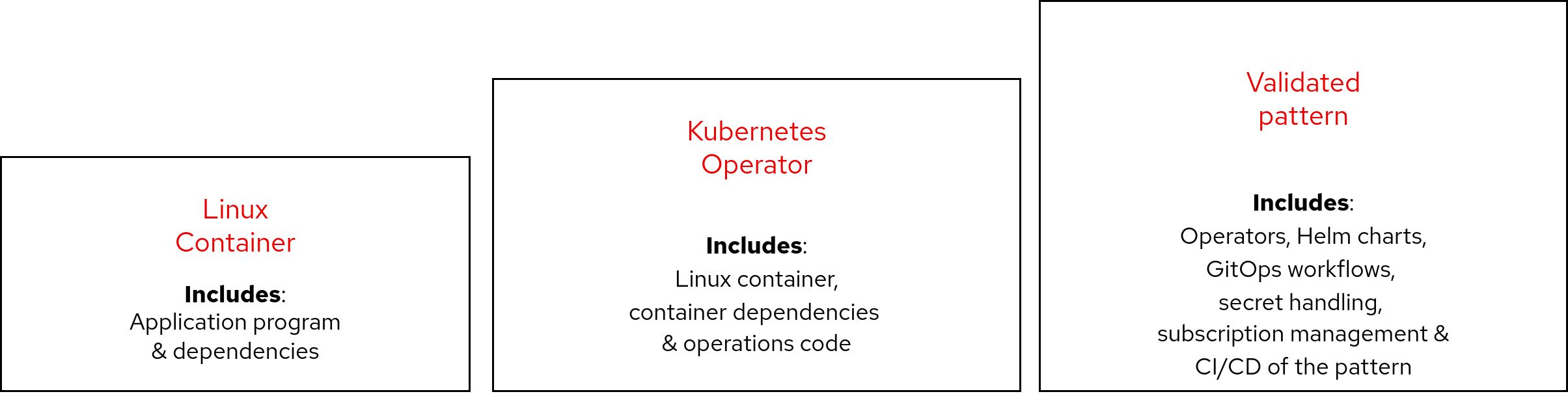
Background On Pattern Development Validated Patterns The validated pattern operator was developed in order to take advantage of the automation provided with the validated pattern framework. it allows users to deploy validated patterns using the red hat openshift console. The general workflow to deploy a pattern is to fork the repo into a private repository and make local changes there. the actual deployment can be started from the command line with a script in the local copy of the repo or from the hub cluster using the validated pattern operator. In this article, i detail the deployment of a credit card fraud detection stack using red hat validated patterns on ibm fusion—leveraging ibm fusion, redhat ai and a robust mlops pipelines for rapid results. In this blog, we will learn how container deployment patterns can be validated for zero trust. confidential computing leverages a trusted execution environment (tee) to protect data during processing, providing encryption not only for stored and transmitted data but also for data actively in use.

Validatedpattern Validatedpatterns E G Nadhan In this article, i detail the deployment of a credit card fraud detection stack using red hat validated patterns on ibm fusion—leveraging ibm fusion, redhat ai and a robust mlops pipelines for rapid results. In this blog, we will learn how container deployment patterns can be validated for zero trust. confidential computing leverages a trusted execution environment (tee) to protect data during processing, providing encryption not only for stored and transmitted data but also for data actively in use.
Comments are closed.