Information Security Vulnerability Management Program Ppt Sample
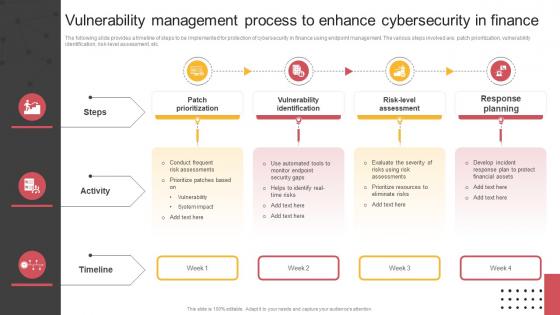
Vulnerability Management Process To Enhance Cybersecurity In Finance Our fully editable and customizable powerpoint presentations provide a comprehensive overview of vulnerability management, empowering organizations to effectively communicate their strategies and processes. Once gaps have been addressed through effective vulnerability management over time, penetration testing can further test security and provide assurance. download as a pptx, pdf or view online for free.
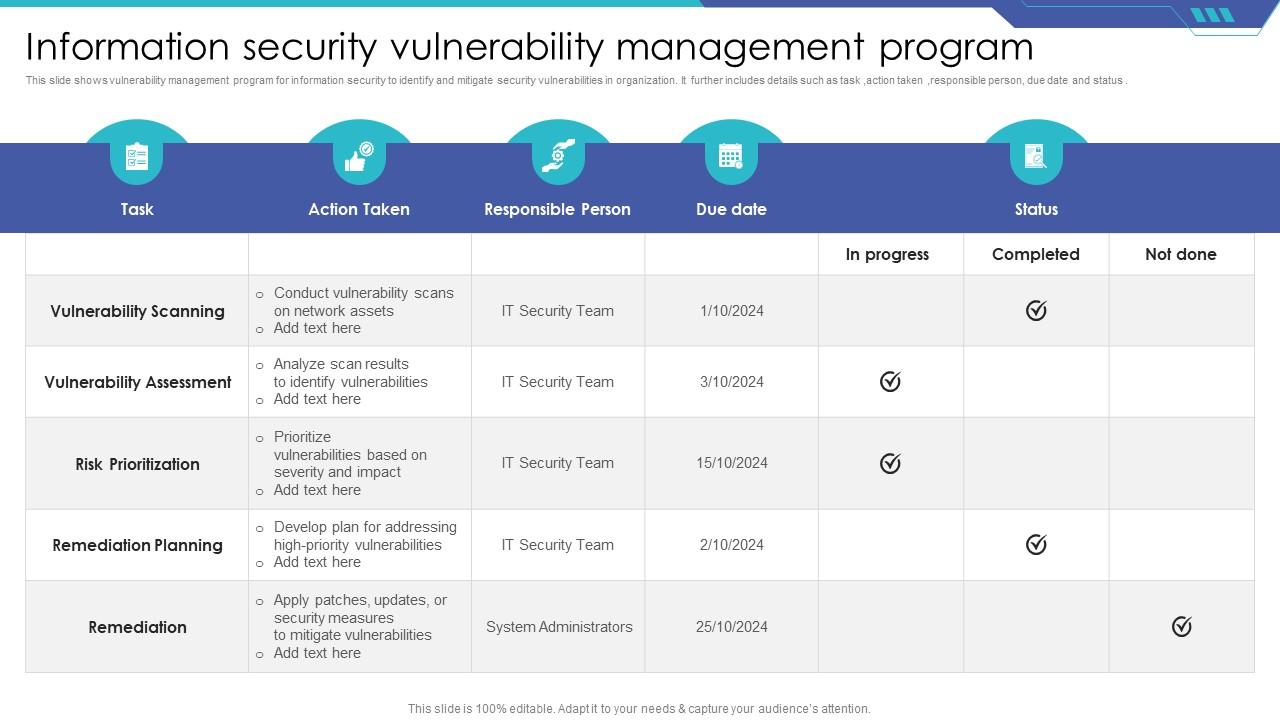
Information Security Vulnerability Management Program Ppt Sample This article by shon harris, ceo of logical security, explores evolving approaches to information security. it outlines the steps of the vulnerability management lifecycle, starting with defining roles and responsibilities, inventory management, developing metrics, assessing and baselining,. Decision making process flow for vulnerability management portrait pdf slide 1 of 2. The document discusses various aspects of vulnerability management in cybersecurity, including the roles of security operations centers (socs), threat intelligence, and incident response processes. Download this entirely editable template on vulnerability management will let you draft visually stunning powerpoint or google slides presentations. available in different color themes.
Vulnerability Management Program Practices Ppt Powerpoint Presentation The document discusses various aspects of vulnerability management in cybersecurity, including the roles of security operations centers (socs), threat intelligence, and incident response processes. Download this entirely editable template on vulnerability management will let you draft visually stunning powerpoint or google slides presentations. available in different color themes. Our ms powerpoint and google slides presentation template is perfect for showcasing the benefits and stages of vulnerability management. so, download it without delay!. Download from our collection of free vulnerability templates to help you create stunning ppt presentations. This article serves as a hub for various threat and vulnerability management templates, each designed to streamline and enhance the efficiency of your threat and vulnerability management process. Over 75% of all data breaches do not use a known vulnerability with an assigned cve. cyentia research continuous monitoring & scanning. insert sales pitch here. the use of ai & ml. accuracy.
Comments are closed.