Implementing Zero Trust Workload Security On Amazon Eks With Calico

Implementing Zero Trust Workload Security On Amazon Eks With Calico In this post, we‘ll dive into how you can apply zero trust workload access controls along with microsegmentation for your workloads that run on amazon eks, and provide specific examples. Learn how you can combine calico cloud and amazon eks to generate compliance reports and meet regulatory compliance requirements.
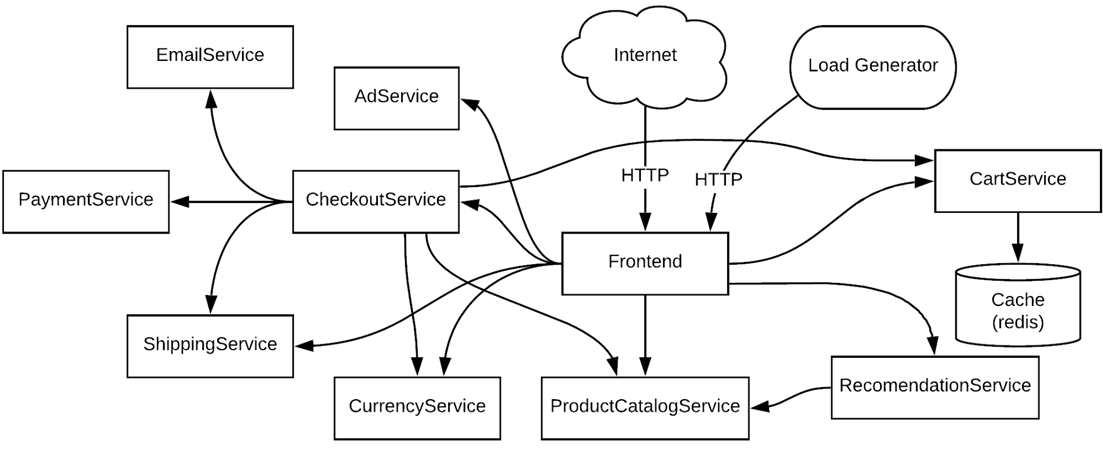
Implementing Zero Trust Workload Security On Amazon Eks With Calico In this eks focused workshop, you will work with aws and calico cloud to learn how implement zero trust security for workloads to reduce the attack surface of applications running on eks clusters. Learn how you can apply zero trust workload access controls along with microsegmentation for workloads on eks, and explore what implementing zero trust workload access controls and identity aware microsegmentation means for you. In this eks focused workshop, you will work with aws and calico cloud to learn how implement zero trust security for workloads to reduce the attack surface of applications running on eks clusters. In this eks focused workshop, you will work with aws and calico cloud to learn how to design and deploy best practices to secure your kubernetes environment, detecting and blocking network based attacks in your clusters.
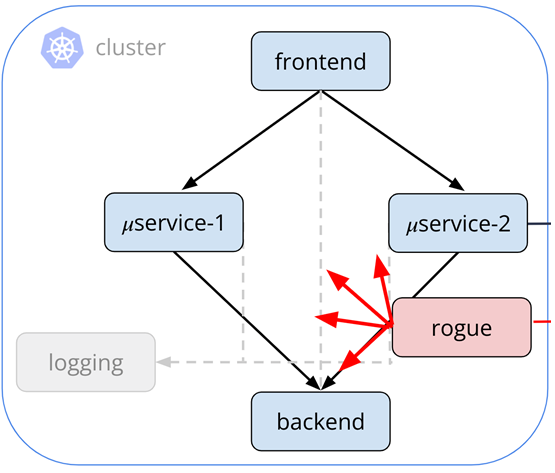
Implementing Zero Trust Workload Security On Amazon Eks With Calico In this eks focused workshop, you will work with aws and calico cloud to learn how implement zero trust security for workloads to reduce the attack surface of applications running on eks clusters. In this eks focused workshop, you will work with aws and calico cloud to learn how to design and deploy best practices to secure your kubernetes environment, detecting and blocking network based attacks in your clusters. This section explains how to establish a zero trust network using calico and istio. it is written from the perspective of platform and security engineers, but should also be useful for individual developers looking to understand the process. In this post, we’ll walk through a proof of concept (poc) for enabling aws’s managed calico addon to enforce networkpolicy in your eks cluster. why calico in eks? amazon eks uses the. In this eks focused workshop, you will work with aws and calico cloud to learn how implement zero trust security for workloads to reduce the attack surface of applications running on eks clusters. In this eks security workshop, you will work with calico and amazon aws experts to learn how to implement zero trust security for workloads to reduce the attack surface of applications running on eks.
Comments are closed.