Implementing An External Attack Surface Management Program Csa

Implementing An External Attack Surface Management Program Csa Digital transformation, increased adoption of cloud and internet of things (iot), a growing remote workforce, and a technology talent shortage have led to an exponential rise in organizations' attack surface. By implementing an effective attack surface management solution, organizations can enhance their security posture, mitigate risks, and protect sensitive information from potential cyber threats.
Forrester Report Best Practices For Implementing External Attack External attack surface management (easm) is a process to identify, monitor and secure your external facing digital assets from risk and vulnerabilities. This set of steps is specific to the actions of an easm product, however the whole process of attack surface management also includes steps to prioritise and mitigate risks. Learn what easm is, how external attack surface management works, and why it's critical for cybersecurity. discover top solutions & best practices. Over the next few thousand words, we’ll define easm, explore how it works, dig into how it reduces cyber risk, and walk through implementation best practices—all in a tone cisos, it leaders, and tech savvy readers can connect with.
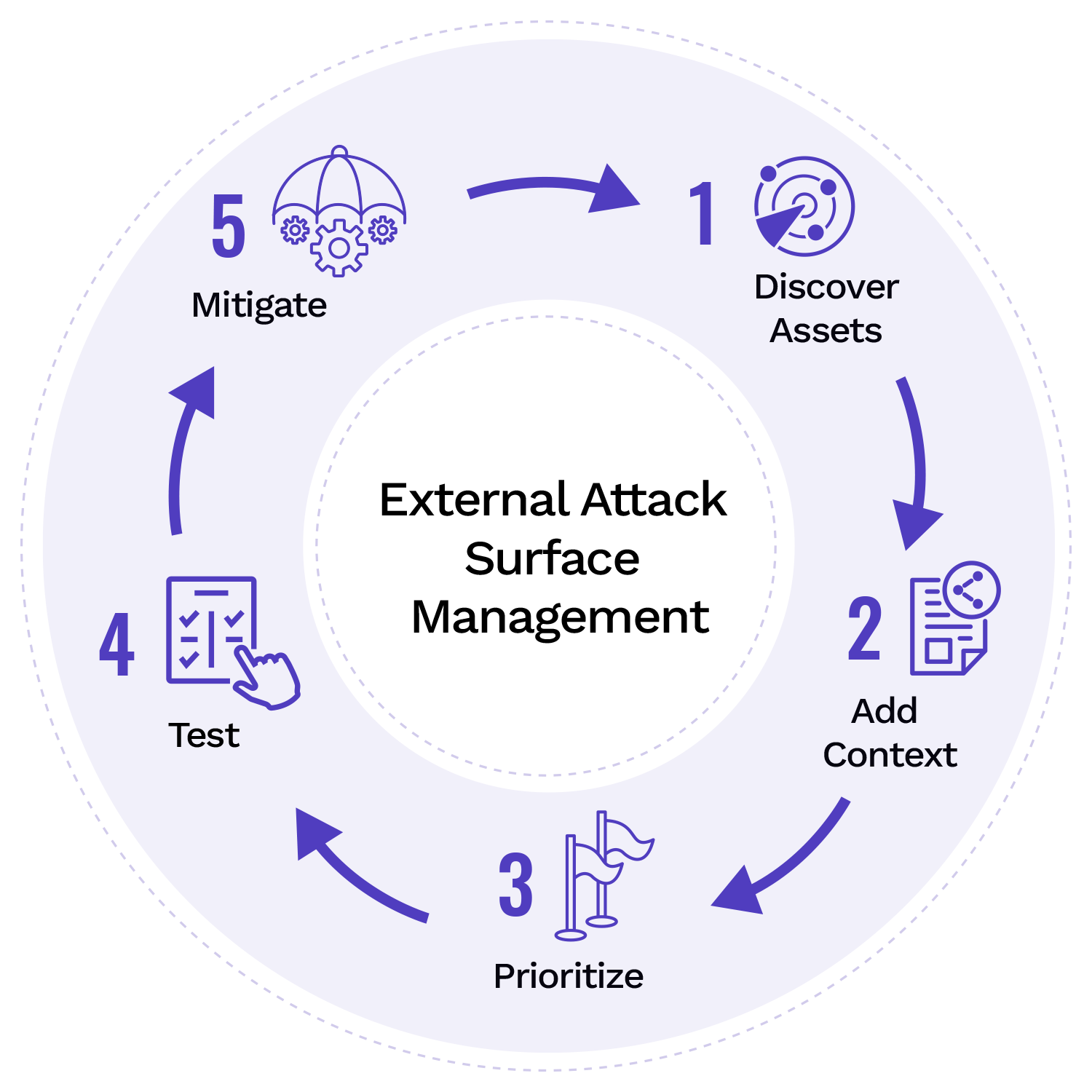
External Attack Surface Management Attaxion Learn what easm is, how external attack surface management works, and why it's critical for cybersecurity. discover top solutions & best practices. Over the next few thousand words, we’ll define easm, explore how it works, dig into how it reduces cyber risk, and walk through implementation best practices—all in a tone cisos, it leaders, and tech savvy readers can connect with. Cyber asset attack surface management (caasm) takes a broader approach by considering both internal and external assets. caasm requires extensive integration work and custom configurations, making it more complex and expensive to implement than easm. Learn what external attack surface management is, how to implement it, and why it’s an essential element of a broader external cybersecurity program. External attack surface management (easm) gives enterprises the external visibility to protect what attackers see first. this article explains how easm tools work, why they matter, and how firemon’s solutions help reduce digital risk. Understanding this attack surface management lifecycle is the foundation for building an effective program. the five phases of the asm lifecycle: discovery — automated identification of all internet facing and internal assets using external scanning, dns enumeration, certificate transparency logs, and cloud api queries.

External Attack Surface Management Buyer S Guide Hadrian Cyber asset attack surface management (caasm) takes a broader approach by considering both internal and external assets. caasm requires extensive integration work and custom configurations, making it more complex and expensive to implement than easm. Learn what external attack surface management is, how to implement it, and why it’s an essential element of a broader external cybersecurity program. External attack surface management (easm) gives enterprises the external visibility to protect what attackers see first. this article explains how easm tools work, why they matter, and how firemon’s solutions help reduce digital risk. Understanding this attack surface management lifecycle is the foundation for building an effective program. the five phases of the asm lifecycle: discovery — automated identification of all internet facing and internal assets using external scanning, dns enumeration, certificate transparency logs, and cloud api queries.
External Attack Surface Management Easm Cycognito External attack surface management (easm) gives enterprises the external visibility to protect what attackers see first. this article explains how easm tools work, why they matter, and how firemon’s solutions help reduce digital risk. Understanding this attack surface management lifecycle is the foundation for building an effective program. the five phases of the asm lifecycle: discovery — automated identification of all internet facing and internal assets using external scanning, dns enumeration, certificate transparency logs, and cloud api queries.
What Is External Attack Surface Management Cognyte
Comments are closed.