Implementing Your Own Encryption Library In A Nutshell Scrolller

Implementing Your Own Encryption Library In A Nutshell Scrolller View and enjoy programminghumor with the endless random gallery on scrolller . go on to discover millions of awesome videos and pictures in thousands of other categories. Actually, implementing your own encryption library in a nutshell makes some sense. that way you know the key is squirreled away.

Wiley Implementing Ssl Tls Using Cryptography And Pki 0470920416 Pdf I want to demonstrate that a good light weight crypto library can be written in c and can be made more maintainable. tinytls was once based on tinyssl, but i have re written a lot of new code and get rid of legacy stuffs that are no londer relevant today. This article will provide a deep dive into aes encryption, explaining its working principles, implementation in python, and real world use cases. additionally, we will explore the fernet module from the cryptography library to perform aes encryption effortlessly. And it is very important (and very simple) to invent your own encryption library. you’ll find thousands of articles discouraging you from writing your own encryption algorithm but not. The tables below compare cryptography libraries that deal with cryptography algorithms and have application programming interface (api) function calls to each of the supported features.

Make Your Own Encryption Program Admin Tinkernut Free Download And it is very important (and very simple) to invent your own encryption library. you’ll find thousands of articles discouraging you from writing your own encryption algorithm but not. The tables below compare cryptography libraries that deal with cryptography algorithms and have application programming interface (api) function calls to each of the supported features. The modules described in this chapter implement various algorithms of a cryptographic nature. they are available at the discretion of the installation. here’s an overview: how many bytes should tokens use? the modules described in this chapter implement various algorithms of a cryptographic nature. Discover resources for this multi language, cross platform, open source cryptographic library. Python encryption libraries provide developers with powerful tools to protect sensitive data. by understanding the fundamental concepts of encryption, choosing the right library and algorithm, and following best practices, developers can ensure the security of their applications. This article covers the general idea and the basic steps you'll need to take in order to create a functional and realistic encryption program. when you first determine your encryption algorithm, you should test it with a short message.
Github Redbiscuits Cyber Security Encryption Library C Package That The modules described in this chapter implement various algorithms of a cryptographic nature. they are available at the discretion of the installation. here’s an overview: how many bytes should tokens use? the modules described in this chapter implement various algorithms of a cryptographic nature. Discover resources for this multi language, cross platform, open source cryptographic library. Python encryption libraries provide developers with powerful tools to protect sensitive data. by understanding the fundamental concepts of encryption, choosing the right library and algorithm, and following best practices, developers can ensure the security of their applications. This article covers the general idea and the basic steps you'll need to take in order to create a functional and realistic encryption program. when you first determine your encryption algorithm, you should test it with a short message.
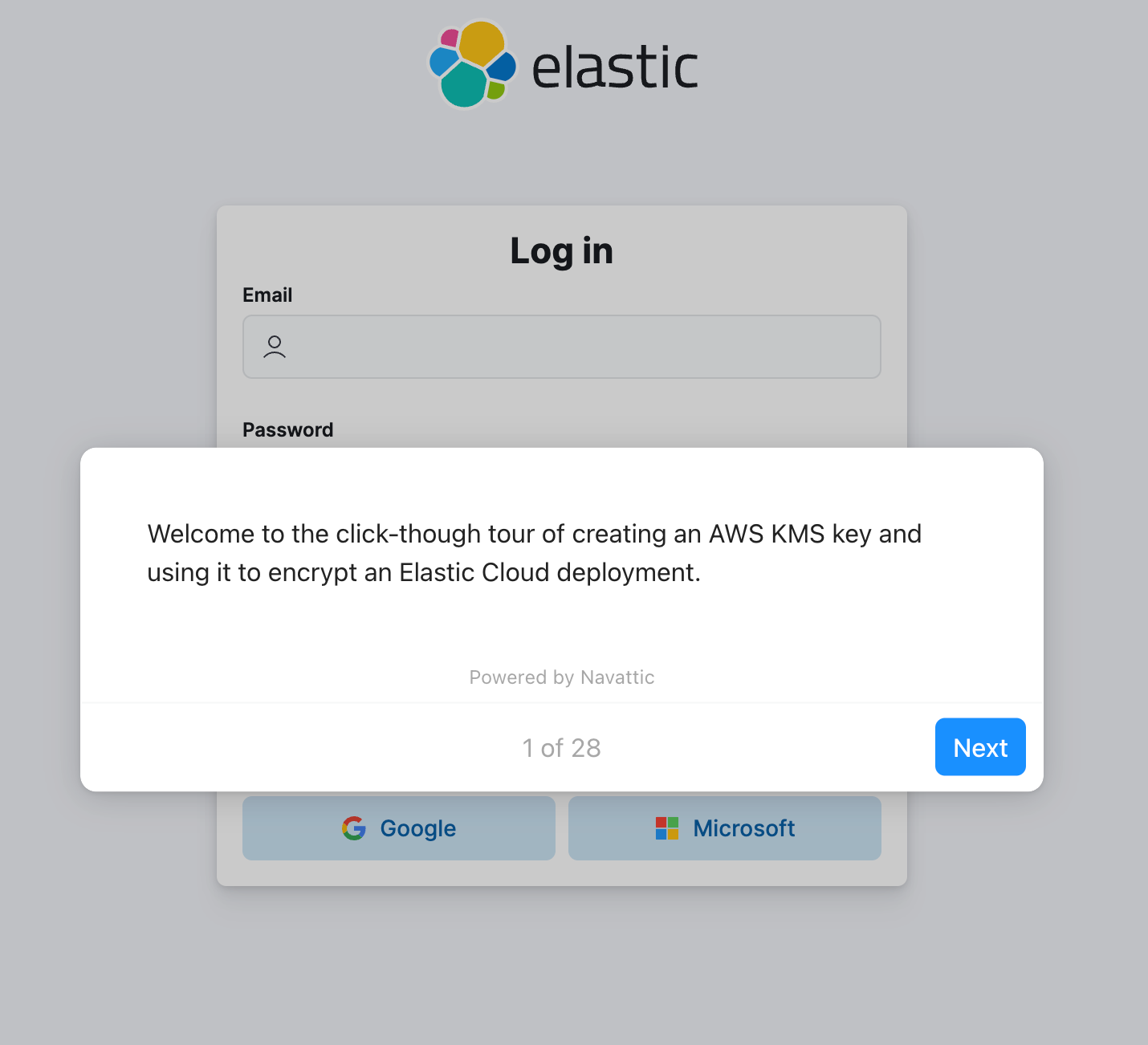
Bring Your Own Encryption Key With Aws Kms Elastic Python encryption libraries provide developers with powerful tools to protect sensitive data. by understanding the fundamental concepts of encryption, choosing the right library and algorithm, and following best practices, developers can ensure the security of their applications. This article covers the general idea and the basic steps you'll need to take in order to create a functional and realistic encryption program. when you first determine your encryption algorithm, you should test it with a short message.
Comments are closed.