Implementing Oauth 2 0 For Secure Api Access In Azure Logic Apps
Secure Access To Your Azure App Services Function Apps Logic Apps Using Azure logic apps, a cloud service that helps automate workflows, can leverage oauth 2.0 to ensure secure api interactions. this article will guide you through the process of implementing oauth 2.0 in azure logic apps, making your applications more secure and efficient. In this article, you’ll learn how to secure logic apps using oauth (microsoft entra id azure ad) so only authorized users or apps can call your flows — no more vulnerable sas tokens.
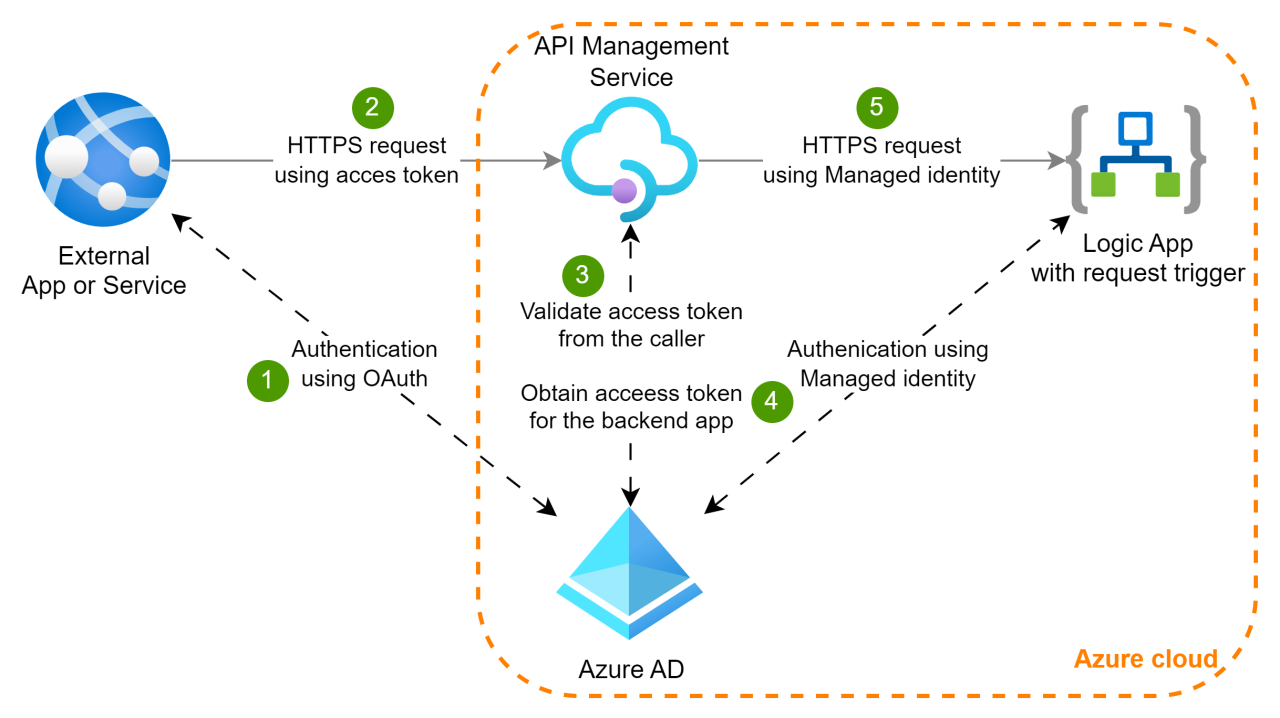
Implementing Oauth 2 0 For Secure Api Access In Azure Logic Apps Sometimes we may need our apps to authenticate autonomously without user input. for this we have oauth 2.0 bearer token. we use oauth 2.0 bearer token to authenticate requests on behalf of our apps. Azure logic apps standard makes it easy to call oauth protected apis using managed identity. this post demonstrates how to use the http action’s built in authentication and token caching for secure, reliable calls. There are many scenarios where you need to call a service that implements oauth 2.0. it has support for roles and claims for instance. out of the box support for oauth 1.0 is really easy and there are many walkthrus on this topic. i will show how to configure a logic app to use oauth 2.0. Set up microsoft entra authentication for calling custom apis from workflows in azure logic apps.
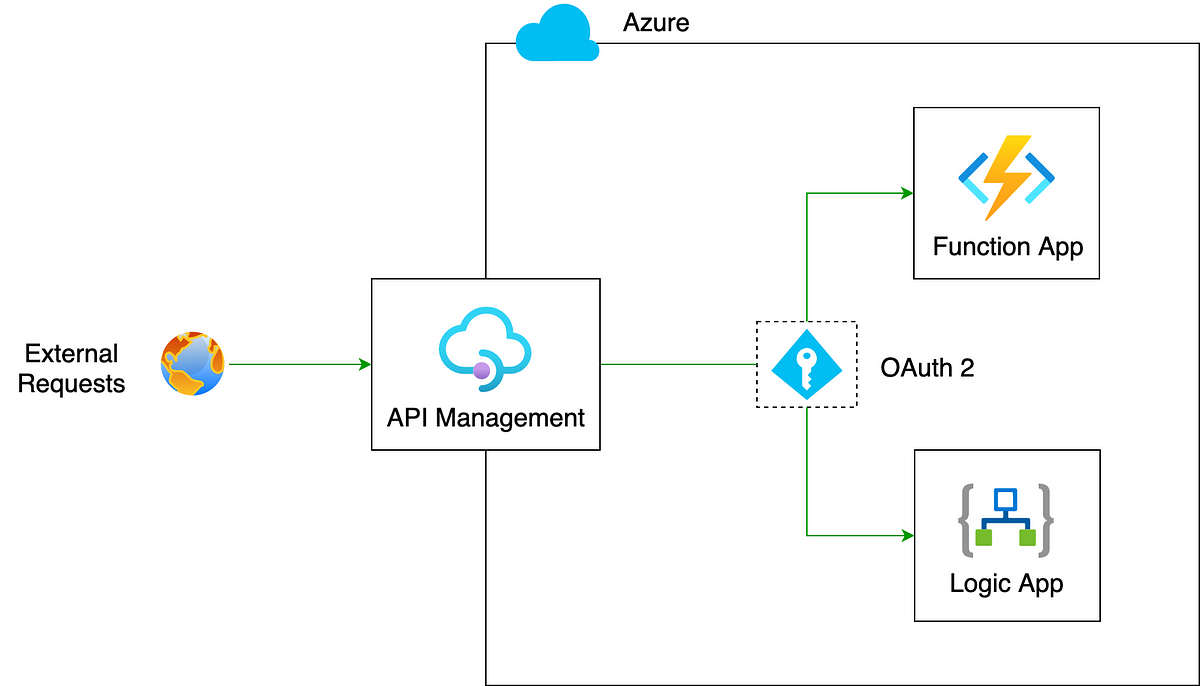
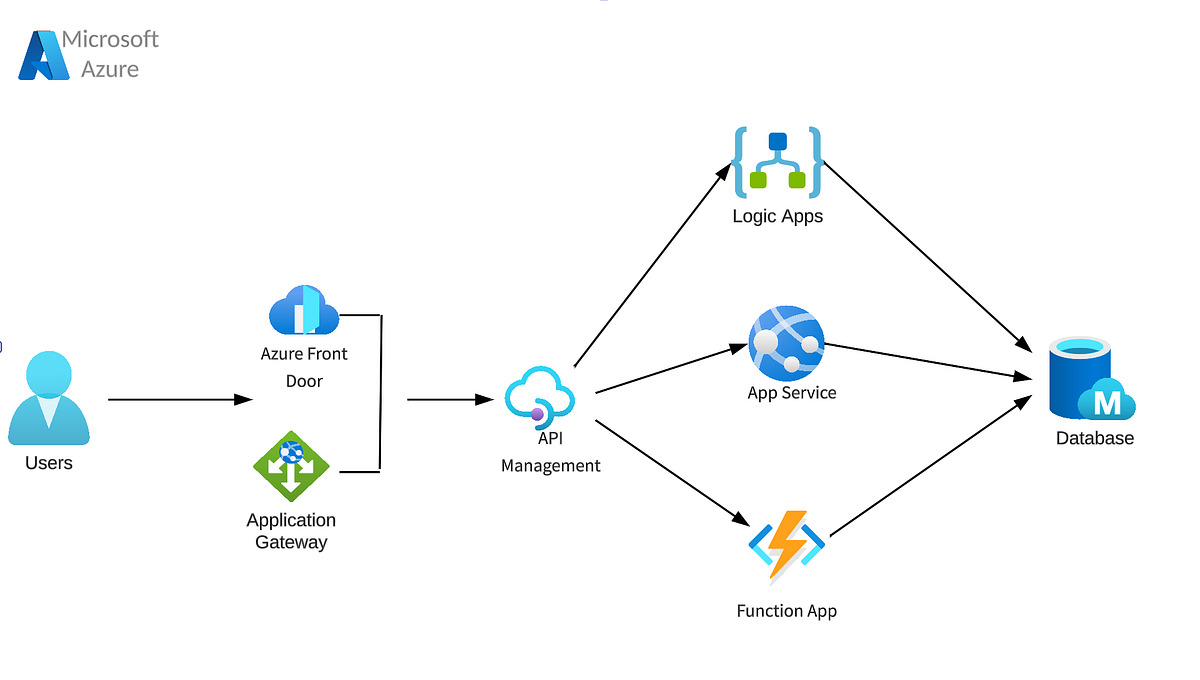
Secure Azure Logic Apps And Function Apps Using Api Management With There are many scenarios where you need to call a service that implements oauth 2.0. it has support for roles and claims for instance. out of the box support for oauth 1.0 is really easy and there are many walkthrus on this topic. i will show how to configure a logic app to use oauth 2.0. Set up microsoft entra authentication for calling custom apis from workflows in azure logic apps. Rather than using sas and passing it as query parameter, we can use more secure and more standardize authorization protocol such as oauth 2.0. In adf, we can now trigger the logic app using a web or webhook activity. for the url, you need to take the logic app url from the trigger, but drop all parameters except the api version. By creating an authtorization policy for your logic app you can use a authorization header with a bearer token and require that the token contains the specified issuer, audience or other claims. showing how that works in detail, and usable scenarios will be the main focus for this blog post. For the url, you need to take the logic app url from the trigger, but drop all parameters except the api version. for the authentication, you can take the system assigned managed identity (no passwords or secrets that can expire) and as resource you specify the audience from the oauth policy.

Secure Azure Logic Apps And Function Apps Using Api Management With Rather than using sas and passing it as query parameter, we can use more secure and more standardize authorization protocol such as oauth 2.0. In adf, we can now trigger the logic app using a web or webhook activity. for the url, you need to take the logic app url from the trigger, but drop all parameters except the api version. By creating an authtorization policy for your logic app you can use a authorization header with a bearer token and require that the token contains the specified issuer, audience or other claims. showing how that works in detail, and usable scenarios will be the main focus for this blog post. For the url, you need to take the logic app url from the trigger, but drop all parameters except the api version. for the authentication, you can take the system assigned managed identity (no passwords or secrets that can expire) and as resource you specify the audience from the oauth policy.
Comments are closed.