Insecure Cryptographic Storage

Insecure Cryptographic Storage Challenge 2 Security Shepherd R Insecure cryptographic storage vulnerability is a type of flaw in the way that data is being stored and secured online. it's an issue that impacts nearly all websites and online organizations, but it can be especially problematic with sensitive private data. Passwords should not be stored using reversible encryption secure password hashing algorithms should be used instead. the password storage cheat sheet contains further guidance on storing passwords.

Insecure Data Storage Android There is an overlapping relationship between insecure storage of sensitive information (cwe 922) and missing encryption of sensitive information (cwe 311). encryption is often used to prevent an attacker from reading the sensitive data. Learn how to identify and fix insecure cryptographic storage vulnerabilities to properly protect sensitive data at rest. One of the most critical aspects of data security is cryptographic storage. in this article, we will explore the dangers of insecure cryptographic storage, its risks and consequences, and provide a comprehensive guide on best practices for secure cryptographic storage. Storing encrypted files is critical for companies that offer sensitive information online. but improperly encrypted files can be an equally risky scenario as it leads to a false sense of security. the process of having improperly encrypted files in storage is known as insecure cryptographic storage (ics).
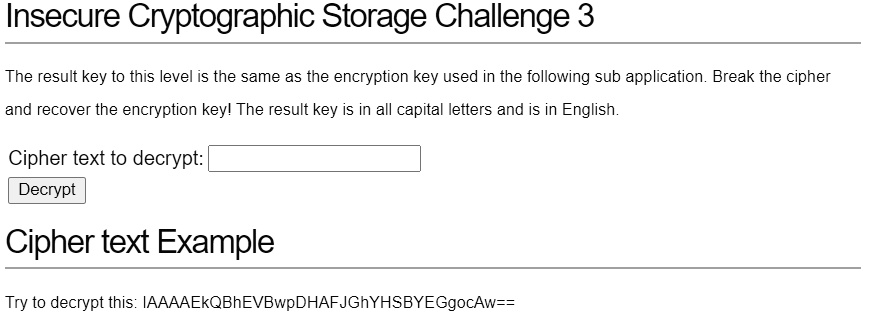
Insecure Cryptographic Storage Challenge 3 The Result Key To One of the most critical aspects of data security is cryptographic storage. in this article, we will explore the dangers of insecure cryptographic storage, its risks and consequences, and provide a comprehensive guide on best practices for secure cryptographic storage. Storing encrypted files is critical for companies that offer sensitive information online. but improperly encrypted files can be an equally risky scenario as it leads to a false sense of security. the process of having improperly encrypted files in storage is known as insecure cryptographic storage (ics). When developers don't protect confidential data, the business falls prey to insecure cryptographic storage. let's take a look at how to securely store data, and what can happen when you don't. when attackers gain access to a system, they're typically on the hunt for data of value. Learn what insecure cryptographic storage is and how it can expose sensitive data to hackers. see how to prevent this vulnerability and watch a video demonstration. Insecure cryptographic storage refers to the practice of storing sensitive information, such as passwords or other confidential data, in a way that can be easily recovered by an attacker. Secure storage of encryption keys: ensure encryption keys are securely stored on the mobile device. avoid storing keys in plain text or easily accessible locations. consider using secure storage mechanisms provided by the operating system or utilizing hardware based secure storage options.

Owasp Security Shepherd Insecure Cryptographic Storage Challenge 1 When developers don't protect confidential data, the business falls prey to insecure cryptographic storage. let's take a look at how to securely store data, and what can happen when you don't. when attackers gain access to a system, they're typically on the hunt for data of value. Learn what insecure cryptographic storage is and how it can expose sensitive data to hackers. see how to prevent this vulnerability and watch a video demonstration. Insecure cryptographic storage refers to the practice of storing sensitive information, such as passwords or other confidential data, in a way that can be easily recovered by an attacker. Secure storage of encryption keys: ensure encryption keys are securely stored on the mobile device. avoid storing keys in plain text or easily accessible locations. consider using secure storage mechanisms provided by the operating system or utilizing hardware based secure storage options.
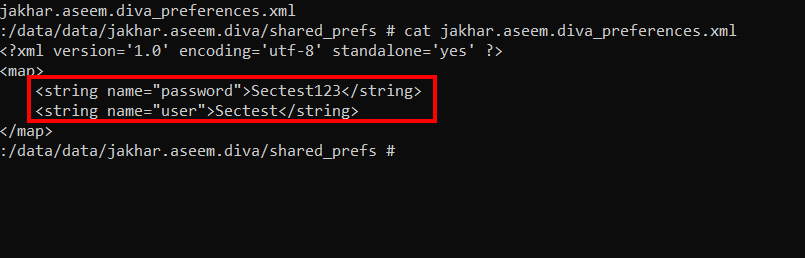
Insecure Data Storage Android Insecure cryptographic storage refers to the practice of storing sensitive information, such as passwords or other confidential data, in a way that can be easily recovered by an attacker. Secure storage of encryption keys: ensure encryption keys are securely stored on the mobile device. avoid storing keys in plain text or easily accessible locations. consider using secure storage mechanisms provided by the operating system or utilizing hardware based secure storage options.
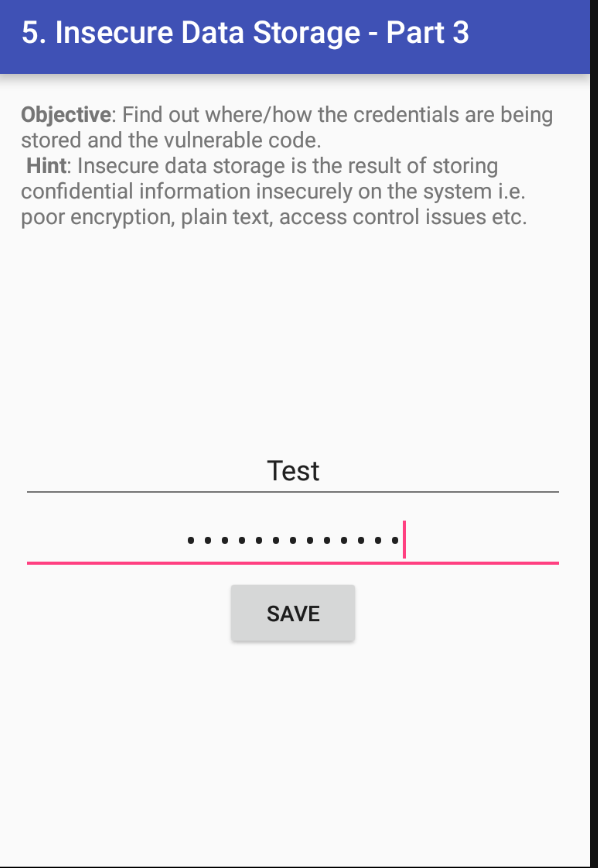
Insecure Data Storage Android
Comments are closed.