Inspecting Encrypted Network Traffic

Inspecting Encrypted Network Traffic Learn how to inspect encrypted traffic without breaking privacy. discover metadata analysis, behavioral detection, and machine learning methods to secure networks while staying compliant and privacy friendly. Overall, this reference could provide insights into statistical methods used for analyzing encrypted network traffic, detecting cyberattacks, and how the insecurity introduced by encryption affects the analysis and classification of network traffic.
Github Lymeiseu Encrypted Network Traffic Analysis Encrypted Network Discover how fidelis elevate uses deep session inspection® and metadata driven behavioral analysis to deliver full encrypted traffic inspection and monitoring—no decryption required, no privacy compromised. Encrypted traffic detection and classification is a critical domain in network security, increasingly essential in an era of pervasive encryption. this survey paper delves into integrating advanced machine learning (ml) and deep learning (dl) techniques to address the challenges of robust encryption methods and dynamic network behaviors. This paper presents a comprehensive survey of recent advancements in machine learning driven encrypted traffic analysis and classification. This in depth article explores how to analyze encrypted traffic using pcap files, focusing on monitoring ssl tls sessions for potential vulnerabilities without decrypting the data.
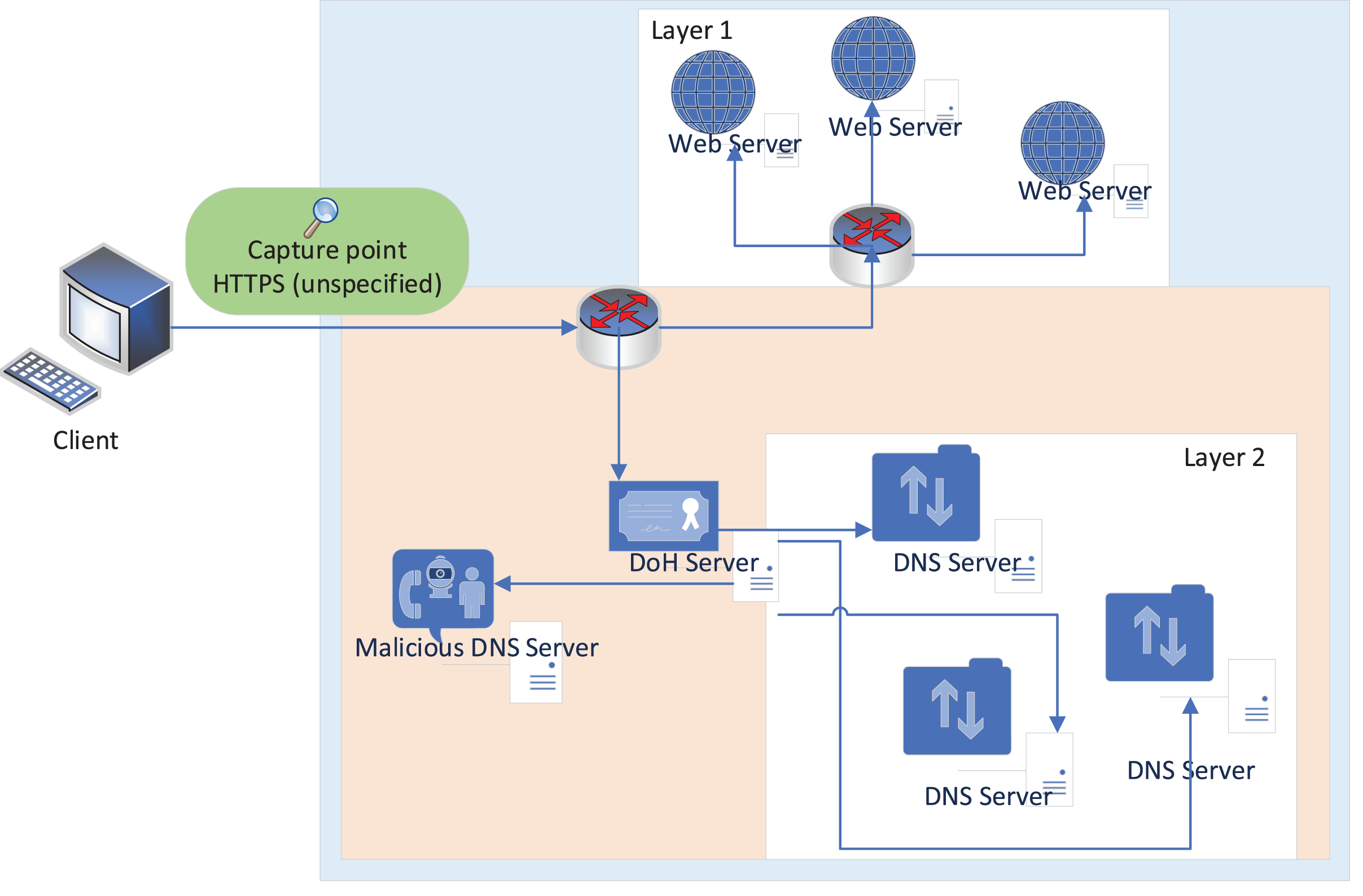
Encrypted Network Traffic Encrypted Network Traffic Analysis Fpyk This paper presents a comprehensive survey of recent advancements in machine learning driven encrypted traffic analysis and classification. This in depth article explores how to analyze encrypted traffic using pcap files, focusing on monitoring ssl tls sessions for potential vulnerabilities without decrypting the data. Do you want to analyze decrypted tls traffic in wireshark or let an ids, like suricata, snort or zeek, inspect the application layer data of potentially malicious tls encrypted traffic?. Inspecting tls encrypted traffic is a balancing act between security and visibility. by choosing the right tools and following best practices, we can gain valuable insights into network behavior without compromising privacy. This book provides a detailed study on sources of encrypted network traffic, methods and techniques for analyzing, classifying and detecting the encrypted traffic. However, it also poses challenges for threat detection, as malicious actors increasingly hide their activities within encrypted channels. this article explores key techniques for analyzing encrypted traffic, securing communications, and detecting anomalies.

Encrypted Traffic In Network Download Scientific Diagram Do you want to analyze decrypted tls traffic in wireshark or let an ids, like suricata, snort or zeek, inspect the application layer data of potentially malicious tls encrypted traffic?. Inspecting tls encrypted traffic is a balancing act between security and visibility. by choosing the right tools and following best practices, we can gain valuable insights into network behavior without compromising privacy. This book provides a detailed study on sources of encrypted network traffic, methods and techniques for analyzing, classifying and detecting the encrypted traffic. However, it also poses challenges for threat detection, as malicious actors increasingly hide their activities within encrypted channels. this article explores key techniques for analyzing encrypted traffic, securing communications, and detecting anomalies.

Encrypted Traffic Intelligence For Network Traffic Analysis This book provides a detailed study on sources of encrypted network traffic, methods and techniques for analyzing, classifying and detecting the encrypted traffic. However, it also poses challenges for threat detection, as malicious actors increasingly hide their activities within encrypted channels. this article explores key techniques for analyzing encrypted traffic, securing communications, and detecting anomalies.
Comments are closed.