Insecure Deserialization In Java And Its Exploitation

Insecure Deserialization Exploitation In Java Insecure deserialization is a type of vulnerability that arises when untrusted data is used to abuse the logic of an application’s deserialization process, allowing an attacker to execute code, manipulate objects, or perform injection attacks. Learn how 'insecure deserialization' vulnerability arises in java and how an attacker may use deserialization to exploit a vulnerable system.

Insecure Deserialization Exploitation In Java In this tutorial, we’ll explore how an attacker can use deserialization in java code to exploit a system. we’ll start by looking at some different approaches an attacker might use to exploit a system. In our blog, we have discussed the foundations of insecure deserialization. now in this blog, we’ll take a glance at multiple insecure deserialization exploitation in java. Java serialization is the process of converting a java object’s state into a byte stream, which can be stored or transmitted and later reconstructed (deserialized) back into the original object. In this section, we'll cover what insecure deserialization is and describe how it can potentially expose websites to high severity attacks. we'll highlight typical scenarios and demonstrate some widely applicable techniques using concrete examples of php, ruby, and java deserialization.

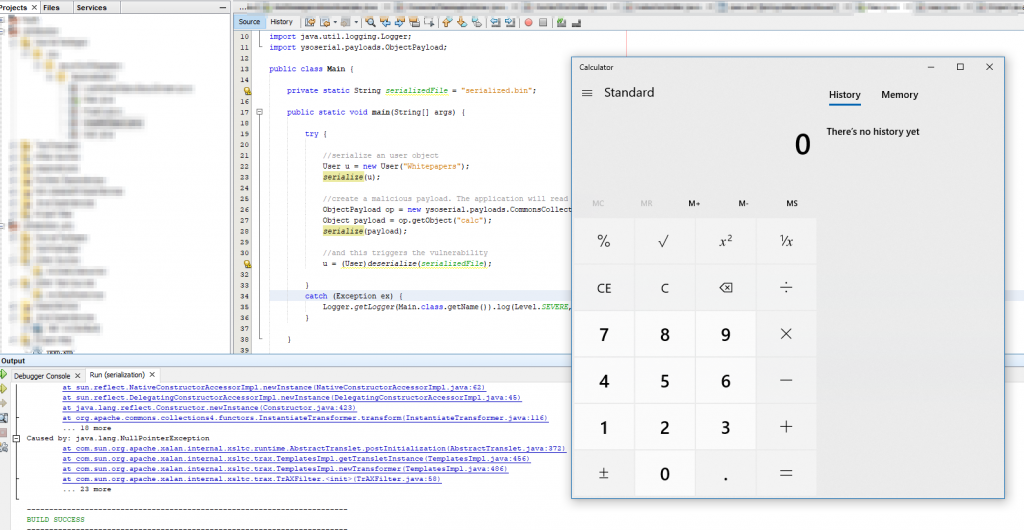
Insecure Deserialization Exploitation In Java Java serialization is the process of converting a java object’s state into a byte stream, which can be stored or transmitted and later reconstructed (deserialized) back into the original object. In this section, we'll cover what insecure deserialization is and describe how it can potentially expose websites to high severity attacks. we'll highlight typical scenarios and demonstrate some widely applicable techniques using concrete examples of php, ruby, and java deserialization. Master insecure deserialization exploitation across java, php, python, and . covers java gadget chains with ysoserial, php magic method abuse, python pickle rce, and binaryformatter gadget chains with detection techniques. In this post, we share the story behind the discovery, explain the risks of insecure deserialization, and highlight how a simple fix helped secure a vulnerable authentication endpoint. To ensure that such objects (e.g., superuser) cannot be deserialized, we can override the readobject() method and mark it as final to throw an exception during the deserialization process. the readobject() method of java.io.objectinputstream is vulnerable. Insecure deserialization is a type of vulnerability that arises when an attacker is able to manipulate the serialized object and cause unintended consequences in the program’s flow. this can cause dos, authentication bypass or even rce.
Insecure Deserialization In Java Master insecure deserialization exploitation across java, php, python, and . covers java gadget chains with ysoserial, php magic method abuse, python pickle rce, and binaryformatter gadget chains with detection techniques. In this post, we share the story behind the discovery, explain the risks of insecure deserialization, and highlight how a simple fix helped secure a vulnerable authentication endpoint. To ensure that such objects (e.g., superuser) cannot be deserialized, we can override the readobject() method and mark it as final to throw an exception during the deserialization process. the readobject() method of java.io.objectinputstream is vulnerable. Insecure deserialization is a type of vulnerability that arises when an attacker is able to manipulate the serialized object and cause unintended consequences in the program’s flow. this can cause dos, authentication bypass or even rce.
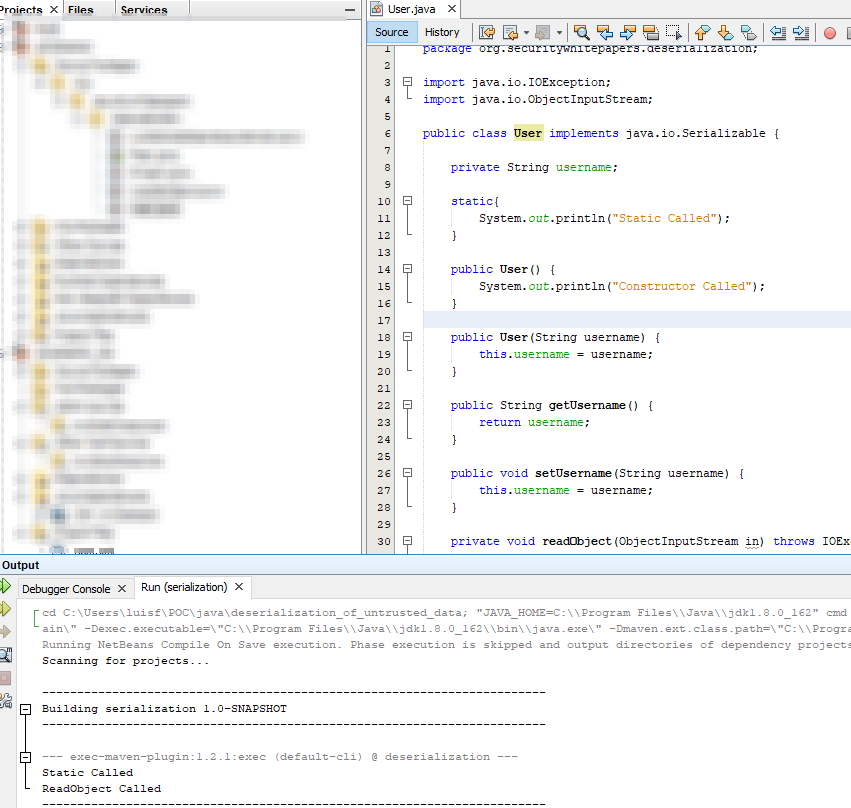
Insecure Deserialization In Java To ensure that such objects (e.g., superuser) cannot be deserialized, we can override the readobject() method and mark it as final to throw an exception during the deserialization process. the readobject() method of java.io.objectinputstream is vulnerable. Insecure deserialization is a type of vulnerability that arises when an attacker is able to manipulate the serialized object and cause unintended consequences in the program’s flow. this can cause dos, authentication bypass or even rce.
Insecure Deserialization In Java
Comments are closed.