Insider Threat Detection With Ml Techniques Pdf Machine Learning

Intrusion Detection Using Explainable Machine Learning Techniques Pdf This research paper presents an intelligent system for insider threat detection using machine learning (ml) techniques. the system employs user behavior analytics, real time log monitoring, and anomaly detection to identify suspicious activities. To combat insider threats, emerging natural language processing techniques are employed in conjunction with powerful machine learning classifiers, specifically xgboost and adaboost.
Github Shrii157 Insider Threat Detection Using Deep Learning The article discusses the use of machine learning techniques for detecting insider threats in cybersecurity, focusing on the challenges posed by authorized users who may engage in malicious activities. We precisely evaluate the performance of various supervised machine learning algorithms on a balanced dataset using the same feature extraction method. additionally, we explore the impact of hyperparameter tuning on performance within the balanced dataset. The principal interest of this proposed architecture of this research is to assess the capability of machine learning techniques in detecting insider threats in a corporate and organizational network. Insider threat detection is a broadly researched topic; a variety of solutions have been proposed: specifically, different learning techniques to facilitate early, more accurate threat detection.

Pdf Threat Detection In Iot Using Machine Learning Techniques The principal interest of this proposed architecture of this research is to assess the capability of machine learning techniques in detecting insider threats in a corporate and organizational network. Insider threat detection is a broadly researched topic; a variety of solutions have been proposed: specifically, different learning techniques to facilitate early, more accurate threat detection. The proposed framework, termed the insider threat explainable machine learning (it xml) framework, integrates the cross industry standard process for data mining (crisp dm) methodology with hidden markov models (hmm) to enhance proactive insider threat management and decision making. Abstract— insider threats pose significant risks to organizations by compromising sensitive data and resources. detecting these threats effectively necessitates robust machine learning (ml) techniques capable of managing complex and imbalanced datasets. T: insider threats pose a significant security challenge to organizational assets and sensitive information. this paper presents a novel approach to insider threat detection by categorizing features into several behavioral types, including time related, user related, proj. Due to their elusive nature, proactive strategies have been proposed of which detection using machine learning models has been favoured. the choice of algorithm, datasets and metrics are cornerstones of model performance and hence, need to be addressed.
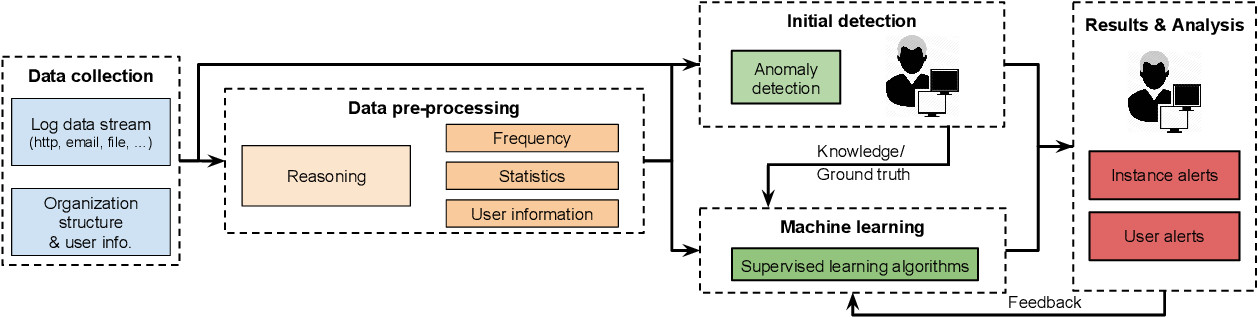
Figure 1 From Machine Learning Based Insider Threat Modelling And The proposed framework, termed the insider threat explainable machine learning (it xml) framework, integrates the cross industry standard process for data mining (crisp dm) methodology with hidden markov models (hmm) to enhance proactive insider threat management and decision making. Abstract— insider threats pose significant risks to organizations by compromising sensitive data and resources. detecting these threats effectively necessitates robust machine learning (ml) techniques capable of managing complex and imbalanced datasets. T: insider threats pose a significant security challenge to organizational assets and sensitive information. this paper presents a novel approach to insider threat detection by categorizing features into several behavioral types, including time related, user related, proj. Due to their elusive nature, proactive strategies have been proposed of which detection using machine learning models has been favoured. the choice of algorithm, datasets and metrics are cornerstones of model performance and hence, need to be addressed.

Pdf Ai Driven Cybersecurity Evaluating Machine Learning Models For T: insider threats pose a significant security challenge to organizational assets and sensitive information. this paper presents a novel approach to insider threat detection by categorizing features into several behavioral types, including time related, user related, proj. Due to their elusive nature, proactive strategies have been proposed of which detection using machine learning models has been favoured. the choice of algorithm, datasets and metrics are cornerstones of model performance and hence, need to be addressed.

Enhancing Cybersecurity Through Machine Learning Based Intrusion
Comments are closed.