Insecure Deserialization

Insecure Deserialization Foundations Learn what insecure deserialization is, how it can expose websites to high severity attacks, and how to exploit and prevent it. see examples of php, ruby, and java deserialization and the techniques to manipulate them. Learn what insecure deserialization is, how it can be exploited, and how to mitigate it. see an example scenario, impact, and references for java and other languages.
Github Qeeqbox Insecure Deserialization A Threat Actor May Tamper Another less understood but equally dangerous vulnerability associated with user input is insecure deserialisation. insecure deserialisation exploits occur when an application trusts. Learn how to exploit and prevent insecure deserialization vulnerabilities in java applications. follow a step by step guide to hack a web game and understand the concepts of gadgets and deserialization chains. Insecure deserialization is a serious vulnerability that can lead to remote code execution, injection attacks, and other critical security issues. it occurs when an application deserializes untrusted or maliciously crafted data without proper validation or sanitization. What is insecure deserialization in simple terms? insecure deserialization occurs when an api reconstructs an object from untrusted data without validating its contents.
Prevent Insecure Deserialization Attacks Veracode Docs Insecure deserialization is a serious vulnerability that can lead to remote code execution, injection attacks, and other critical security issues. it occurs when an application deserializes untrusted or maliciously crafted data without proper validation or sanitization. What is insecure deserialization in simple terms? insecure deserialization occurs when an api reconstructs an object from untrusted data without validating its contents. Deserialization was designed to reconstruct complex objects, but when used on untrusted input, it can reconstruct more than just data. insecure deserialization lets attackers provide specially crafted data that executes code, reads files, or cause the application to crash. Insecure deserialization happens when an application blindly deserializes data that came from an untrusted source (like you, the hacker 👀) without verifying what that data actually contains. In this blog, we’ll walk you through everything you need to know about insecure deserialization — from basic concepts to real world exploitation and mitigation strategies. What is insecure deserialization? insecure deserialization is a vulnerability in which untrusted or unknown data is used to inflict a denial of service attack, execute code, bypass authentication or otherwise abuse the logic behind an application.
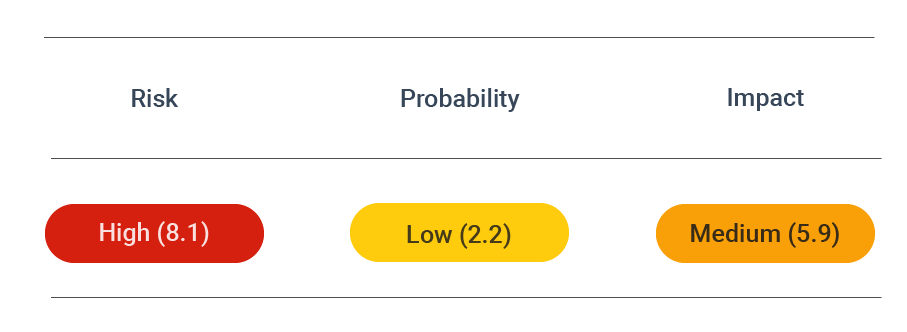
Prevent Insecure Deserialization Attacks Veracode Docs Deserialization was designed to reconstruct complex objects, but when used on untrusted input, it can reconstruct more than just data. insecure deserialization lets attackers provide specially crafted data that executes code, reads files, or cause the application to crash. Insecure deserialization happens when an application blindly deserializes data that came from an untrusted source (like you, the hacker 👀) without verifying what that data actually contains. In this blog, we’ll walk you through everything you need to know about insecure deserialization — from basic concepts to real world exploitation and mitigation strategies. What is insecure deserialization? insecure deserialization is a vulnerability in which untrusted or unknown data is used to inflict a denial of service attack, execute code, bypass authentication or otherwise abuse the logic behind an application.

Insecure Deserialization Attacks Risks And Best Practices In this blog, we’ll walk you through everything you need to know about insecure deserialization — from basic concepts to real world exploitation and mitigation strategies. What is insecure deserialization? insecure deserialization is a vulnerability in which untrusted or unknown data is used to inflict a denial of service attack, execute code, bypass authentication or otherwise abuse the logic behind an application.
Comments are closed.