Implementing Zero Trust

Implementing A Zero Trust Architecture This nist cybersecurity practice guide explains how organizations can implement zta consistent with the concepts and principles outlined in nist special publication (sp) 800 207, zero trust architecture. Learn how to implement zero trust security and the steps you need to take. understand why implementation involves a policy of never trusting and always verifying the authenticity and privileges of devices and users.

Premium Photo Implementing Zero Trust Network Architecture As attackers become more sophisticated, companies need more powerful security. learn how to implement zero trust to keep operations secure. Our guide on how to implement zero trust security breaks down core principles, key components, and best practices for building a modern security framework. Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security.
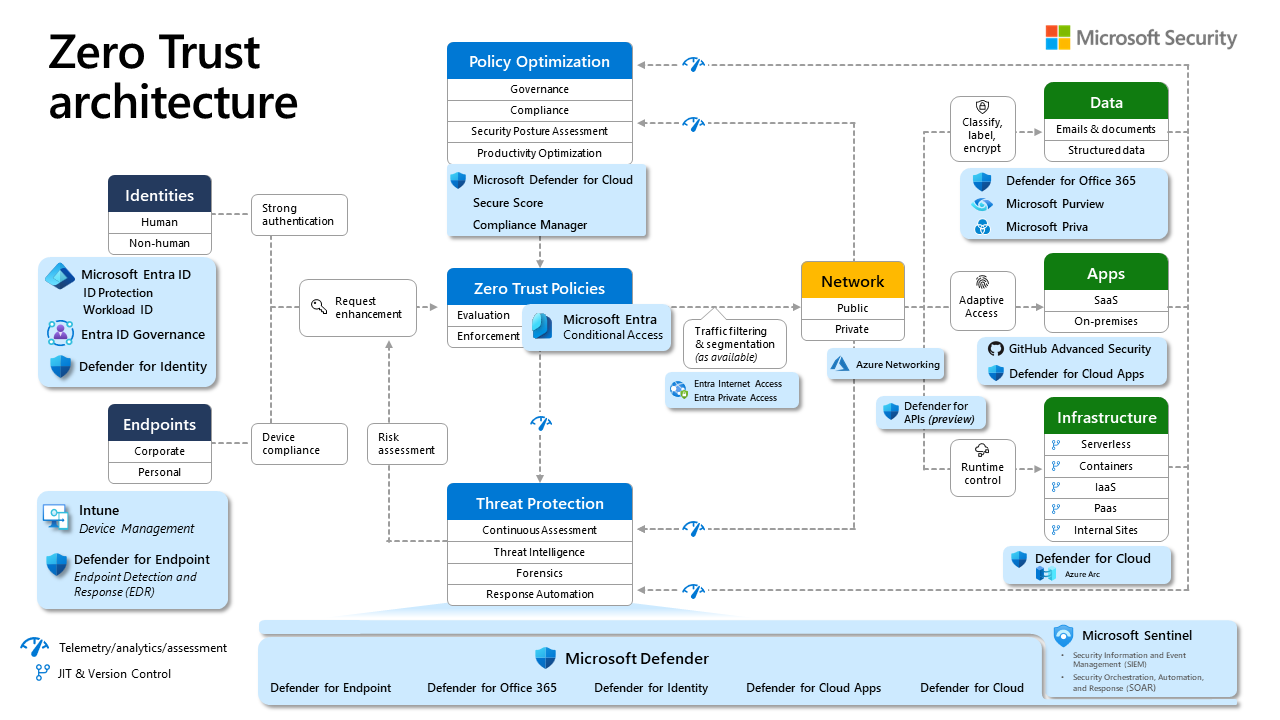
Understanding And Implementing Zero Trust On Azure Know It Like Pro Find deployment guides, assessment tools, and adoption frameworks to implement zero trust principles that protect and enable secure operations across identity, endpoints, applications, data, infrastructure, and networks in your organization. Simplify zero trust implementation with this detailed guide. learn the policies, compliance, and monitoring strategies to implement zero trust security. Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. the goal is to prevent unauthorized access to data and services and make access control. Implementing a zero trust architecture revolves around several fundamental principles: verify explicitly: all access requests are explicitly authenticated and authorized based on all available data points, including user identity, location, device health, service or workload, data sensitivity, and behavioral anomalies. You can implement zero trust for software supply chain security by validating dependencies, securing pipelines, and continuously verifying access.

6 Steps To Implementing A Zero Trust Model The Decision Making Learn how to implement zero trust security with clear pillars, a practical roadmap, and tactics that solve challenges and cut risk across cloud environments. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. the goal is to prevent unauthorized access to data and services and make access control. Implementing a zero trust architecture revolves around several fundamental principles: verify explicitly: all access requests are explicitly authenticated and authorized based on all available data points, including user identity, location, device health, service or workload, data sensitivity, and behavioral anomalies. You can implement zero trust for software supply chain security by validating dependencies, securing pipelines, and continuously verifying access.
Comments are closed.