Input Validation Ppt

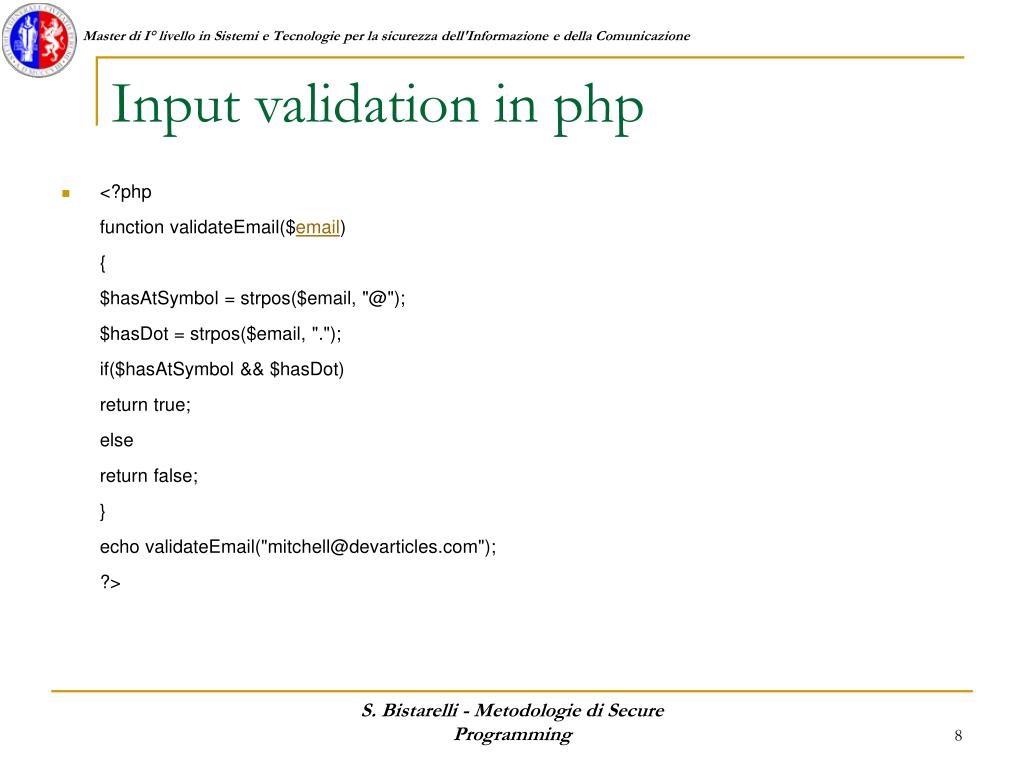
Lecture 4 Input Validation Pdf Input validation is important to prevent incorrect or invalid values from being entered into an application which could lead to user frustration or security issues. Ensure the integrity of your data with our input validation powerpoint presentation. this fully editable and customizable resource provides insights into effective input validation techniques, helping you safeguard your applications and enhance user experience.
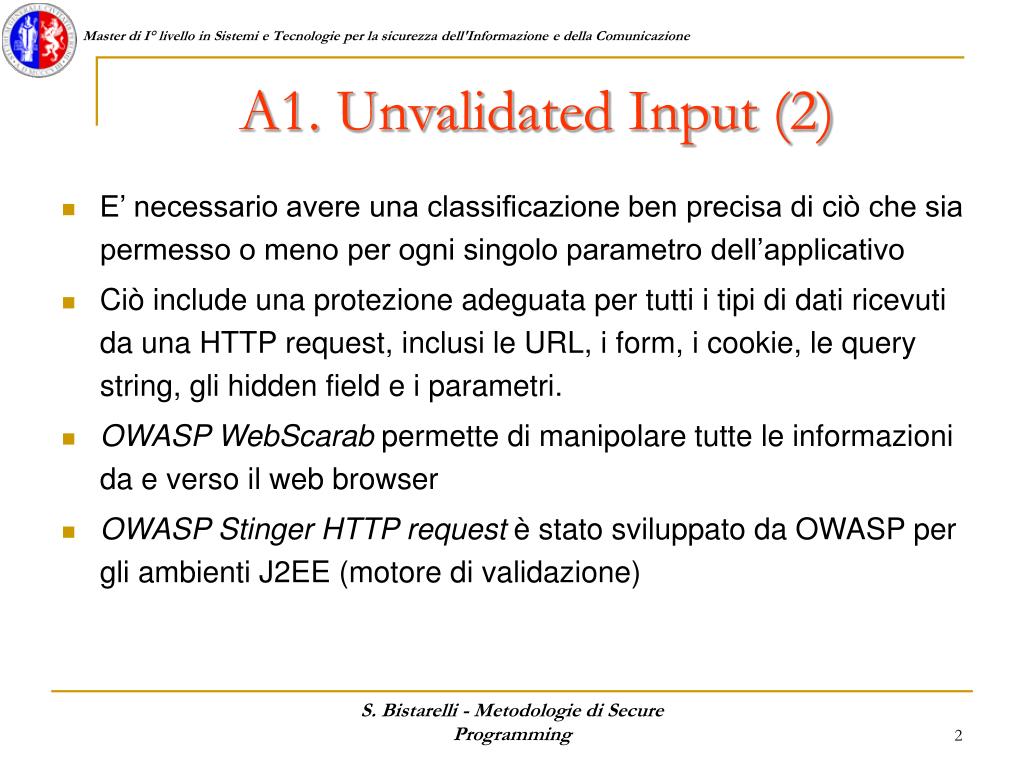
Ppt Input Validation Powerpoint Presentation Free Download Id 4072233 Topics like product development, successfully validated design, inputs according can be discussed with this completely editable template. it is available for immediate download depending on the needs and requirements of the user. Learn the importance of validating input and trust relationships in software engineering. explore validation techniques, dangerous variables, and entry points to ensure secure programming practices. You must do input validation of allchannels where untrusted data comes from (at least) discussion: input sources • for different kinds of programs: identify some potential input channels (e.g., ports) and methods (apis) •do not limit to intendedchannels & methods what might an attacker try to do?. Defensive programming aims to anticipate errors and design programs to avoid them, and input validation is a key part of defensive programming. common applications for validation include addresses, financial values, dates, and more. download as a pptx, pdf or view online for free.
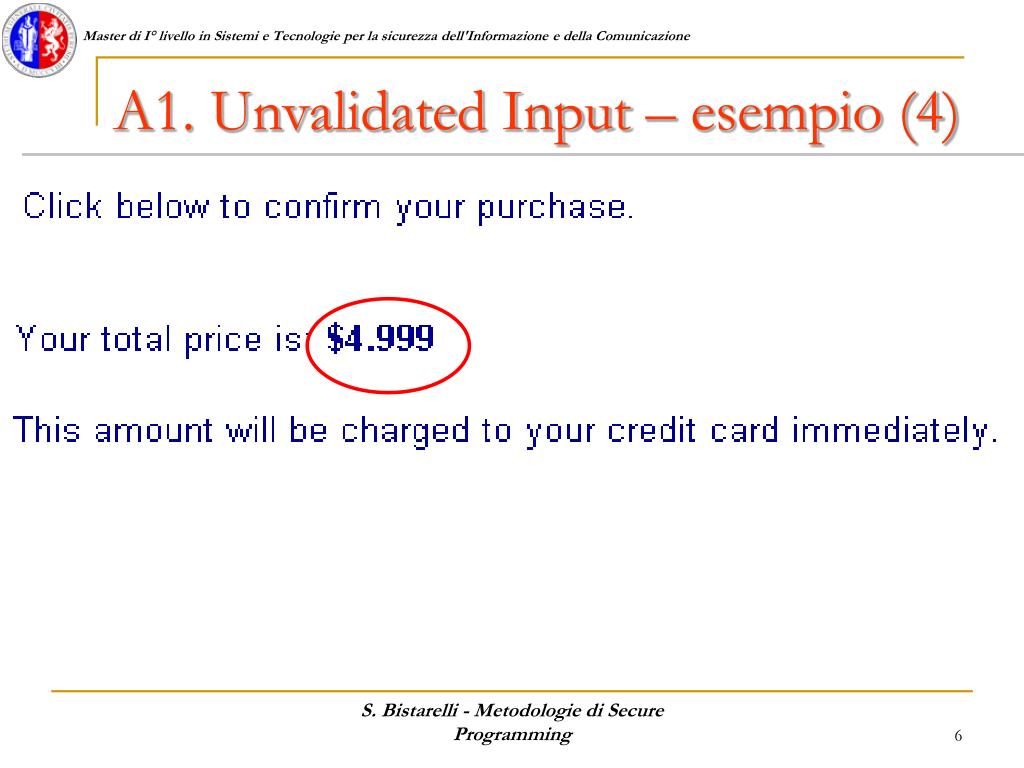
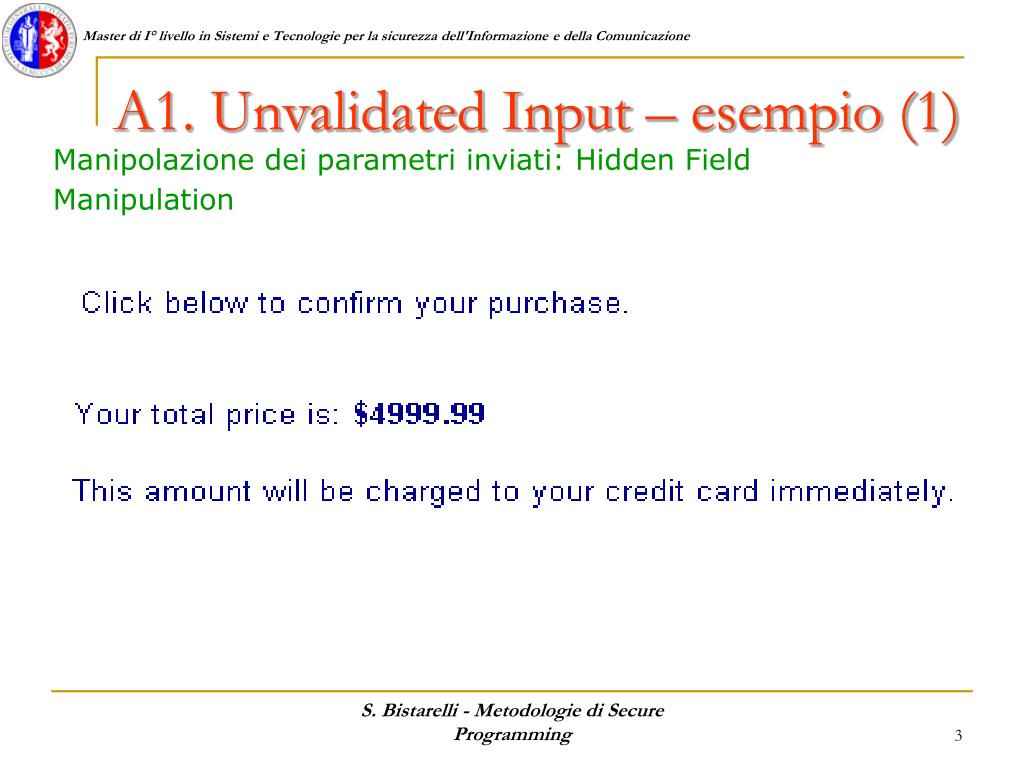
Ppt Input Validation Powerpoint Presentation Free Download Id 4072233 You must do input validation of allchannels where untrusted data comes from (at least) discussion: input sources • for different kinds of programs: identify some potential input channels (e.g., ports) and methods (apis) •do not limit to intendedchannels & methods what might an attacker try to do?. Defensive programming aims to anticipate errors and design programs to avoid them, and input validation is a key part of defensive programming. common applications for validation include addresses, financial values, dates, and more. download as a pptx, pdf or view online for free. Top 10 input validation techniques powerpoint presentation templates in 2026 input validation techniques are essential in software development, ensuring that the data provided by users meets specific criteria before it is processed. these techniques help prevent errors, enhance security, and improve overall application robustness. Input validation cheat sheet introduction this article is focused on providing clear, simple, actionable guidance for providing input validation security functionality in your applications. goals of input validation input validation is performed to ensure only properly formed data is entering the workflow in an information system, preventing malformed data from persisting in the database and. Topics like purpose of validating solution, techniques of validating solution, process inputs description, process output description can be discussed with this completely editable template. The document discusses various techniques for attacking web applications through input validation vulnerabilities, including buffer overflows, sql injection, cross site scripting, and command execution.
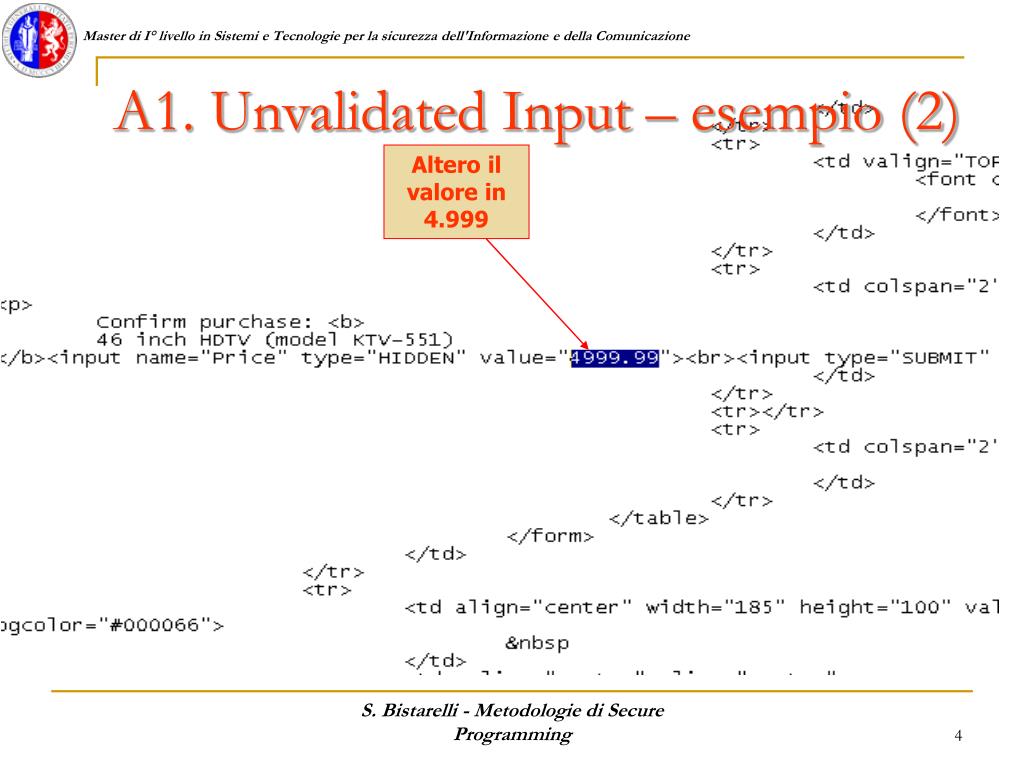
Ppt Input Validation Powerpoint Presentation Free Download Id 4072233 Top 10 input validation techniques powerpoint presentation templates in 2026 input validation techniques are essential in software development, ensuring that the data provided by users meets specific criteria before it is processed. these techniques help prevent errors, enhance security, and improve overall application robustness. Input validation cheat sheet introduction this article is focused on providing clear, simple, actionable guidance for providing input validation security functionality in your applications. goals of input validation input validation is performed to ensure only properly formed data is entering the workflow in an information system, preventing malformed data from persisting in the database and. Topics like purpose of validating solution, techniques of validating solution, process inputs description, process output description can be discussed with this completely editable template. The document discusses various techniques for attacking web applications through input validation vulnerabilities, including buffer overflows, sql injection, cross site scripting, and command execution.
Ppt Input Validation Powerpoint Presentation Free Download Id 4072233 Topics like purpose of validating solution, techniques of validating solution, process inputs description, process output description can be discussed with this completely editable template. The document discusses various techniques for attacking web applications through input validation vulnerabilities, including buffer overflows, sql injection, cross site scripting, and command execution.
Ppt Input Validation Powerpoint Presentation Free Download Id 4072233
Comments are closed.