Information Security Vulnerability Assessment Administration

Solutions Internal Vulnerability Assessment Learn what vulnerability assessment is, the key types and five step process, and how to build an effective va program. includes 2026 statistics and compliance mapping. Learn how to conduct a vulnerability assessment process and discover if it can help keep your organization safe from known and zero day vulnerabilities.

The Complete Security Vulnerability Assessment Checklist Discover information security vulnerability management, its importance, and how to identify, assess, and fix security risks to protect sensitive data. Vulnerability assessments should be a must for large and small businesses to ensure that their it infrastructure is secure. these thorough assessments not only safeguard businesses from hostile cyber attacks but also help customers and shareholders trust them. Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Understand risks across your network with a vulnerability assessment. our vulnerability assessment solution focuses on making your data actionable.
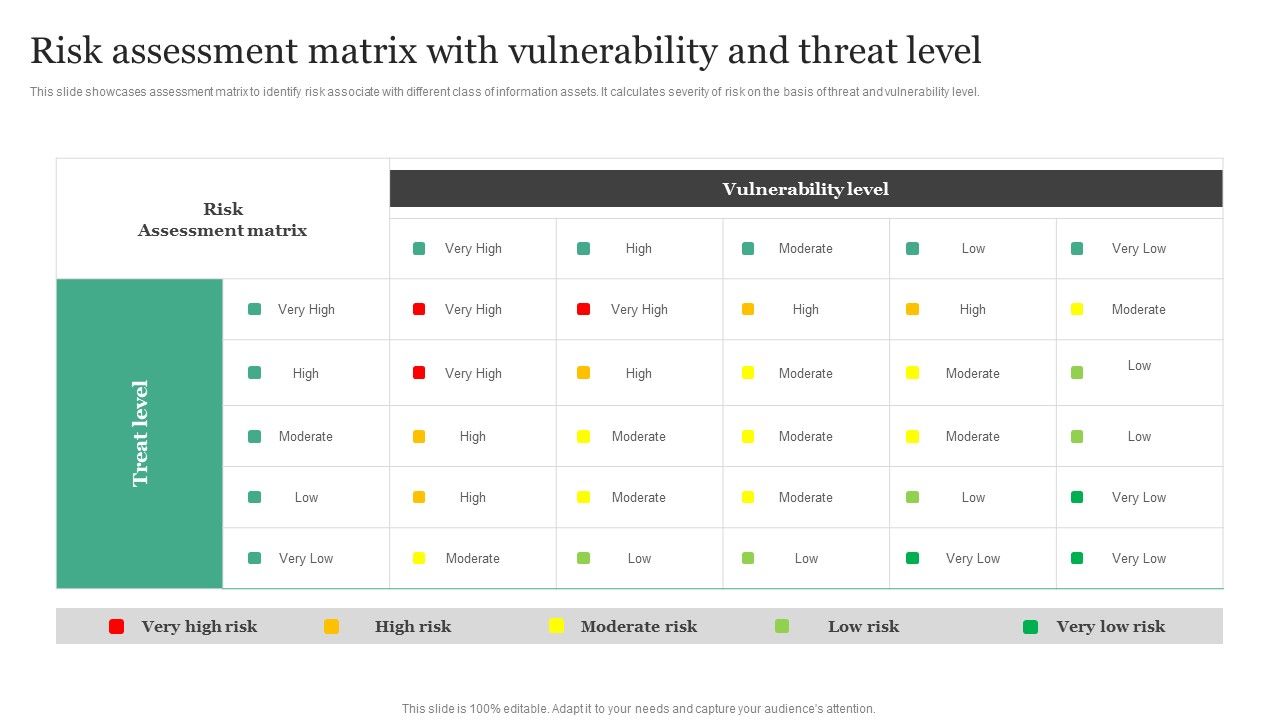
Risk Assessment Matrix With Vulnerability And Threat Level Information Secu Vulnerability assessment is a process that identifies security weaknesses of any it system, network, application, or cloud environment. it is a proactive approach to detect and fix security gaps before any cyber criminals exploit them. Understand risks across your network with a vulnerability assessment. our vulnerability assessment solution focuses on making your data actionable. In this comprehensive guide, we’ll explore vulnerability assessment methodology, the different types of vulnerability assessments, the best tools available, and best practices for conducting these assessments. It performs a vulnerability analysis process that aims to discover whether the organization is at risk of known vulnerabilities, assigns a level of severity to those vulnerabilities, and recommends whether a threat should be mitigated or remediated. The guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification scanning phase, the reporting phase, and remediation phase. In this guide, we’ll walk through what vulnerability management really means in practice, how it differs from a basic vulnerability assessment, and the key steps involved in building a program that actually works.
Comments are closed.