Infographic Mobile Phishing Attacks
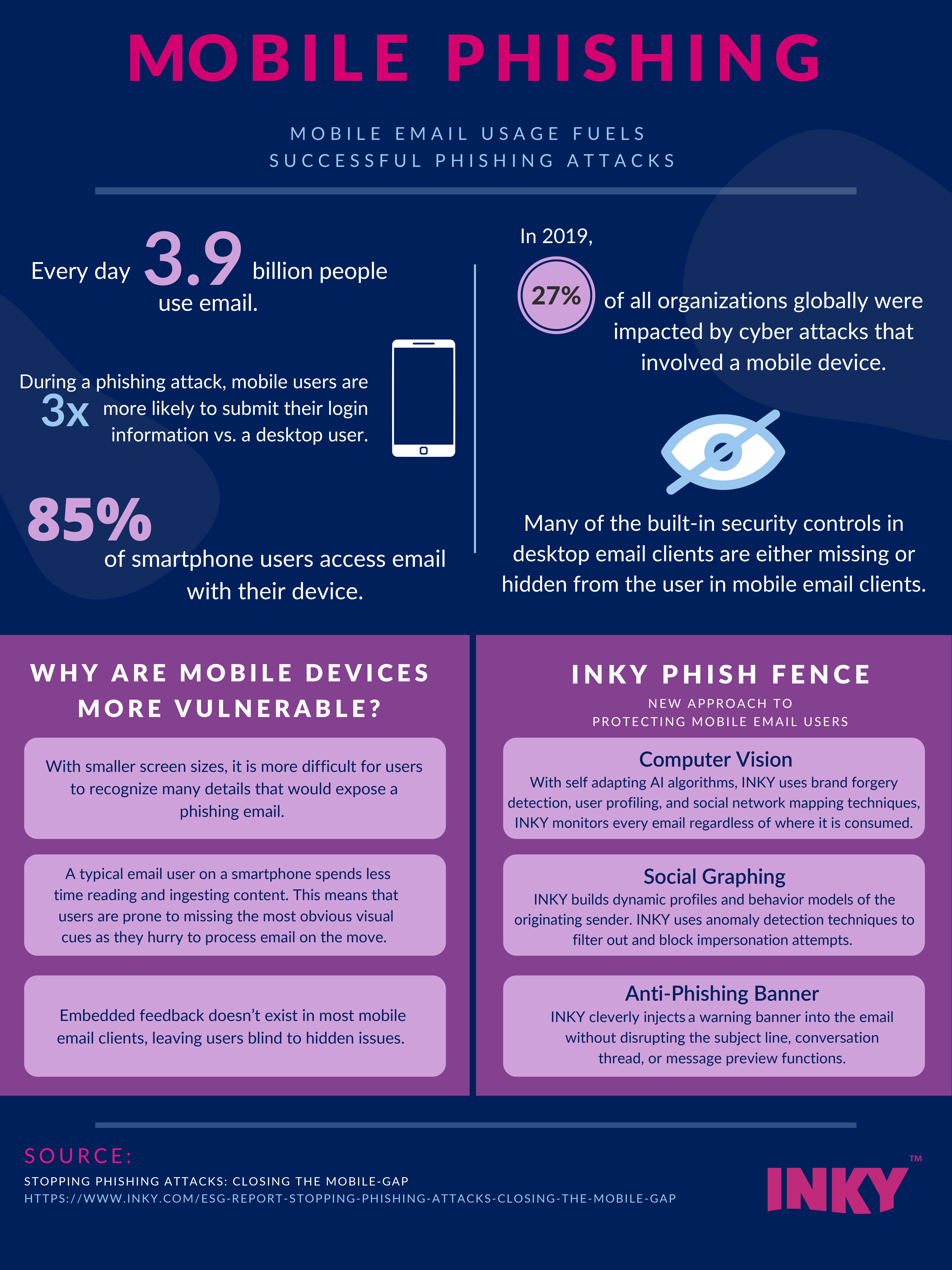
Infographic Mobile Phishing Attacks Mobile phishing is rising at an alarming rate. we've gather some stats on why we're seeing an increase in attacks, how they're successful, and how to avoid them. Mobile phishing is one of the most common ways for attackers to steal employee login credentials. remote work and the popularity of bring your own devices (byod) have dramatically increased the frequency of such attacks.

Infographic Mobile Phishing Attacks Phishing is a form of social engineering in which a cyber threat actor poses as a trustworthy colleague, acquaintance, or organization to lure a victim into providing sensitive information or network access. the lures can come in the form of an email, text message, or even a phone call. This infographic covers the most common types of phishing attacks. whether its through email, phone call, text message, or usb baiting, learn about how these attacks can occur, common statistics, and prevention tips. An infographic style diagram of a cyber attack process: phishing, malware delivery, network infiltration, data exfiltration, represented with clean vector icons and arrows. To better understand how this security threat works, we’ve discussed in this infographic what mobile phishing is, and the different techniques being used to defend against this attack.

Mobile Phishing Infographic An infographic style diagram of a cyber attack process: phishing, malware delivery, network infiltration, data exfiltration, represented with clean vector icons and arrows. To better understand how this security threat works, we’ve discussed in this infographic what mobile phishing is, and the different techniques being used to defend against this attack. Our analysis breaks down the prevalent threats observed across both android and ios platforms, highlighting the key attack vectors targeting devices, networks, applications, and users through sophisticated mishing (mobile targeted phishing) and other campaigns. Don't miss the latest cybersecurity facts, figures & statistics in beautifully designed infographics for your research work. This report provides the industry's chief reference point on real phishing attacks that bypass email filters, helping paint a clearer picture of evolving trends in the ai boosted phishing landscape and its effect on human cyber behavior. Mobile cyberattacks are increasing and evolving. it is essential to navigate these threats by learning more about the current trends.
.png#keepProtocol)
Phishing Attacks The Anatomy Of A Threat Our analysis breaks down the prevalent threats observed across both android and ios platforms, highlighting the key attack vectors targeting devices, networks, applications, and users through sophisticated mishing (mobile targeted phishing) and other campaigns. Don't miss the latest cybersecurity facts, figures & statistics in beautifully designed infographics for your research work. This report provides the industry's chief reference point on real phishing attacks that bypass email filters, helping paint a clearer picture of evolving trends in the ai boosted phishing landscape and its effect on human cyber behavior. Mobile cyberattacks are increasing and evolving. it is essential to navigate these threats by learning more about the current trends.
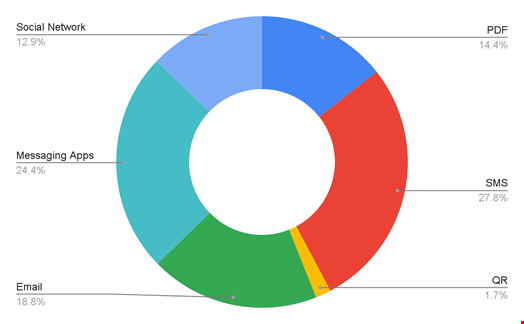
Mobile Phishing Attacks Surge With 16 Of Incidents In Us This report provides the industry's chief reference point on real phishing attacks that bypass email filters, helping paint a clearer picture of evolving trends in the ai boosted phishing landscape and its effect on human cyber behavior. Mobile cyberattacks are increasing and evolving. it is essential to navigate these threats by learning more about the current trends.
Comments are closed.