Insecure Deserialization Attack Explained

Insecure Deserialization Attack Explained Cybernoz Cybersecurity News Insecure deserialization is a type of vulnerability that arises when untrusted data is used to abuse the logic of an application’s deserialization process, allowing an attacker to execute code, manipulate objects, or perform injection attacks. Another less understood but equally dangerous vulnerability associated with user input is insecure deserialisation. insecure deserialisation exploits occur when an application trusts.

Insecure Deserialization Explained With Examples Thehackerish In this section, we'll cover what insecure deserialization is and describe how it can potentially expose websites to high severity attacks. we'll highlight typical scenarios and demonstrate some widely applicable techniques using concrete examples of php, ruby, and java deserialization. Learn how an insecure deserialization attack works, and how to mitigate and remediate the vulnerability with real world examples from security experts. Insecure deserialization detect, understand, remediate insecure deserialization allows attackers to manipulate serialised objects to achieve remote code execution, privilege escalation, or injection attacks when the application deserialises untrusted data. Insecure deserialization is when untrusted serialized input is reconstructed into program objects without validation, enabling attackers to manipulate application logic or execute code.

Insecure Deserialization Explained With Examples Thehackerish Insecure deserialization detect, understand, remediate insecure deserialization allows attackers to manipulate serialised objects to achieve remote code execution, privilege escalation, or injection attacks when the application deserialises untrusted data. Insecure deserialization is when untrusted serialized input is reconstructed into program objects without validation, enabling attackers to manipulate application logic or execute code. Insecure deserialization occurs when an api reconstructs an object from untrusted data without validating its contents. attackers modify the serialized data to include malicious code that executes during the reconstruction process. A deserialization attack, specifically insecure deserialization, occurs when an application converts (or deserializes) a stream of data into a live object without ensuring the data is safe or trustworthy. Insecure deserialization is a serious vulnerability that can lead to remote code execution, injection attacks, and other critical security issues. it occurs when an application deserializes untrusted or maliciously crafted data without proper validation or sanitization. Insecure deserialization represents a significant security risk that arises when an application improperly handles the deserialization of untrusted data. this vulnerability can lead to a wide range of attacks, including remote code execution, privilege escalation, and data manipulation.
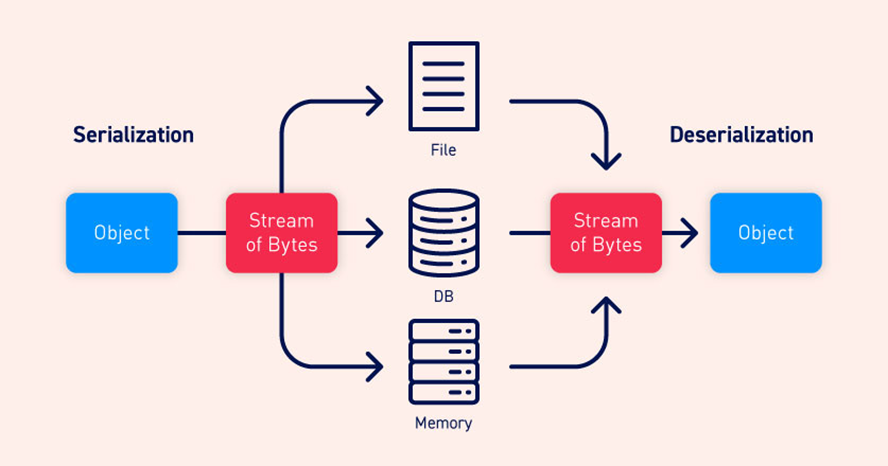
Insecure Deserialization Attack In Python Application Insecure deserialization occurs when an api reconstructs an object from untrusted data without validating its contents. attackers modify the serialized data to include malicious code that executes during the reconstruction process. A deserialization attack, specifically insecure deserialization, occurs when an application converts (or deserializes) a stream of data into a live object without ensuring the data is safe or trustworthy. Insecure deserialization is a serious vulnerability that can lead to remote code execution, injection attacks, and other critical security issues. it occurs when an application deserializes untrusted or maliciously crafted data without proper validation or sanitization. Insecure deserialization represents a significant security risk that arises when an application improperly handles the deserialization of untrusted data. this vulnerability can lead to a wide range of attacks, including remote code execution, privilege escalation, and data manipulation.
Comments are closed.