Implementing Oauth 2 0 For Java Web Applications Peerdh
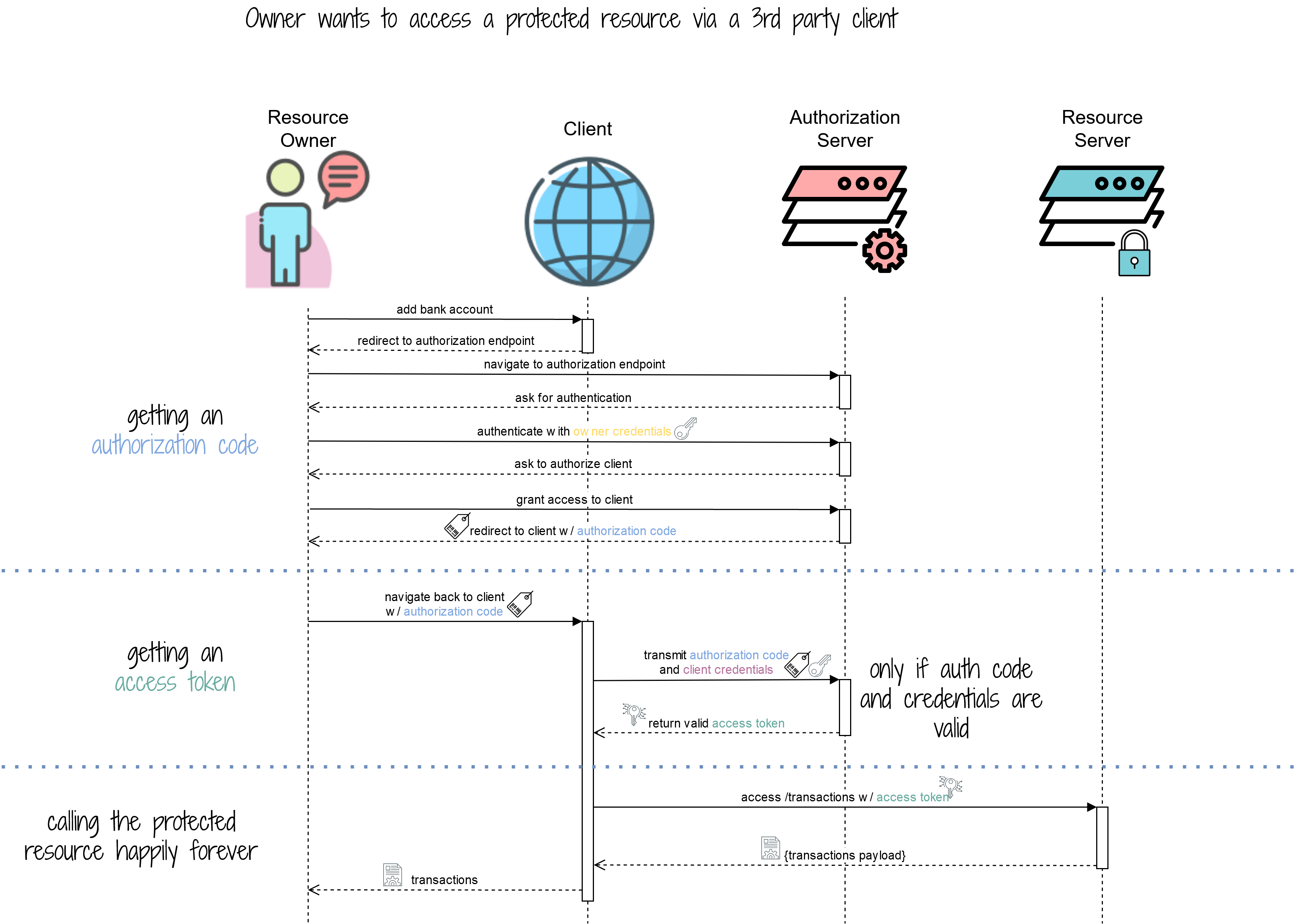
Implementing Oauth 2 0 For Java Web Applications Peerdh Oauth 2.0 has emerged as a popular authorization framework that allows third party applications to access user data without exposing passwords. this article will guide you through implementing oauth 2.0 in java web applications, ensuring your app is both secure and user friendly. This tutorial will walk you through the process of implementing oauth 2.0 authentication in a java based web application. we’ll cover the core concepts, best practices, and common pitfalls, as well as provide step by step implementation guides with code examples.

Implementing Oauth 2 0 In Web Applications Peerdh This article will guide you through the process of integrating oauth 2.0 into your java web application, ensuring that your application is secure and user friendly. It is essential for modern web applications, especially when integrating with third party services. this article will guide you through implementing oauth 2.0 authentication in java applications, providing clear examples and explanations along the way. Oauth 2.0 has emerged as a popular framework for api authentication, providing a robust method for securing access. this article will guide you through implementing oauth 2.0 in your java applications, ensuring that your apis are protected against unauthorized access. One of the most effective ways to secure api access is through oauth 2.0. this protocol allows applications to obtain limited access to user accounts on an http service. in this article, we will look at how to implement oauth 2.0 in a java application, ensuring that your api interactions are secure and efficient.

Implementing Oauth 2 0 Authentication In Java Applications Peerdh Oauth 2.0 has emerged as a popular framework for api authentication, providing a robust method for securing access. this article will guide you through implementing oauth 2.0 in your java applications, ensuring that your apis are protected against unauthorized access. One of the most effective ways to secure api access is through oauth 2.0. this protocol allows applications to obtain limited access to user accounts on an http service. in this article, we will look at how to implement oauth 2.0 in a java application, ensuring that your api interactions are secure and efficient. This article shows an example of implementing the oauth2 authorization framework using java ee and microprofile. Implementing oauth 2.0 in your web application is a powerful way to secure user data and enhance user experience. by following the steps outlined above, you can set up a secure authorization flow that protects your users while allowing them to interact with your application seamlessly. Securing your java applications with robust authentication and authorization can be complex. this guide breaks down implementing oauth 2.0 and openid connect (oidc) using java, demystifying the process. This tutorial focuses on implementing oauth 2.0 and jwt to protect java apis. readers will learn to set up an oauth2 server, generate and validate jwts, and securely integrate these into their applications.
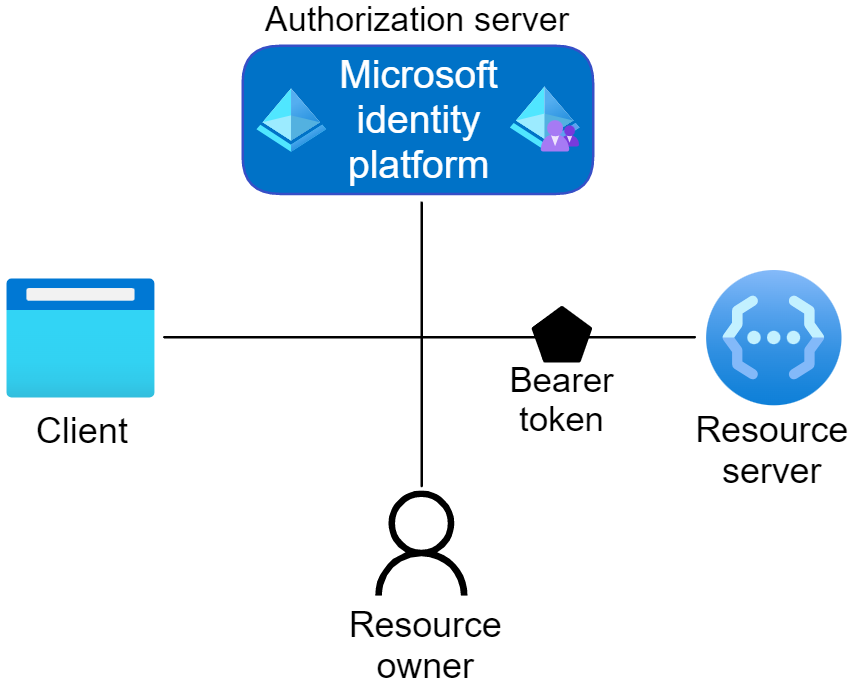
Implementing Oauth 2 0 In A Web Application Using Jwt Tokens Peerdh This article shows an example of implementing the oauth2 authorization framework using java ee and microprofile. Implementing oauth 2.0 in your web application is a powerful way to secure user data and enhance user experience. by following the steps outlined above, you can set up a secure authorization flow that protects your users while allowing them to interact with your application seamlessly. Securing your java applications with robust authentication and authorization can be complex. this guide breaks down implementing oauth 2.0 and openid connect (oidc) using java, demystifying the process. This tutorial focuses on implementing oauth 2.0 and jwt to protect java apis. readers will learn to set up an oauth2 server, generate and validate jwts, and securely integrate these into their applications.

Understanding Oauth 2 0 Key Concepts And Implementation Peerdh Securing your java applications with robust authentication and authorization can be complex. this guide breaks down implementing oauth 2.0 and openid connect (oidc) using java, demystifying the process. This tutorial focuses on implementing oauth 2.0 and jwt to protect java apis. readers will learn to set up an oauth2 server, generate and validate jwts, and securely integrate these into their applications.

Guide To Implementing Oauth 2 0 With Examples
Comments are closed.