Incident Response And Cyber Forensics Pdf Windows Registry

Windows Registry Forensics Pdf Microsoft Windows Windows Registry Incident response and cyber forensics free download as pdf file (.pdf), text file (.txt) or read online for free. cybersecurity. This set of guides not only boosts analytical capabilities but also contextualizes the evidence within the security frameworks developed by microsoft over years of incident response .

Module 07 Windows Forensics Download Free Pdf Windows Registry Sans has a massive list of posters available for quick reference to aid you in your security learning. sans posters 46. windows forensic analysis.pdf at main · deepanshusood sans posters. A comprehensive comparison of different cyber forensic tools covering diverse digital forensic domains like windows, image, mobile, and network forensics is provided. Microsoft windows is a widely deployed operating system, making forensic analysis, notably registry analysis, a common practice and central task in cyber incident response. Cientific method. subsequent chapters will then go through different portions of windows including the windows registry, shadow copy, a d related topics. you will also learn to use microsoft powershell to accomplis.

Cloud Forensics Pdf Windows Registry Computer File Microsoft windows is a widely deployed operating system, making forensic analysis, notably registry analysis, a common practice and central task in cyber incident response. Cientific method. subsequent chapters will then go through different portions of windows including the windows registry, shadow copy, a d related topics. you will also learn to use microsoft powershell to accomplis. This paper introduces winregrl, a registry analysis framework that combines reinforcement learning with rule based artificial intelligence. it models forensic analysis as a markov decision process mimicking the sequential decision making operated by experts during incident response. Continue your learning path with industry recognized training and certifications for500: windows forensic analysis: this training course provides in depth windows forensics training, equipping you to recover, analyze, and validate digital evidence, track user and network activity, and present findings for incident response and investigations. 1. introduction. definitions. intended audience. book layout. defining the issue. the pervasiveness and complexity of windows systems. the pervasiveness of high speed connections. the pervasiveness of easy to use tools. purpose. real incidents. where to go for more information. conclusion. This book can be read as a complete introductory course in basic computer forensics and incident response. however, it is also meant to serve as both a guide and a tool; and many readers will already be somewhat familiar with the various subjects covered.

Windows Registry Forensics Artifacts Pptx This paper introduces winregrl, a registry analysis framework that combines reinforcement learning with rule based artificial intelligence. it models forensic analysis as a markov decision process mimicking the sequential decision making operated by experts during incident response. Continue your learning path with industry recognized training and certifications for500: windows forensic analysis: this training course provides in depth windows forensics training, equipping you to recover, analyze, and validate digital evidence, track user and network activity, and present findings for incident response and investigations. 1. introduction. definitions. intended audience. book layout. defining the issue. the pervasiveness and complexity of windows systems. the pervasiveness of high speed connections. the pervasiveness of easy to use tools. purpose. real incidents. where to go for more information. conclusion. This book can be read as a complete introductory course in basic computer forensics and incident response. however, it is also meant to serve as both a guide and a tool; and many readers will already be somewhat familiar with the various subjects covered.
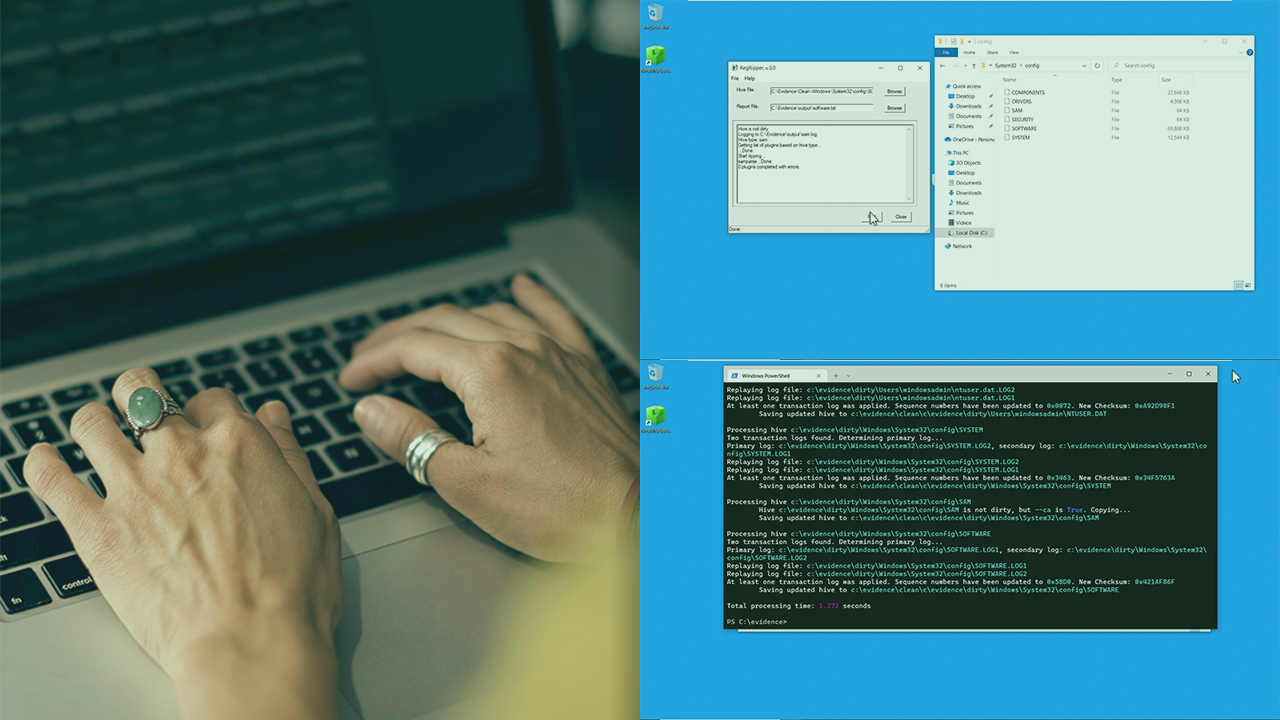
Specialized Dfir Windows Registry Forensics 1. introduction. definitions. intended audience. book layout. defining the issue. the pervasiveness and complexity of windows systems. the pervasiveness of high speed connections. the pervasiveness of easy to use tools. purpose. real incidents. where to go for more information. conclusion. This book can be read as a complete introductory course in basic computer forensics and incident response. however, it is also meant to serve as both a guide and a tool; and many readers will already be somewhat familiar with the various subjects covered.
Comments are closed.