Insecure Cryptographic Storage Demonstration Video

Insecure Data Storage Download Free Pdf Encryption Cryptography Here is a short insecure cryprographic storage demonstration video, which appears in the appsec labs application security awareness e learning software. The insecure cryptographic storage vulnerability affects almost all websites and online organizations, but it can be especially problematic with sensitive private data.

Insecure Cryptographic Storage Challenge 2 Security Shepherd R Learn about the dangers of insecure cryptographic storage and how to protect your data with effective security measures and best practices. Run a secure aws scan with kirkpatrickprice to receive a report with custom recommendations from our cloud security experts. start your free scan today!. If insecure cryptographic methods or cryptographic configurations are used, the risk of information leakage and compromising (privileged) accounts is high. this significantly raises the chances of a devastating cyberattack and its impact. Insecure cryptographic storage refers to the practice of storing sensitive information, such as passwords or other confidential data, in a way that can be easily recovered by an attacker.

Insecure Data Storage Android If insecure cryptographic methods or cryptographic configurations are used, the risk of information leakage and compromising (privileged) accounts is high. this significantly raises the chances of a devastating cyberattack and its impact. Insecure cryptographic storage refers to the practice of storing sensitive information, such as passwords or other confidential data, in a way that can be easily recovered by an attacker. We’ll explain what a insecure cryptographic storage attack is, its causes and preventions, and some potential hazards. Here's a walkthrough of implemented user stories: gif created with licecap. this lab was definitely more challenging than the week before. i still need to learn how to spot patterns in encryption methods. When developers don't protect confidential data, the business falls prey to insecure cryptographic storage. let's take a look at how to securely store data, and what can happen when you don't. when attackers gain access to a system, they're typically on the hunt for data of value. With the growing need for cybersecurity across the world, developers who have mastered cyber resilience get ahead. secure coding in asp is an instrumental pathway for all selection from writing secure code in asp [video].

Insecure Data Storage Android We’ll explain what a insecure cryptographic storage attack is, its causes and preventions, and some potential hazards. Here's a walkthrough of implemented user stories: gif created with licecap. this lab was definitely more challenging than the week before. i still need to learn how to spot patterns in encryption methods. When developers don't protect confidential data, the business falls prey to insecure cryptographic storage. let's take a look at how to securely store data, and what can happen when you don't. when attackers gain access to a system, they're typically on the hunt for data of value. With the growing need for cybersecurity across the world, developers who have mastered cyber resilience get ahead. secure coding in asp is an instrumental pathway for all selection from writing secure code in asp [video].
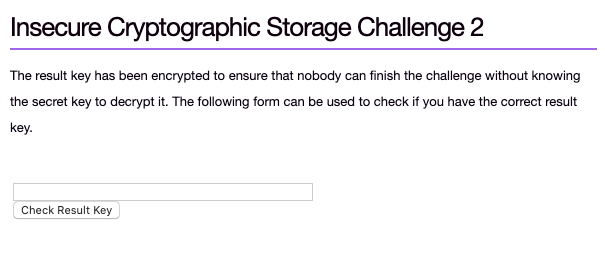
Insecure Cryptographic Storage Challenge 2 The Result Chegg When developers don't protect confidential data, the business falls prey to insecure cryptographic storage. let's take a look at how to securely store data, and what can happen when you don't. when attackers gain access to a system, they're typically on the hunt for data of value. With the growing need for cybersecurity across the world, developers who have mastered cyber resilience get ahead. secure coding in asp is an instrumental pathway for all selection from writing secure code in asp [video].
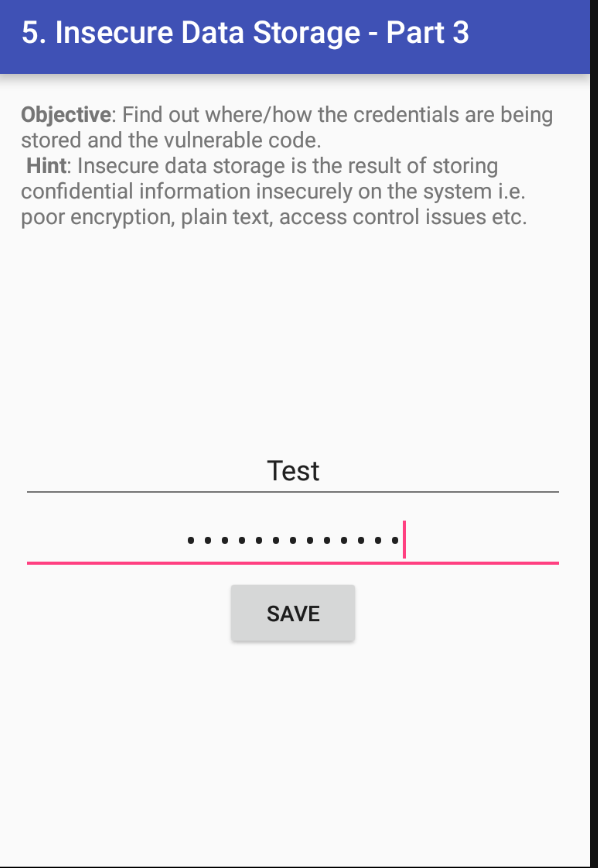
Insecure Data Storage Android
Comments are closed.