Incident Response 5 Step Process A Guide

5 Steps Of The Incident Response Cycle Master the incident response cycle with our comprehensive guide. learn the 5 phases to effectively handle cybersecurity threats and protect your organization. This article breaks down the incident response phases and steps. you'll see how each stage connects to the next and why following an established lifecycle makes such a difference.

Incident Response Plan Step By Step Guide Toolkitcafe Blog Master the 5 phases of the incident management process with this complete guide. learn how to improve it incident response and minimize downtime. Discover the incident response lifecycle stages and proven practices to help your team detect, contain, recover from incidents, and improve readiness. An incident response plan lists actionable steps to prepare & recover from a cyber attack. learn the 5 steps to help reduce disruptions & ensure compliance. Learn how to build a 5 step incident response plan that minimizes damage, accelerates recovery, and strengthens your cybersecurity readiness.

Incident Response Plan Step By Step Guide Toolkitcafe Blog An incident response plan lists actionable steps to prepare & recover from a cyber attack. learn the 5 steps to help reduce disruptions & ensure compliance. Learn how to build a 5 step incident response plan that minimizes damage, accelerates recovery, and strengthens your cybersecurity readiness. What are the 5 key steps in a cybersecurity incident response plan and how do they help mitigate and recover from attacks? an effective cybersecurity incident response plan includes five key steps: preparation, identification, containment, eradication & recovery, and lessons learned. This step by step guide will walk you through the essential elements of an effective response plan, empowering your organization to handle incidents swiftly and effectively. This guide covers the five step incident response process, key differences between incidents and service requests, best practices for building an effective incident management strategy, and essential metrics to track your team's success. By following these steps, organizations can better protect critical assets, respond to incidents in a coordinated manner, and minimize the impact of future incidents. let's dive into the details of each step in the nist framework for incident response.
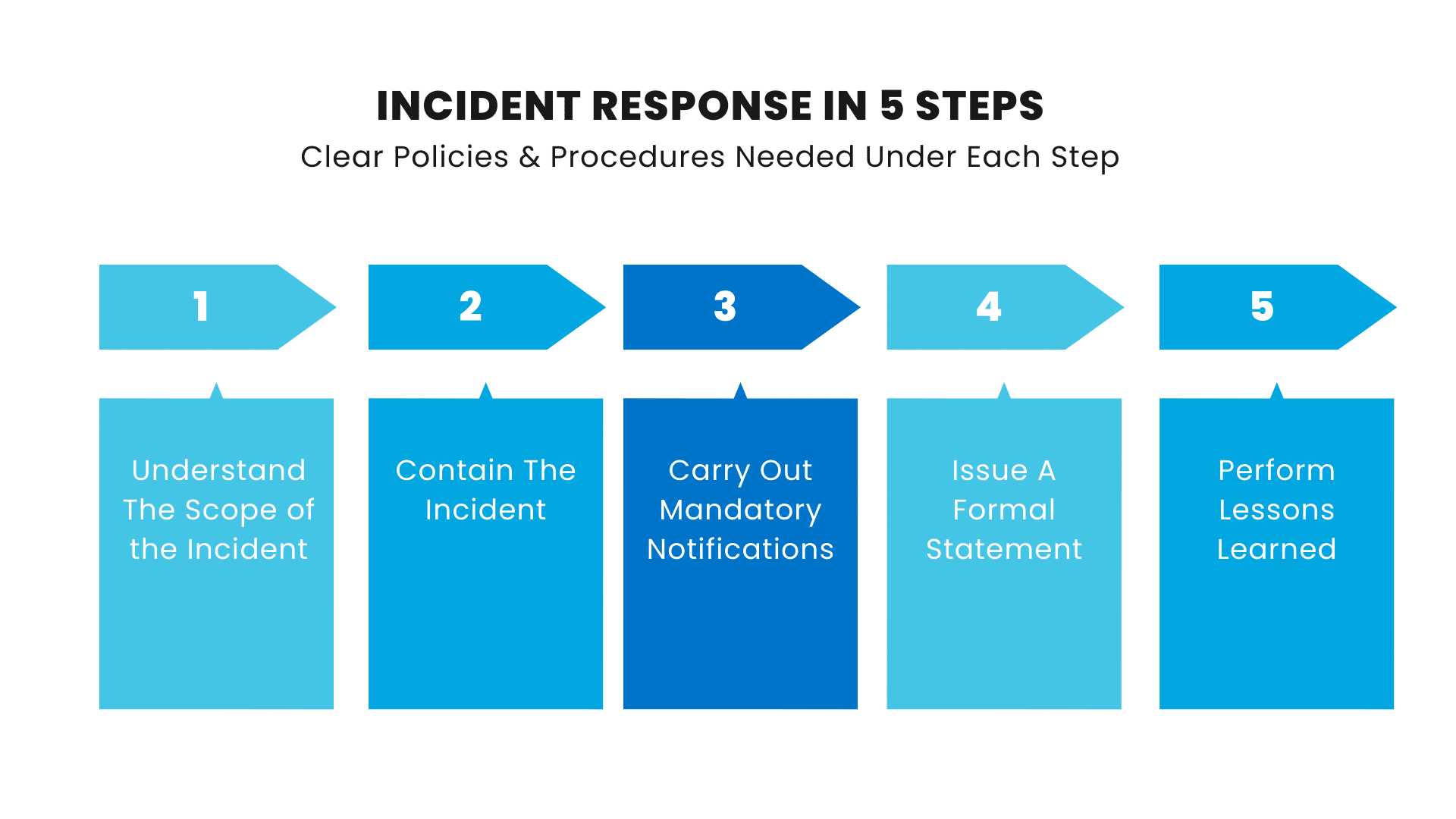
Incident Response Policy A Step By Step Guide What are the 5 key steps in a cybersecurity incident response plan and how do they help mitigate and recover from attacks? an effective cybersecurity incident response plan includes five key steps: preparation, identification, containment, eradication & recovery, and lessons learned. This step by step guide will walk you through the essential elements of an effective response plan, empowering your organization to handle incidents swiftly and effectively. This guide covers the five step incident response process, key differences between incidents and service requests, best practices for building an effective incident management strategy, and essential metrics to track your team's success. By following these steps, organizations can better protect critical assets, respond to incidents in a coordinated manner, and minimize the impact of future incidents. let's dive into the details of each step in the nist framework for incident response.

Incident Response Process Sy0 701 Comptia Security This guide covers the five step incident response process, key differences between incidents and service requests, best practices for building an effective incident management strategy, and essential metrics to track your team's success. By following these steps, organizations can better protect critical assets, respond to incidents in a coordinated manner, and minimize the impact of future incidents. let's dive into the details of each step in the nist framework for incident response.

Incident Response Csrc
Comments are closed.