Insecure Java Deserialization Pptx
Insecure Deserialization In Java It explains the serialization and deserialization processes, the concept of gadget classes that can be exploited, and how attackers can create self executing gadget chains. it also references resources for further information on the topic. download as a pptx, pdf or view online for free. Insecure deserialization.pptx free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. the document discusses insecure deserialization vulnerabilities.
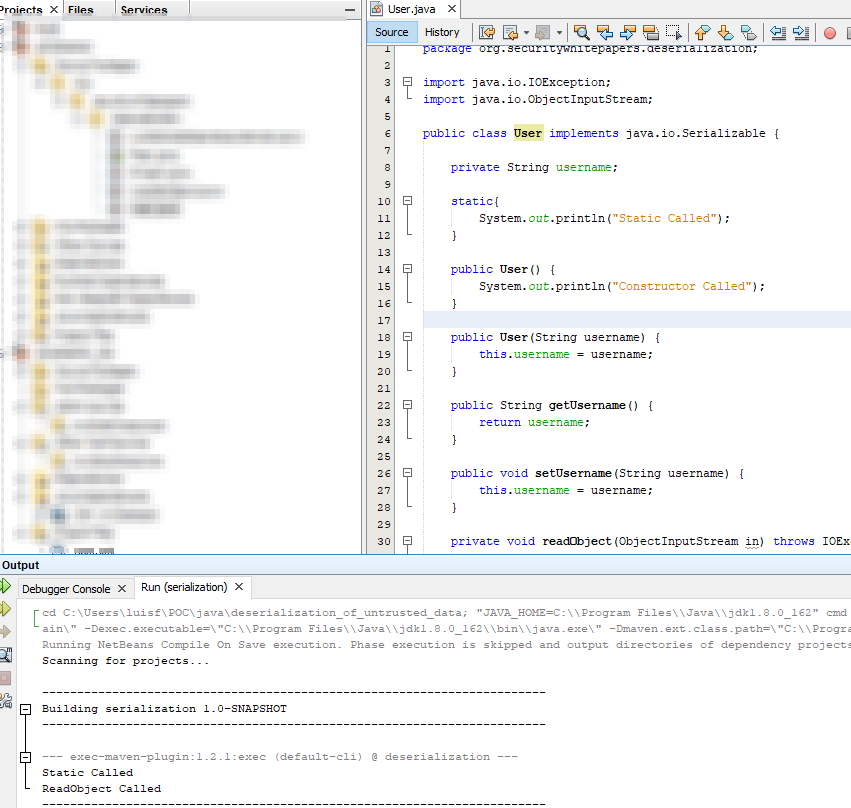
Insecure Deserialization In Java Owasp foundation web respository. contribute to owasp www chapter toronto development by creating an account on github. Dese is reverse of se where the seri data are converted into object so that we may use its properties. insecure deserialization if an attacker can control the serialized stream, the process of deserializing the stream of data could be exploited leading to application server compromise. insecure deserialization case study. Since deserialization can invoke class methods automatically, insecure implementations may allow remote code execution (rce). in this lab, we’ll focus on achieving rce by crafting a malicious serialized payload and injecting it into the application. To ensure that such objects (e.g., superuser) cannot be deserialized, we can override the readobject() method and mark it as final to throw an exception during the deserialization process. the readobject() method of java.io.objectinputstream is vulnerable.
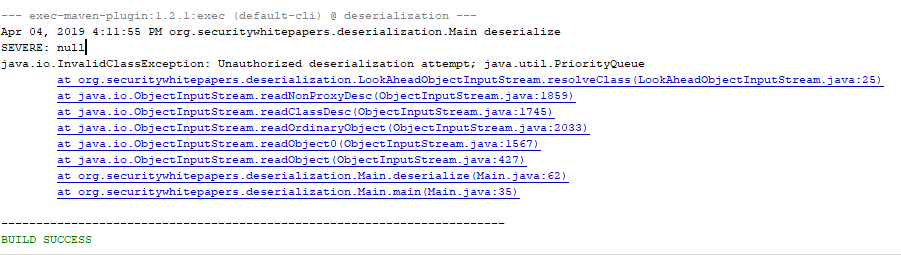
Insecure Deserialization In Java Since deserialization can invoke class methods automatically, insecure implementations may allow remote code execution (rce). in this lab, we’ll focus on achieving rce by crafting a malicious serialized payload and injecting it into the application. To ensure that such objects (e.g., superuser) cannot be deserialized, we can override the readobject() method and mark it as final to throw an exception during the deserialization process. the readobject() method of java.io.objectinputstream is vulnerable. In this section, we'll cover what insecure deserialization is and describe how it can potentially expose websites to high severity attacks. we'll highlight typical scenarios and demonstrate some widely applicable techniques using concrete examples of php, ruby, and java deserialization. In this post, we share the story behind the discovery, explain the risks of insecure deserialization, and highlight how a simple fix helped secure a vulnerable authentication endpoint. In this article, we’ve covered how an attacker may use deserialization to exploit a vulnerable system. in addition, we have covered some practices to maintain good security hygiene in a java system. Learn how an insecure deserialization attack works, and how to mitigate and remediate the vulnerability with real world examples from security experts.
Comments are closed.